The sharingan is a recon multitool for bug hunters. The purpose of the program is to detect open ports and show us the services running behind them.
![]()
We download and install Sharingan with the following commands:
git clone https://github.com/leobeosab/sharingan
go get github.com/leobeosab/sharingan/cmd/sharingancli
A necessary condition is to already have it in our system Nmap and go.
DNS
Brute force
DNS prevents the target with a wordlist you already have on your system. For example:
sharingancli –target targetname dns –dns-wordlist ~/path/to/wordlist –root-domain target.com
addsubs
Adds subdomains to program through stdin using pipes. For example:
cat subs | sharingancli –target targetname dns addsubs
Scan
Scans all hosts stored on the target using nmap. For example:
sharingancli –target target scan
Interactive
Scans a specific host from the list of subdomains stored in the target. For example:
sharingancli –target target scan interactive
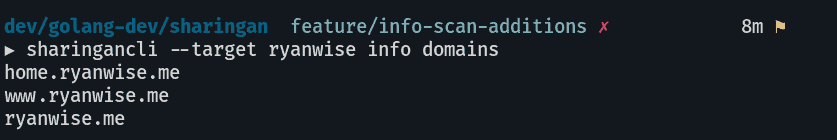
info
Exports all domains as a list to stdout. For example:
sharingancli –target target info domains