WinPot: Security researchers have discovered one strange malware for an ATM which turns money theft into a slot machine. Yes like these games you find in casinos.
On Tuesday, the security team Kaspersky Labs announced the appearance of WinPot, a malware family that attacks ATMs. The new malware first appeared on underground forums in March 2018.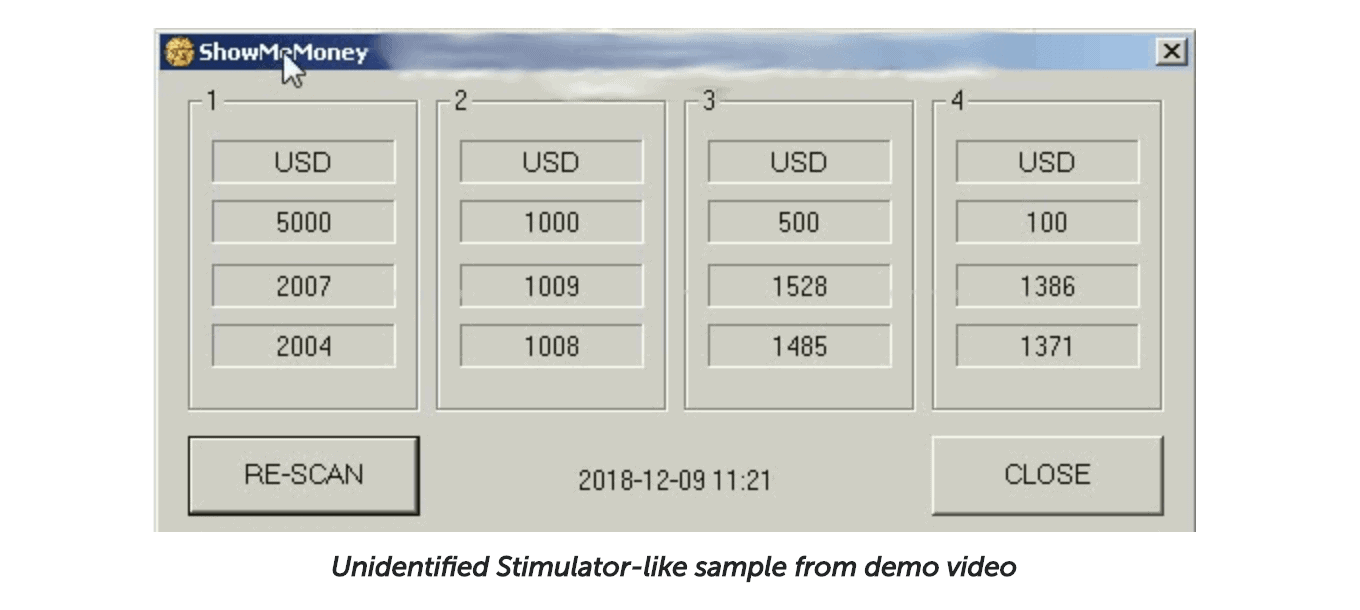
Although simple in its main function, WinPot – internally dubbed by Kaspersky as ATMPot – is designed to hack into the ATMs of a popular companys that manufactures ATMs. After infection it causes the machines to empty their cassettes of all the money they contain.
The appearance of malware is what makes it very unusual, as it looks like a slot machine. 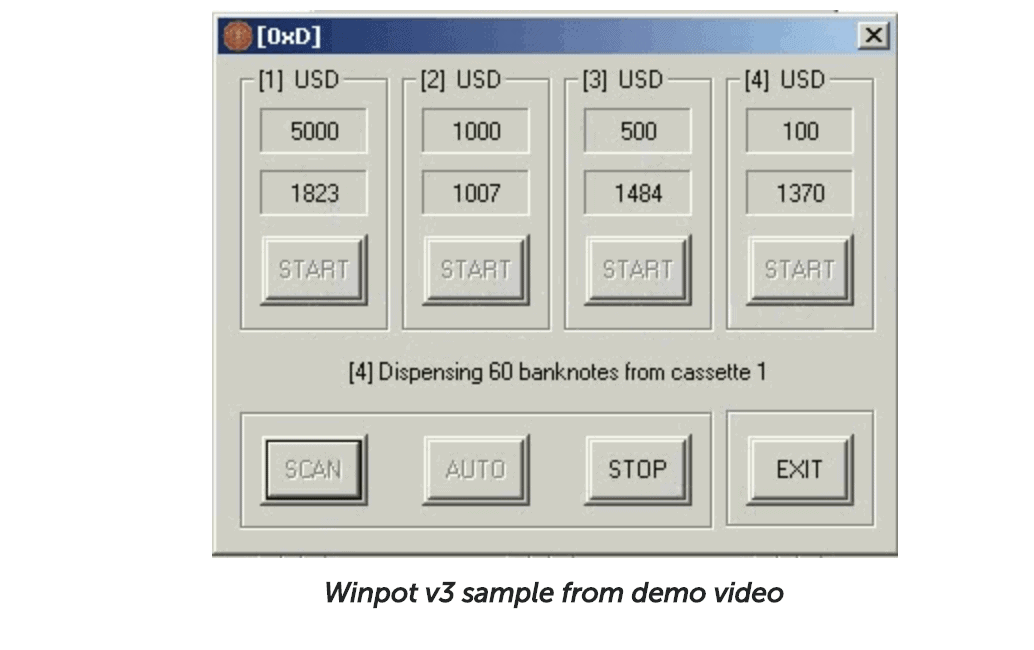
Η screen that the ATM displays includes four reels numbered from 1 to 4.
There is a button with the indication "rotation", which when pressed, begins the redemption of cash. The "stop" button stops withdrawing cash, while the "scan" resets the "game" and re-examines a machine for cash availability. (The stop will probably be the button that will be used less…)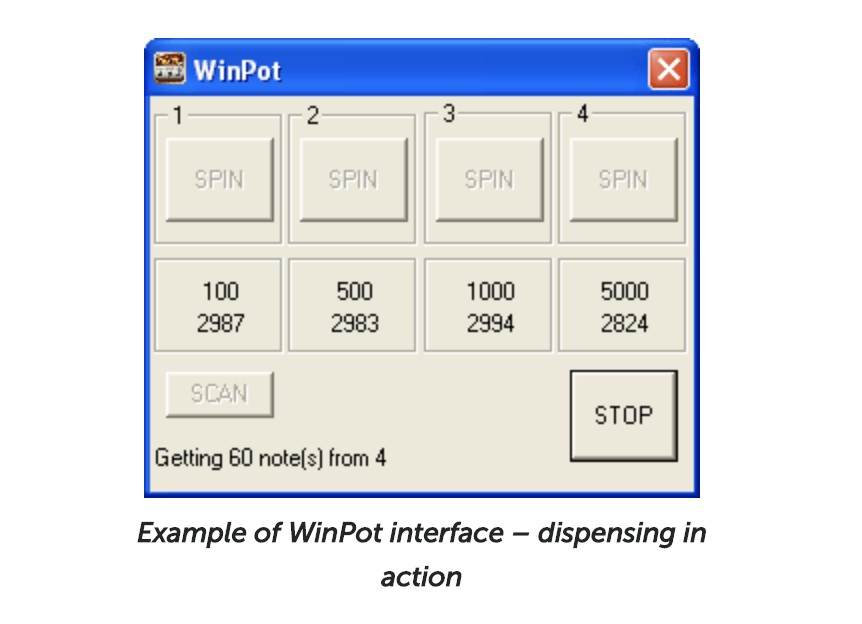
The malware developer on the Dark Web is already advertising WinPot version 3, which also includes a refreshed display and a new feature called "ShowMeMoney."
WinPot shows similarities to Cutlet Maker, a malware that needs to be loaded onto a USB and connected to the ATM through a USB port. Once loaded, the malicious code dismantles the system while a simulator simulates transactions to force the machine to dispense cash.
Kaspersky Lab recognizes WinPot as Backdoor.Win32.ATMPot.gen
______________
- Search Developer finds an ATM error and steals $ 1 million
- Jackpotting: forces ATMs to hurl money
- Kaspersky: nyet in appealing against the US government
- TDSSKiller free Rootkit removal from Kaspersky





