ASUS Live Update Utility: A new advanced persistent threat (APT) detected by Kaspersky Lab in January of 2019 seems to run from June to November of 2018.
The threat is reported to have affected more than one million users who have downloaded data from ASUS Live Update Utility on their computers.
The team Global enviroment Research and Analysis (GReAT) της Kaspersky Lab ονόμασε αυτή την κακόβουλη καμπάνια Operation ShadowHammer και όπως ανέφερε αρχικά ο Kim Zetter, οδήγησε στην λήψη και εγκατάσταση data from a backdoored version of ASUS Live Update over 57.000 users using Kaspersky products (on ASUS computers of course).
While Kaspersky was able to stop most downloads from the trojanized ASUS Live Update, the company's research team estimates that over one million users are infected.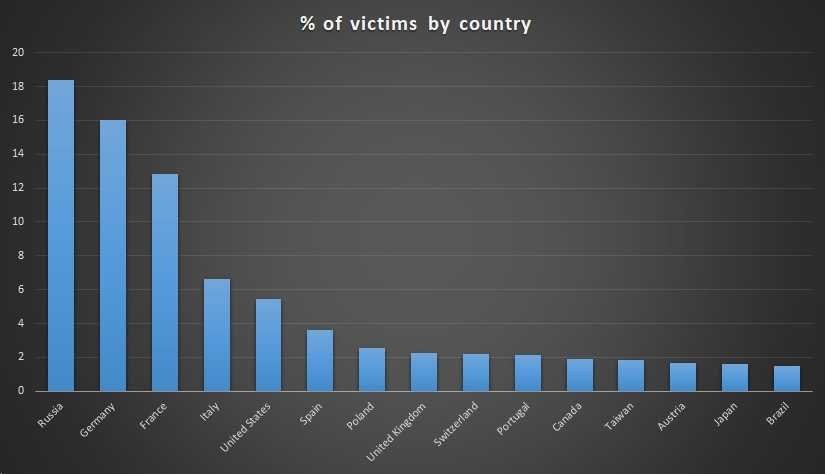
According to GReAT:
ASUS Live Update is a utility that comes pre-installed on most ASUS computers. Used to automatically update certain items such as BIOS, UEFI, drivers and applications
And it continues:
According to Gartner, ASUS was the fifth largest computer company worldwide by 2017. This makes the company an extremely attractive target for APT teams that may want to take advantage of the range of their users.
According to GReAT, there were multiple versions of infected files in the ASUS Live Update that were shared, targeting "unknown groups of users identified by MAC addresses."
The attackers behind the ShadowHammer feature used a hardcoded list of MAC addresses to target the distribution of the malware software. Kaspersky was able to collect more than 600 MAC addresses from 200 malware samples used in this attack.
The researchers Kaspersky also discovered that the infected Live Update was digitally signed with legitimate certificates from “ASUSTeK Computer Inc.” certificates hosted on the official (liveupdate01s.asus[.]com and liveupdate01.asus[.]com) ASUS update servers.
If you're worried about your Asus computer, Kaspersky released one offline application and an online web checkerto check if your systems have been dropped by Operation ShadowHammer.
For testing, we compare your MAC address with the list of hardcoded addresses we discovered in malware.
___________________
- Windows 10 build 18362 on the Slow Ring as a RTM candidate
- Focus Mode by Google: what it is and how to turn it on
- TEDx University of Crete Saturday 6 April 2019





