There are many, many, many tools on the internet that can "crack", "fish", "bypass" your passwords for anything. Each of these tools is specialized and addresses everything from your operating system password, your wifi password, to your connectionyour with some service.
Learn to protect yourself. These courses are not intended to show you how to do it yourself hacker , but what methods do the hackers and how effective they are.

Lesson 2 - Break a wifi password with WEP encryption within 5 minutes
Before we say anything we inform you that this lesson is 2 and the continuation of the 1 course. Before reading this article please read the 1 course first, so you can understand exactly what we are going to present here today.
Here is a small parenthesis to give you some information about linux. Those familiar with the basic linux functions, in order not to sleep over their keyboard, are asked to skip the following paragraph.
linux is an operating program, like windows, with the only difference being that it is usually free and open source. There used to be peripheral compatibility issues, but not anymore. You should be able to see through linux all your peripherals and cards like cameras, sound cards etc.
The commands accepted by linux are done with two ways, through their home screen icons (as well as in windows) and through the “terminal” which resembles the “Command Line” of Windows. In fact, more actions can be done from the "terminal" than from the icons. After all, you see the "terminal" in a remote connection to a linux box, 90% of which will be done via ssh (ssh = network protocol). It is the "terminal" that is, the remote management for windows.
linux has multiple monitors that can run at the same time but you only see one at a time. Switching is usually done by window-like icons at the bottom right of your screen. So be careful not to accidentally click on a screen other than the one you are working on and then search to find where the open windows that you had a while ago in front of you have gone. ….. :)
Basic linux commands (Debian custom commands):
ls -alt = show what the folder contains in chronological order ps -aux = show which programs and services are now running on the computer . = alternate name of each folder we are at any given time .. = alternate name of a folder behind the current folder we are in at all timesThese, for the time being, slowly and during the lessons we will give you other commands
------
Steps:
- Log in to your router as you see fit and set it to transmit wirelessly with WEP encryption by entering a random 8-digit code,
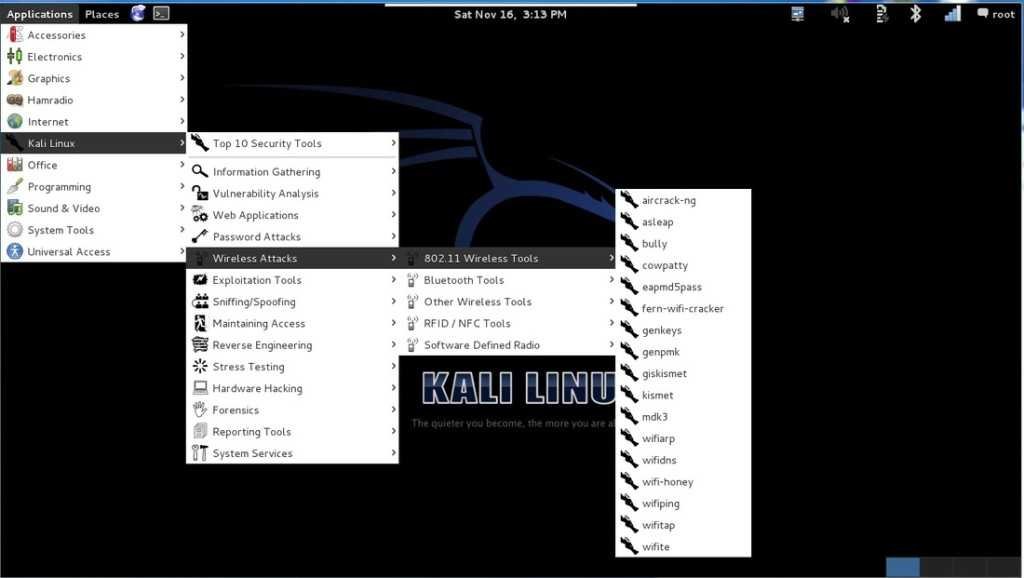
- Having it on our laptop Kali Linux to run as an operating system through the live usb, go with our mouse to the menu program called "fern-wifi-cracker". We find this program in the following path:
Applications> Kali linux> Wireless Attacks> 802.11 Wireless Tools> fern-wifi cracker
3. Normally the program will open with a green wifi antenna signal. On the initial screen of the program press the up-down arrow on “select interface” and select wlan0 ( wlan0 is your wireless network card, eth0 is the wired one. If you do not have a wireless network card then you will not be able to communicate via wifi with your router and therefore you will never be able to break it !!! )
4. Wait until under wlan0 the program writes the message "Monitor Mode Enabled on mon0", close the small window titled "Tips - Scan settings" that will open, by pressing OK, and then press the button "Scan for Access Point”. The message “Initializing” and then “Active” should be written next to the button. The program searches the area for wireless networks. Below you will see how many WEP and how many WPA it has found at any given time.
- When a few seconds of searching have passed and of course next to the WEP button it says that at least one network was found, press the WEP button. In the new window you will see the WEP networks that exist in your neighborhood, including your router. Highlight your router by right clicking on it and press the “Attack” button
- For an 8-digit code, with full signal quality, and with a 4-year-old computer (intel core 2 2.13 Ghz with 4 GB ram) you will need about 3 minutes to see your router's code written in the program, in red letters. Longer passwords will require more waiting minutes but we don't think this is a problem for the hacker next door.
As you can see you are not sure if you put a password on your router with WEP encryption. In fact, it is like saying "Enter me for free, I share a small connection and the door is unlocked, but in order not to be crowded and the lame Maria enters, I put a sign that says no entry."
What does clues mean and how does the program work? fern-wifi-cracker:
ESSID = is the name of the wireless network
BSSID = η mac address address of the wireless network (hexadecimal serial number which is unique to each network device). Remember this parameter, we will need it later
Channel = channel broadcast by the wireless network
Power = Signal level of the network (large number of low signal, small number of better signal)
Encryption = The type of network encryption
The program in question, written in python language, uses to crack – and requires that we already have installed on our computer – the well-known aircrack-ng, and also requests Reaver (for WPS attacks), xterm, subversion, python, etc.
You don't care about these since they already exist in Kali Linux, just know that fern-wifi-cracker makes the life of hackers very easy because it does all the work in a graphical environment where most users are used to seeing.
In short: your neighbor doesn't need to be the ultimate crazy hacker to crack your WEP encryption. With 5 colybograms he knows about linux he can make you a public toilet!!!
Fern-wifi-cracker can break both WPA and WPA2 encryption, but we will prefer to give you the corresponding example through the terminal for learning purposes rather than a graphical environment
So in the next lesson, we'll show you how easy it is to break a wifi connection with WPA and WPA2 encryption, and what format should be the codes we put in our router
Dimitris - iGuRu.gr





