Someone has reportedly published the purported source code for the iOS bootloader, iBoot, potentially opening a door to hackers and jailbreakers that can help find vulnerabilities in the mobile functional Apple system.
The Motherboard reports that the iBoot source code is from iOS 9 and leaked through GitHub. Although the code is from an earlier version of iOS, its parts are probably the same in the current iOS 11.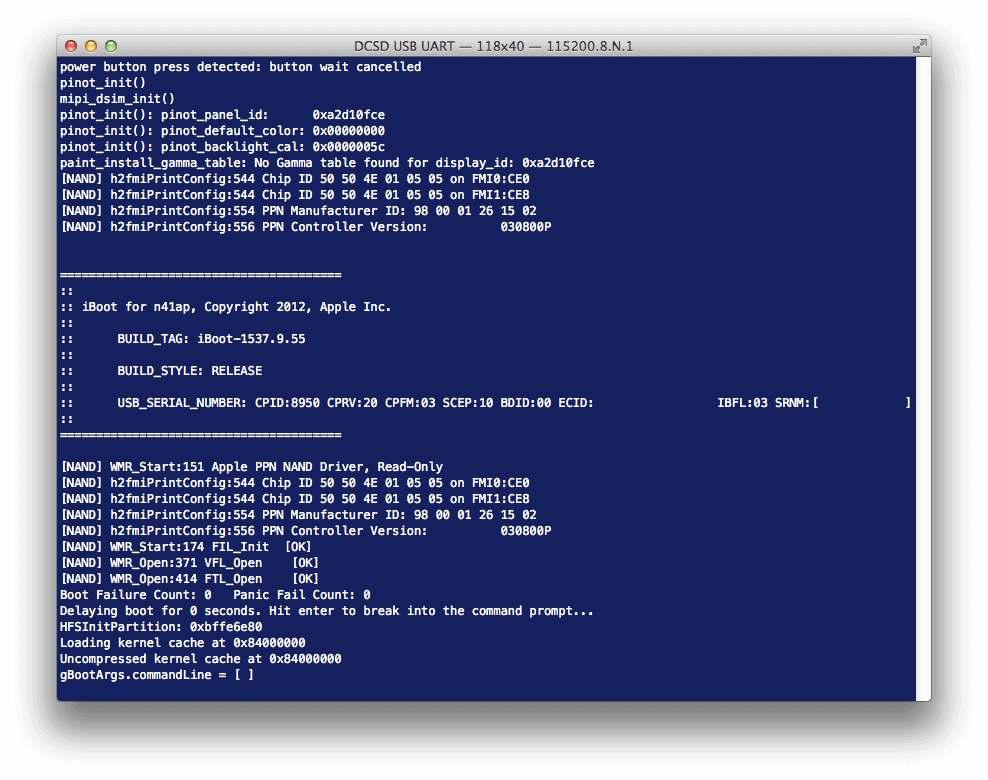
iBoot is a key part of iOS's secure boot chain, a highly sensitive process that runs when a devices iOS.
The secure boot chain ensures that the lower levels of software in the operating system are not altered and only loads the software digitally signed by Apple.
Because of the sensitivity of the feature, Apple also offers the highest reward ($200.000) in the program bug bounty of iOS to researchers which discover vulnerabilities in the boot firmware.
Ο Jonathan Levin, author of several books on iOS and OS X development, said that the iBoot source code appears to be real, as it appears to match the code he had reverse-engineered.
It is currently unknown who leaked the source code on GitHub but it first surfaced four months ago via a Reddit link posted by a user called 'apple_internals'. The leak was originally hosted by Mega and is no longer available.
Of course, Apple is trying to protect its code and so the GitHub page that contained the iBoot source code was replaced with a DMCA notice by an Apple law firm (Kilpatrick Townsend & Stockton). DMCA announcements have also been implemented in over a dozen iBoot cloned repositories.





