Several reports show that a hacker who uses alias "xerub" managed to decrypt Apple's Secure Enclave Processor firmware (SEP) and published the decryption key on Thursday.
Secure Enclave Processor (SEP) is a feature on the A7 chipset that powers the iPhone 5, iPad Air, iPad mini 2, and iPad mini 3 as well as any Apple A series processor.
It is capable of managing its functions touch ID, the cryptographic functions of Apple Watch Series 2 smartwatches, passcode verifications accessand other processes related to better safety.
SEP is encrypted by the design and is completely isolated, which means it can not be tampered with.
"THE Processor forwards the data to the Secure Enclave but cannot read it. They are encrypted and authenticated with a session key that is negotiated using the shared device key provided for the Touch ID sensor and Secure Enclave,” Apple says.
The decryption key will not allow hackers to access stored data.
The hacker announced in his Twitter account that he was able to decipher Apple's Secure Enclave Processor (SEP) using the img4lib library, which can deal with img4 files, along with a SEP firmware splitter designed to handle decrypted files.
Both tools were developed by the hacker and are available at GitHub for security researchers wanting to try to decipher Apple's SEP firmware to detect vulnerabilities. However, these tools will not allow them to access the data stored in SEP.
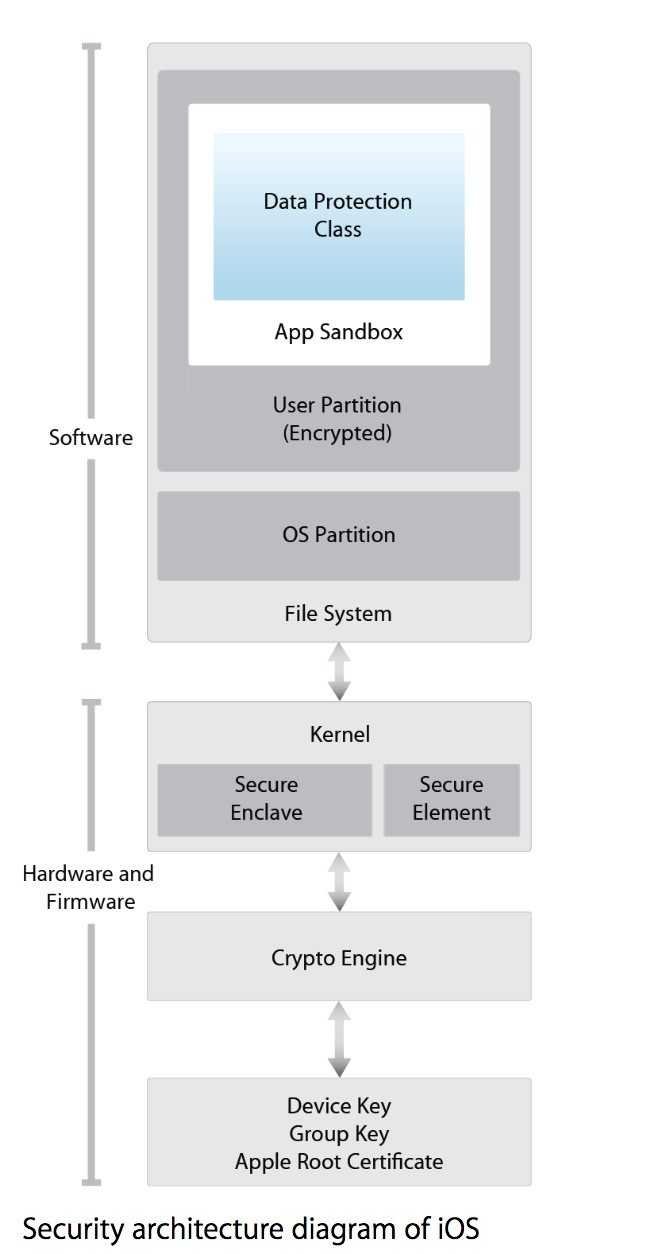
Below you can see the security architecture diagram of Apple's iOS mobile operating system to understand how its security system works. The hacker said the decryption key is "fully deployed" and that you can download the required tools from the links below.
key is fully grown https://t.co/MwN4kb9SQI use https://t.co/I9fLo5Iglh to decrypt and https://t.co/og6tiJHbCu to process
- ~ (@xerub) August 16