If your computer is infected with Ransomware Thanatos and you are looking for a solution, before you pay a ransom, try a free decryption tool from Cisco Talos to decrypt your files.
Cisco Talos security researchers have discovered a flaw in the Thanatos ransomware code that allows victims to unlock their encrypted files without paying a ransom to the criminals.
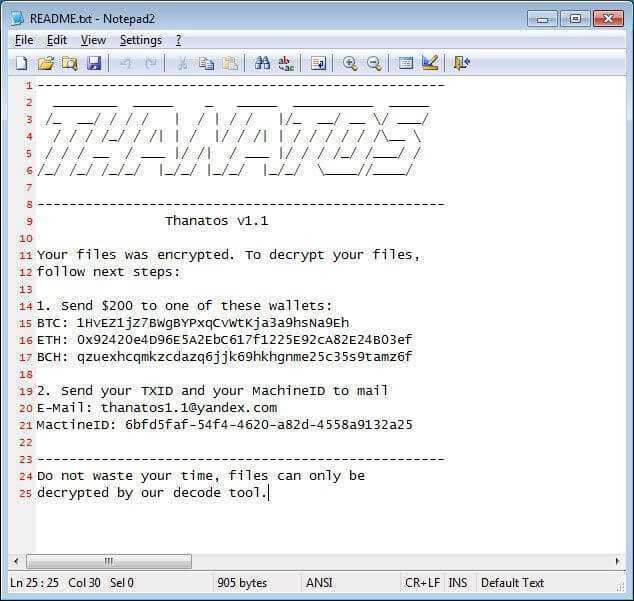
Like all ransomware threats, Thanatos encrypts files and asks its victims to ransom multiple cryptosystems, including Bitcoin Cash (BCH), Zcash (ZEC), Ethereum (ETH) and others, to decrypt their files. Once a computer is infected, all infected encrypted file extensions end up in .THANATOS, and then a ransom note appears, giving instructions on where to send the money to decrypt the files.
However, since Thanatos uses on a tainted system διαφορετικά κλειδιά κρυπτογράφησης για κάθε αρχείο, και χωρίς να τα αποθηκεύει κάπου, είναι αδύνατο για τους προγραμματιστές του κακόβουλου προγράμματος να αποστείλουν τους κωδικούς, ακόμα και αν τα θύματα πληρώνουν τα λύτρα.
Cisco researchers analyzed malware code and found a loophole in the design of the Thanatos file encryption methodology, based on which they developed a free ransomware decryption tool to help victims decrypt their files. It is called Thanatos Decryptor, is completely free, you can download it from GitHub website, and works for versions 1 and 1.1 of Thanatos ransomware
Since the encryption keys used by Thanatos are derived based on the number of milliseconds since the system was last booted, the researchers were able to reverse this logic and recreate the same 32-bit encryption key using a brute force attack and the Event Logs of Windows. For more details about Thanatos ransomware, you can refer in the detailed article published yesterday by Cisco Talos.
To decrypt your encrypted files from Thanatos Ransomware, you need to download Thanatos Decryptor and save it to your desktop. You also need to make sure that you have it installed Microsoft Visual C ++ Redistributable for Visual Studio 2017 otherwise when you try to run Dectyptor you will see an error about missing DLLs.
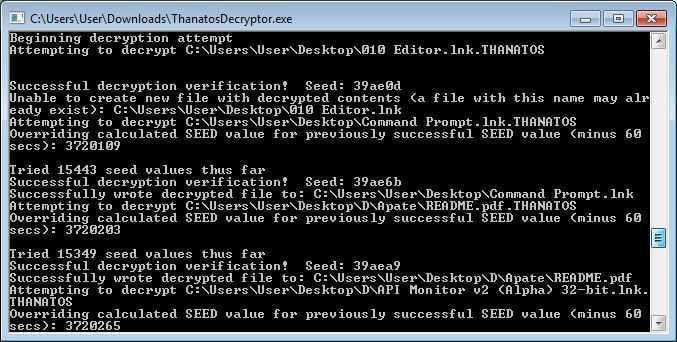
Once you have everything you need, just double click in the executable (exe) file and the decrypter will start looking for files to decrypt. It will only decrypt the following file types:
Image: .gif, .tif, .tiff, .jpg, .jpeg, .png
Video: .mpg, .mpeg, .mp4, .avi
Sound: .wav
Document: .doc, .docx, .xls, .xlsx, .ppt, .pptx, .pdf, .odt, .ods, .odp, .rtf
Other: .zip, .7z, .vmdk, .psd, .lnk
Cisco recommends that you run the decryptor on the same computer where the files were encrypted. The decryption process can take a long time, so be patient.





