ESET researchers have analyzed the new tools of the PowerShell-based Turla cyber espionage team. These tools are more resistant to attacks and show improved detection functions of the detection mechanisms.
The famous Advanced Persistent Threat (APT) group, also known as Snake, has recently started using PowerShell scripts, which can directly download and "run" executables archives and malware libraries.
Using PowerShell-based tools, Turla cybercriminals can bypass the detection techniques that are activated when a malicious executable file appears on a disk.
Turla is a well-known cyber espionage team, which stands out for the use of complex malware in its attacks.
Its actions are believed to date back to at least 2008, when US military systems were breached. It is also involved in serious attacks on many government agencies in Europe and the Middle East - including the German Foreign Ministry and the French Army.
Recently, ESET researchers have identified a number of attacks using PowerShell programming scenarios against diplomatic missions in Eastern Europe. "These are probably the same scenarios that Turla uses against other global targets," said ESET researcher Matthieu Faou, who led the study.
ESET researchers have published one article with the results of their analysis of the PowerShell scripts that the Turla team uses to help counter the attacks. "In addition to the new PowerShell loader used by Turla, we discovered and analyzed several interesting payloads, such as a backdoor cuts based on RPC protocol and a PowerShell backdoor, using OneDrive, the service Microsoft cloud storage, as a Command and Control server,” says Faou.
PowerShell loaders, which, when detected, are classified by ESET under the generic name PowerShell / Turla, stand out from the common droppers for their ability to remain in the system, as they regularly load into memory only the built-in executable files.
In some samples, Turla cybercriminals had modified PowerShell scripts to bypass AMSI (Antimalware Scan Interface). This technique, first discovered at the Black Hat Asia 2018 conference, prevents the antimalware product from receiving data from AMSI for scanning.
"However, these techniques do not prevent the detection of real malicious charges in memory," explains Matthieu Faou.
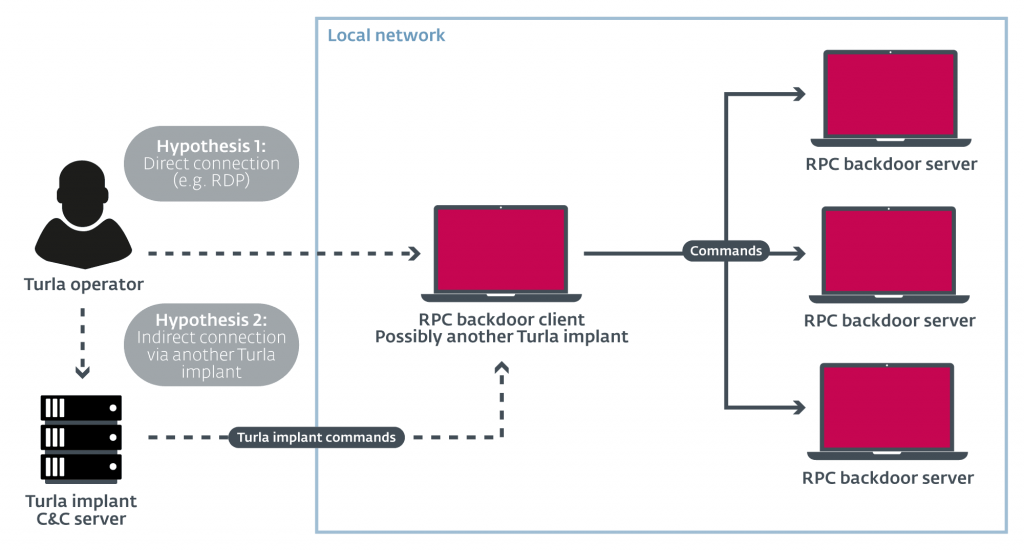
Among the malicious cargoes recently used by Turla, two stand out. One is a whole set of backdoor based RPC protocols. These backdoors are used to perform sideways movement and take control of other machines on the local network without relying on an external C&C server. Also of interest is PowerStallion, a lightweight PowerShell backdoor that uses Microsoft's OneDrive cloud storage service as a Command & Control server.
"We believe that this backdoor is a tool for her recovery accesss in case Turla's main backdoors are removed and cybercriminals can no longer access the compromised computers," comments Matthieu Faou.
ESET researchers continue to closely monitor the APT Turla group as well as other similarly significant groups, investigating their methods, tactics and procedures so that they can help organizations protect networks their.
More details can be found in the relevant article on ESET's blog, WeLiveSecurity.com.
____________________
- Mageia 7 RC with Linux kernel 5.1.5 and KDE Plasma 5.15.4
- Google, WhatsApp, and Apple slap at GCHQ
- The Honda electric car brings the exterior mirrors in





