Imagine opening a file with WinRAR, και να σας εγκαταστήσει ένα κακόβουλο λογισμικό στο σύστημά σας. Η εφαρμογή WinRAR, ένα ένα ευρέως χρησιμοποιούμενο βοηθητικό πρόγραμμα compression and data decompression. But according to the latest information from THN a flaw allows hackers to distribute malware. A security researcher from Israel, Danor Cohen (An7i) discovered that a feature allows forgery at data which the application compresses. Let's see how.
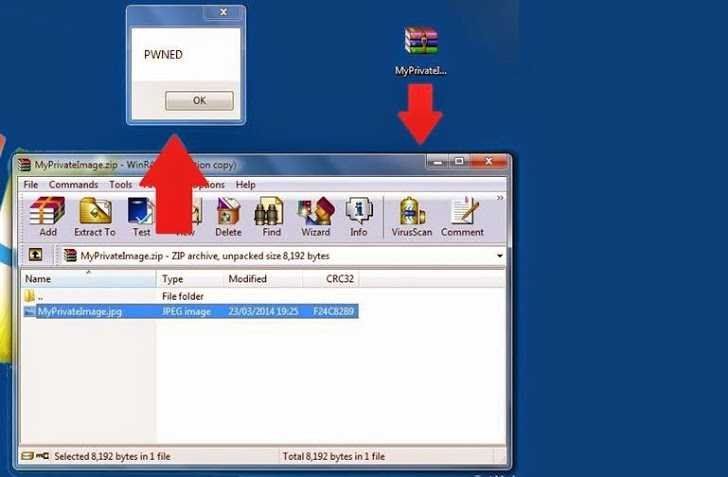
The hacker reports that by modifying a file name and expanding it within the traditional archive, it can hide binary malicious code within a file that represents .jpg, or .txt or any other form.
Using an explwork Hex, analyzed a ZIP file and noticed that the application adds some custom properties to a file, which usually has two name references in the properties. The first name is the original file name (FAX.png) and the second name is again the file name (FAX.png). The file properties are displayed in the WinRAR GUI window.
Danor renamed the file to FAX.EXE and extended the malicious FAX.EXE file to FAX.PNG. After everything is easy, prepare a separate ZIP file, which contained a malware file "FAX.exe", but displayed it as "FAX.png" to the end user.
Η company ασφαλείας IntelCrawler δημοσίευσε επίσης μια έκθεση, η οποία αποκαλύπτει ότι οι κυβερνοεγκληματίες χρησιμοποιούν αυτή τη zero-day ευπάθεια για να στοχεύουν εταιρείες αεροδιαστημικής, Στρατιωτικούς υπεργολάβους, πρεσβείες, καθώς και πολλές άλλες εταιρείες.
Using this technique, an attacker can install any malware in a very convincing way in the systems he chooses.
Danor managed to run it exploit successfully applied to the 4.20 version of the application, but IntelCrawler has confirmed that the vulnerability is compatible with all versions of the popular application including the latest V.5.1.