WhatWeb recognizes websites. It aims to answer the question, “What is this site?”. Recognizes technologies ιστού, συμπεριλαμβανομένων συστημάτων διαχείρισης περιεχομένου (CMS), πλατφόρμες blogging, statistics / analytics packages, JavaScript libraries, web servers and embedded devices.
WhatWeb has over 1700 plugins, each to recognize something different. WhatWeb also identifies version numbers, email addresses, account IDs, web framework modules, SQL errors, and more.
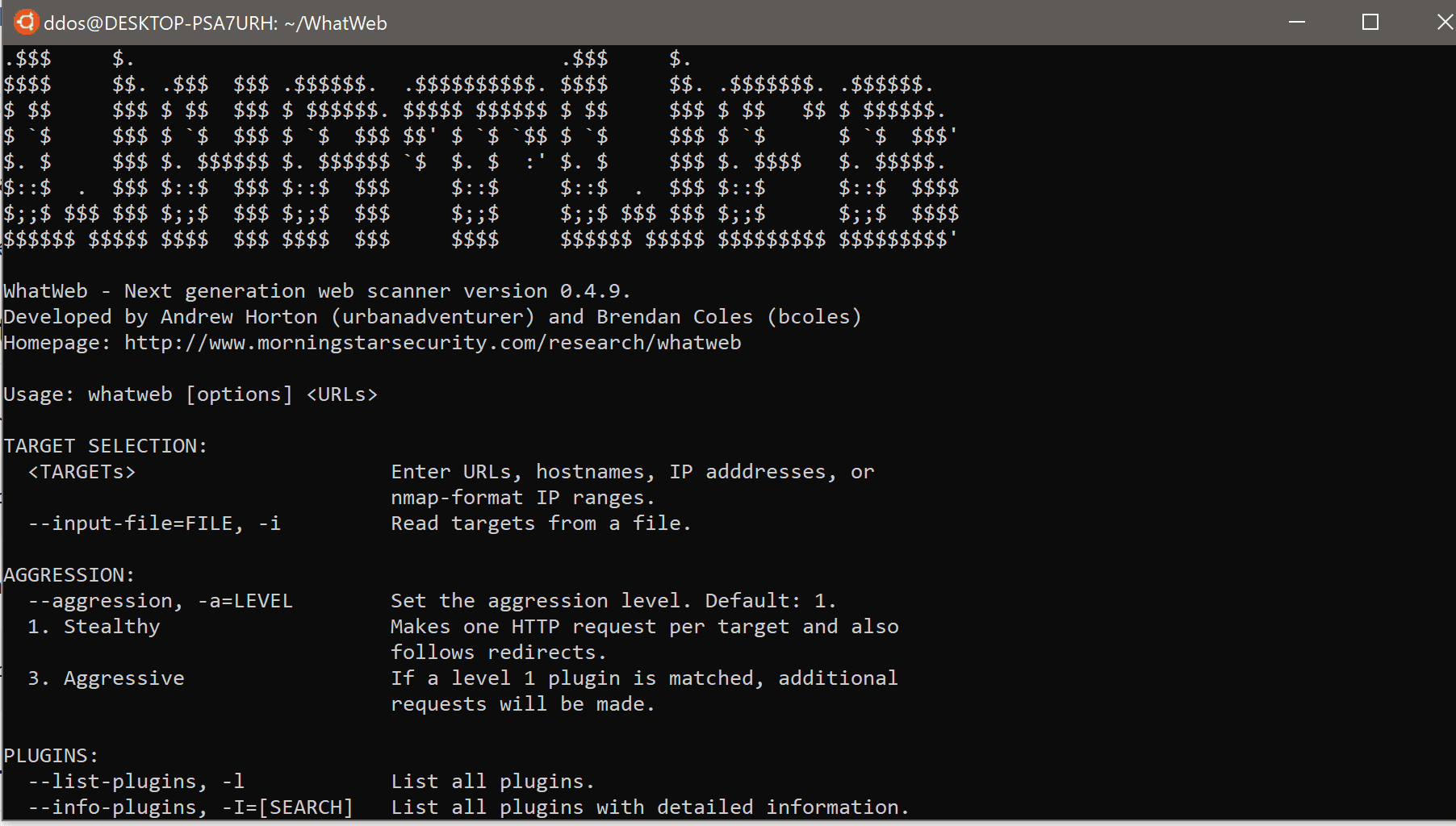
WhatWeb can be stealthy and fast, or deep but slow. When you visit a website with your browser, the exchange data includes lots of tips on what web technologies power this site.
Sometimes a single web visit contains enough information to identify a site, but when it does not, WhatWeb can further search the site. The default level of aggression, called "stealthy", is the fastest and requires only one HTTP request from a site. More aggressive ways of using it in penetration testing have been developed.
Οι περισσότερες προσθήκες WhatWeb είναι διεξοδικές και αναγνωρίζουν μια σειρά από ενδείξεις από λεπτές έως προφανείς. Για παράδειγμα, οι περισσότεροι ιστότοποι WordPress μπορούν να αναγνωριστούν με την ετικέτα μετα-HTML, π.χ. ” ', αλλά μια μειοψηφία ιστότοπων WordPress καταργεί αυτήν την ετικέτα αναγνώρισης, αλλά αυτό δεν εμποδίζει το WhatWeb.
The WordPress WhatWeb plugin has over 15 trials, which include favicon checking, default installation files, login pages, and "/ wp-content /" checking in related links.
Specifications
- Over 1800 plugins
- Check the balance between speed / privacy and reliability
- Performance coordination. Check how many sites are scanning at the same time.
- Multiple logging formats: Brief (greppable), Verbose (human readable), XML, JSON, MagicTree, RubyObject, MongoDB, ElasticSearch, SQL.
- Proxy support in TOR
- Custom HTTP headers
- Basic control HTTP identity
- Web redirect control
- Range from IP address
- Fuzzy matching
- Result of awareness of certainty
- Custom plugins are defined in the command line
- IDN (International Domain Name) Support
Installation
sudo apt-get install ruby ruby-dev libopenssl-ruby
sudo gem install bson
sudo gem install bson_ext
sudo gem install mongo
sudo gem install rchardet
git clone https://github.com/urbanadventurer/WhatWeb.git
You will find a user guide for the program here.





