Keeper password manager development company was found once more not to care so much about safety. This time, he was using a server that allowed anyone to access and replace archives with malicious content, according to a security researcher.
Chris Vickery, who discovered the exposed server, immediately alerted ZDNet, who attempted to contact Keeper via phone and email on Friday. An hour after disclosure, the server was secured.
However, the director of Aaron Gessner refused any allegations.
The Chicago-based company has a storage server on Amazon S3 to host installers for its various supported platforms.
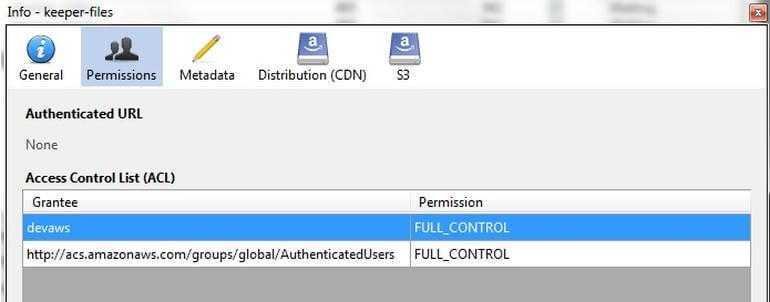
However, the server was not password protected and gave access to anyone and "full control" of its contents (reading, replacing and deleting files).
Many of the files included installers for Windows, Mac, Android, and iPhone. One archive on the server had a private code signing certificate issued by Apple. The certificate can be used to sign the company's iPhone apps, and was issued to Callpod Inc., a company founded by Keeper chief Darren Guccione.
Naturally, a specialized attacker could replace a legitimate iPhone or iPad install program with a malicious file.
Let us mention that its development company applications Keeper recently sued the Ars Technica security researcher, And Goodin, because he posted a vulnerability which he discovered in the browser extension of the Keeper password manager.
Although the company confirmed the vulnerability, it filed a lawsuit against Goodin for allegedly making "false and misleading statements about the Keeper application."
The news caused many reactions in the security community, which criticized the company's response. Many high-level researchers and well-known figures in the community have claimed that such an action will likely have adverse effects on future security investigations and vulnerability disclosures.





