The FBI, the Google και 20 τεχνολογικοί οργανισμοί συνεργάστηκαν για να ρίξουν ένα γιγαντιαίο network (3ve) in cyberspace used by criminals to generate fake views and clicks.
For those who don't know what fake clikcs means, it is a method used to deceive advertising networks. The above network has been operating for the past four years and has yielded income million dollars to its creators.
In addition to a concerted intervention to remove network botnets, the US Department of Justice has also announced an indictment against eight suspects believed to be behind the project. Three of them have already been arrested and expected to be released in the United States.
According to a DOJ indictment and a white paper released by Google and the company Cyber-Security White Ops, the eight suspects are believed to be the main operators of the particular fraud scheme believed to have been operating since at least 2014.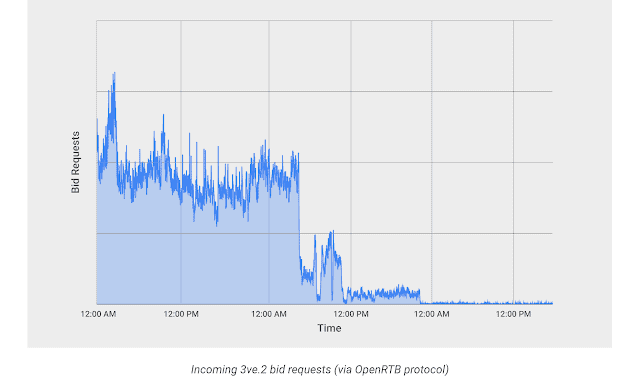
Researchers and the FBI said the administrators used different programs to create ad views and clicks. They used tricks such as hiring other botnets and creating their own botnets hosted on different data centers to hide their true IP addresses. They even created legitimate pages for displaying ads as well as for controlling bots.
According to the FBI, in one of these tricks they used more than 1.900 servers to host MethBot / Miuref / Boaxxe bots.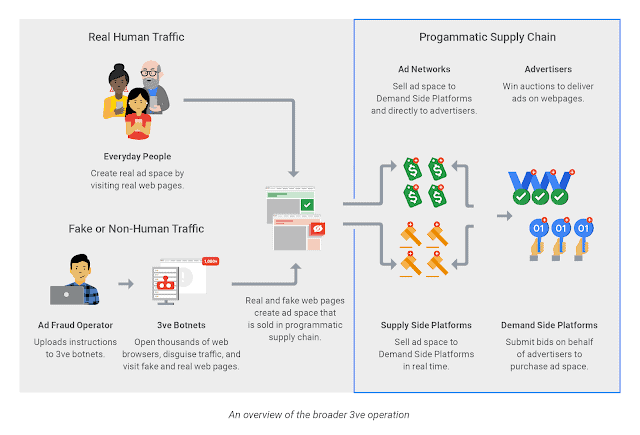
The bots were configured to mimic the traffic coming from both desktops and mobile devices.
Researchers report that gang managed to extend the bot to more than 700.000 computers, infecting them with Kovter malware. The bot has secretly opened browser windows to load websites that have, of course, brought more profits to criminals.
In one publishing on the blog of the company, Google today revealed that it was aware of the features and functions of the bot last year. Google has said that it has assembled a team of big technology names: Microsoft, ESET, Symantec, Proofpoint, Trend Micro, F-Secure, Malwarebytes, CenturyLink, MediaMath, White Ops, Amazon, Adobe, Trade Desk, Oath, The Shadowserver Foundation, and National Cyber-Forensics and Training Alliance.
The names of 8 arrested: Aleksandr Zhukov (38, Russia), Boris Timokhin (39 from Russia), Mikhail Andreev (34 from Russia), Denis Avdeev (40 from Russia), Dmitry Novikov (?? Sergey Ovsyannikov (30 from Kazakhstan), Aleksandr Isaev (31 from Russia), and Yevgeniy Timchenko (30 years from Kazakhstan).
__________________________
- Airfish 8 is flying by Wigetworks
- Debian 9.6: Available the sixth point release of Stretch
- Bitdefender Rescue CD: bootable free for everyone
- Sonar free Microsoft tool for web analytics





