The researchers of ESET, according to the recent reportssolutions των banking Trojans που πλήττουν τη Λατινική Αμερική, προχώρησαν στην ανατομία του Guildma, του πιο ισχυρού και προηγμένου banking Trojan που είχαν ποτέ συναντήσει από αυτή την ομάδα στη συγκεκριμένη περιοχή.
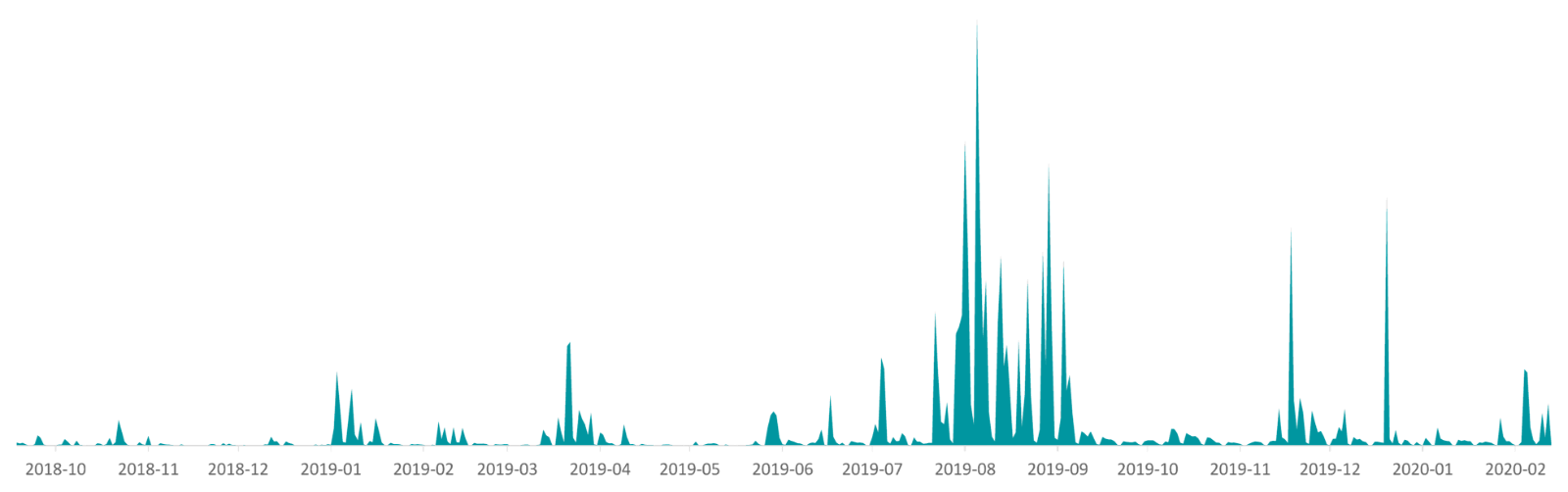
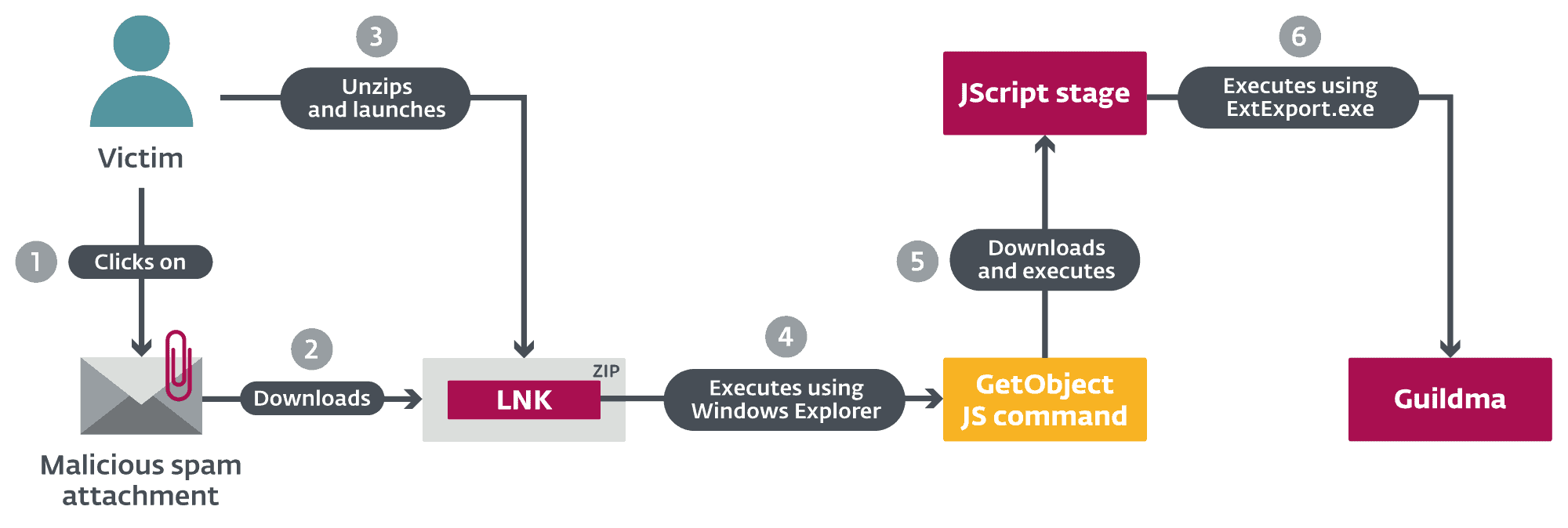
This malicious λογισμικό στοχεύει ειδικά τα τραπεζικά ιδρύματα, προσπαθώντας να κλέψει τα διαπιστευτήρια για λογαριασμούς ηλεκτρονικού ταχυδρομείου, e-shops και υπηρεσίες streaming στη Βραζιλία. Έχει μολύνει τουλάχιστον 10 φορές περισσότερα θύματα συγκριτικά με άλλα banking Trojans της Λατινικής Αμερικής που έχει αναλύσει η ESET. Κατά την περίοδο έξαρσης – μια τεράστια εκστρατεία το 2019 – η ESET είχε καταγράψει έως και 50.000 επιθέσεις την ημέρα. Το Guildma εξαπλώνεται αποκλειστικά μέσω ανεπιθύμητων ηλεκτρονικών μηνυμάτων με κακόβουλα συνημμένα.
In one of its latest releases, Guildma used a new way of distributing command and control servers, abusing profiles in YouTube and Facebook. However, its operators stopped using Facebook almost immediately and, at least at this stage, rely entirely on YouTube.
“Guildma uses very innovative execution methods and sophisticated attack techniques. The actual attack is orchestrated by the C&C server. In this way, its operators can react more flexibly to the countermeasures applied by the banks when they are attacked," explains Robert Šuman, the ESET researcher who leads the team analyzing Guildma.
Guildma has multiple backdoor functions, such as taking screenshots, recording keystrokes, simulating mouse and keyboard functions, blocking shortcuts (such asactivation of Alt + F4, to make it harder for fake windows it may show to disappear), and/or reboot. Furthermore, Guildma has a highly modular architecture, consisting, today, of at least 10 modules. The malware uses tools already on the machine and reuses its own methods. "New techniques are added from time to time, but, for the most part, developers seem to just reuse techniques from older versions," Šuman says.
In one of the first editions of Guildma in 2019, the possibility of targeting institutions (mainly banks) outside Brazil was added. However, in the last 14 months, ESET has not detected any international campaigns outside the country. In fact, the attackers went so far as to block downloads from IP addresses outside Brazil.
Guildma's campaigns slowly escalated until the massive campaign in August 2019, when ESET's Research team recorded up to 50.000 samples per day. This campaign continued for nearly two months, reaching more than double that amount detections that had been observed 10 months before.
The trojan has changed many versions during its development, but there has usually been very little evolution between versions due to its "rigid" architecture.
Guildma has several of the key features of Latin American banking trojans. For more technical details, read the blog post «Guildma: The devil electric drives»On WeLiveSecurity.





