Η published by Der Spiegel we mentioned yesterday, provides some interesting details about NSA hacking capabilities, and the tools used by the Tailored Access Operations (TAO) of the spying service.
Until a few years ago, the NSA used spam, just like most common cybercriminals, to fool their targets and install malicious software στους υπολογιστές τους. Ωστόσο, το spam δεν είναι πια πολύ αποτελεσματικό και έτσι το τμήμα TAO έχει αναπτύξει νέα εργαλεία που ονομάζει "QUANTUMTHEORY."
Documents presented by Der Spiegel show that these tools are particularly effective at targeting online services such as Yahoo, Facebook, Twitter and YouTube.
Apparently, the NSA has not been able to use this method on Google services. On the other hand, the UK secret service GCHQ, which acquired some QUANTUM tools from the NSA, managed to carry out successful attacks on Google services.
Ένα από τα εργαλεία, ονομάστηκε "QUANTUMINSERT," και έχει χρησιμοποιηθεί από την GCHQ για επιθέσεις στη Belgacom, τη βελγική κρατική εταιρεία τηλεπικοινωνιών. Το ίδιο εργαλείο έχει χρησιμοποιηθεί από την NSA κατά του Οργανισμού Πετρελαιοπαραγωγών Χωρών (ΟΠΕΚ) για να αποκτήσουν πρόσβαση σε ευαίσθητες πληροφορίες.
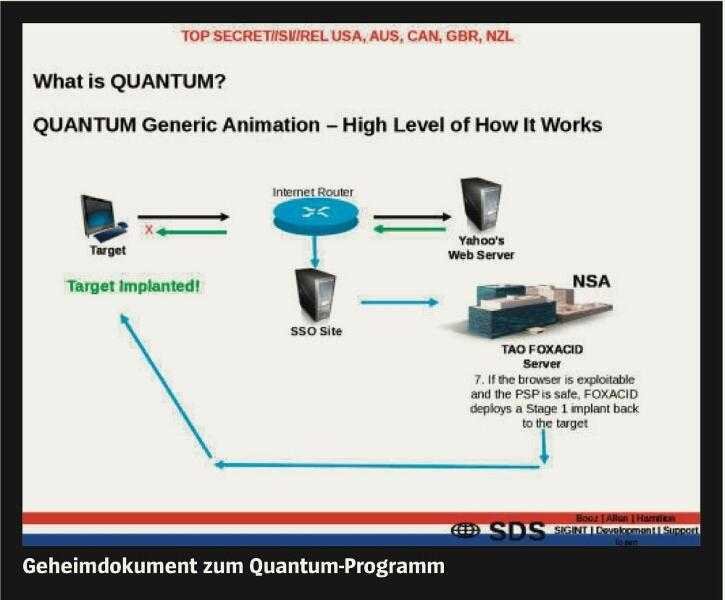
This and other QUANTUM applications are reportedly linked to an NSA shadow network. This network, running parallel to the Internet, is not only composed of NSA computers, but also routers and servers that have been attacked by the secret service.
QUANTUM systems are designed to function automatically based on cookies and other information contained in Internet traffic. When a target or cookie e-mail address is detected, the victim is automatically transferred to covert NSA servers called FOXACID.
In the case of the Belgacom breach, those attempting to visit LinkedIn were automatically redirected to FOXACID where it was loaded malware on their computers. The malware is specially crafted to exploit the vulnerabilities of the targeted device.
Attacks via LinkedIn had a success rate of more than 50%.