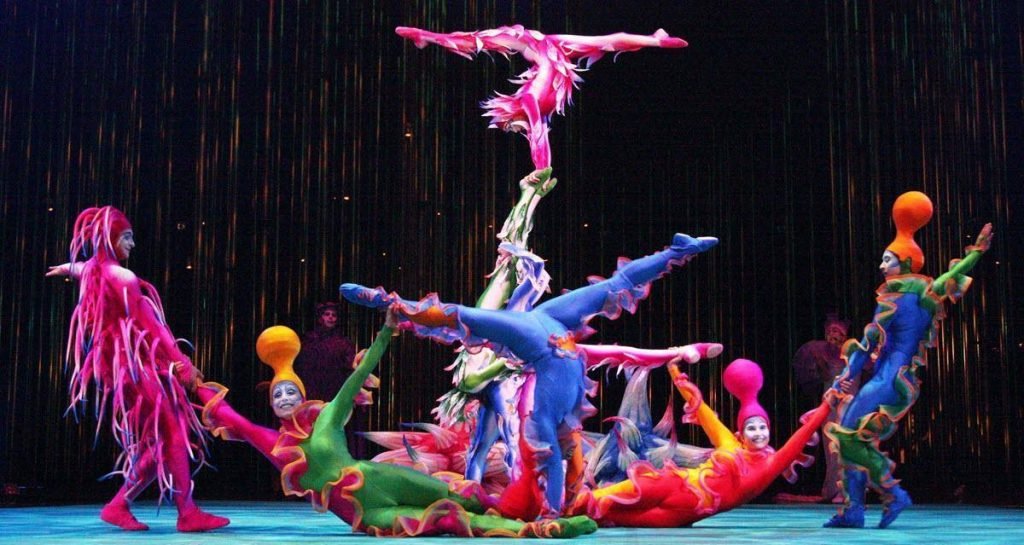
The show "TORUK" by the famous Cirque du Soleil used for advertising purposes an application that made users' mobiles vulnerable. The application, called "TORUK - The First Flight", was designed to enable iOS and Android users to participate in the show through synchronized audiovisual effects created on their mobile phones.
"It seems that the security factor was not taken into account when designing the TORUK application. As a result, anyone connected to the network during the show had the same management capabilities as the Cirque du Soleil administrators, ”explains ESET researcher Lukáš ftefanko, who analyzed the application.
The "TORUK - The First Flight" application has over 100.000 downloads on Google Play, while there is also an iOS version.
With the completion of the "TORUK" performances, the application ceased to be available and the people in charge of Cirque du Soleil stated that they will withdraw it from the official app stores for Android and Apple devices.
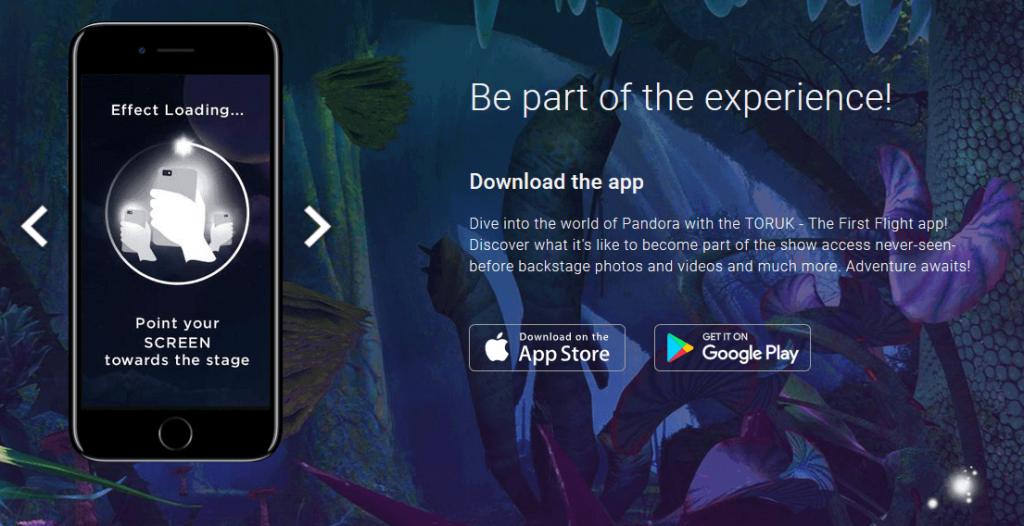
When usesται αυτή η εφαρμογή, ανοίγει μια τοπική θύρα ώστε να είναι δυνατή η απομακρυσμένη αλλαγή των ρυθμίσεων έντασης ήχου, ο localization κοντινών συσκευών Bluetooth (αν είναι ενεργοποιημένη η mode Bluetooth), the display of animation, the setting of the “Like” button for Facebook as well as the participation in shared preferences accessible in the application.
"The problem is that the application does not have an authentication protocol. An expert can scan the network, collect the IP addresses of the devices when the specific port is open (port 6161) and send commands to all devices that use the application ", Štefanko explains.
According to Štefanko, it would be very simple to shield the enforcement against this kind of attack.
If the application created a unique token for each device, it would be impossible for anyone to access all devices massively without authentication testing
After the show, all devices that have this app installed are still vulnerable, so users are at risk of experiencing unpleasant surprises at any time in the future if they are connected to a public network.
"Users who have installed this application must uninstall it immediately. By the way, we recommend that they do this with all applications designed for a specific use ", Štefanko concludes.
More information can be found on this blogpost by Lukáš Štefanko “A great show is now history, as is its insecure mobile devices app” in ESET's Android App Watch.
___________________
- WiFi view the stored codes in Windows
- Pocket Drones for soldiers are being tested in Afghanistan
- Kodachi Linux 6.1 anti forensic anonymous operating





