The security company Lookout has discovered at least 500 applications Androids that were released through the Google Play Store and had Igexin, a software Development kit. Το SDK επέτρεπε στους απατεώνες να αναπτύξουν κακόβουλα programs to spy on users.
Lookout explains that these apps, whose names it did not disclose, exceeded 100 million downloads on the Google Play Store and belonged to very popular categories such as games aimed at teenagers, weather apps, Internet radios, processors photos, travel apps and emojis.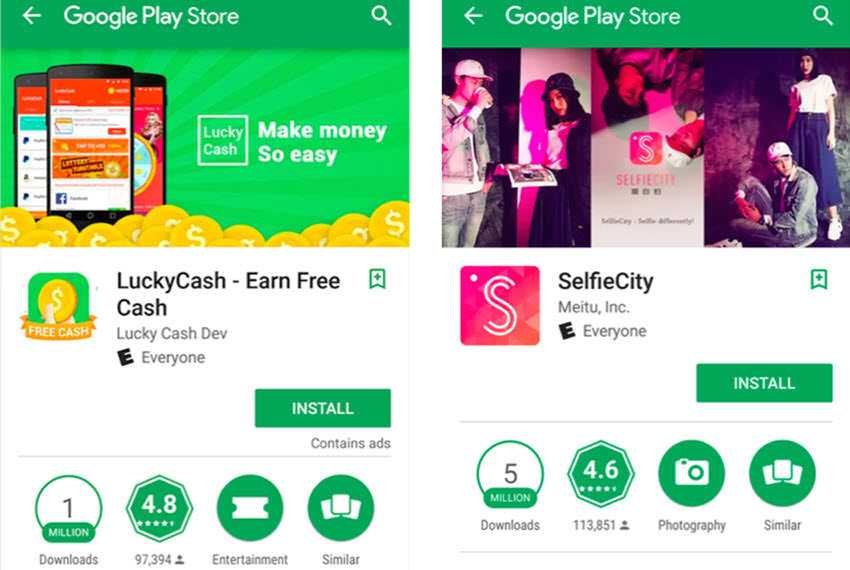
Google seems to have already removed these apps from the Play Store, which means that there is no longer any risk (from this software). Those who have installed apps that look suspicious should scan their devices with a trusted one security software .
Using an SDK to serve malicious applications on Android devices is a new tactic that allows malicious developers to develop malware on phones and tablets using "clean applications."
Lookout reports that the Igexin SDK provides spy capabilities and that developers may not have known it.
“It's likely that many app developers were unaware that their app was leaking personal information from their customers' devices as a result of integrating Igexin's ad SDK. It took a deep analysis of app and SDK behavior by our researchers to make this discovery. THE functionalsecurity is not only obvious, but can be modified at any time from a remote server,” Lookout researchers report.