Saferwall is one platform open source malware analysis.

It has the following goals:
- Provides a collaborative platform for sample sharing between malware researchers.
- Acts as a system expert to help researchers create an automated malware analysis report.
- Analyzes the platform to find new malware.
- Quality assurance for pre-release signature.
Specifications
- Static analysis:
- Crypto hashes, identification deviceς
- Export of Strings
- Portable executable file analysis program
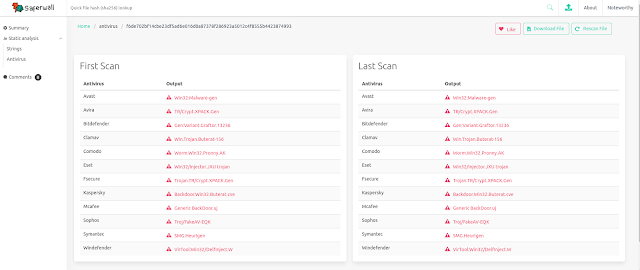
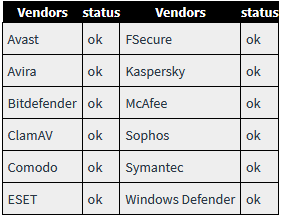
- Multiple AV scanner including major vendors protectionfrom viruses:
Installation
Saferwall takes advantage of kubernetes for its high availability, scalability and huge system behind it.
Everything runs inside the Kubernetes. You can either deploy it in the cloud or host it yourself.
To facilitate the operation of a Kubernetes cluster, you can use since . It automatically provides a suite of kubernetes hosted on AWS, GCE, DigitalOcean or OpenStack but also on dedicated servers. Currently only AWS is officially supported.
Steps for development in AWS:
- Clone the project: git clone https://github.com/saferwall/saferwall
- Using linux debian, make sure the build-essentials are installed with: sudo apt-get install build-essential.
- Rename envna .env and fill in the AVS codes you have.
- Install the make saferwall.
- Edit deployments / values.yaml to suit your needs.
- archives elasticsearch log:
Project architecture
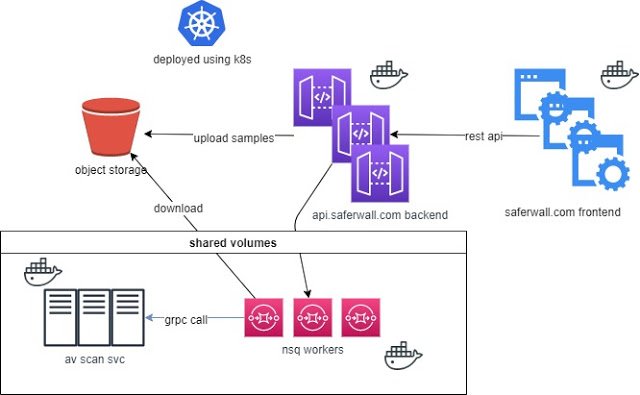
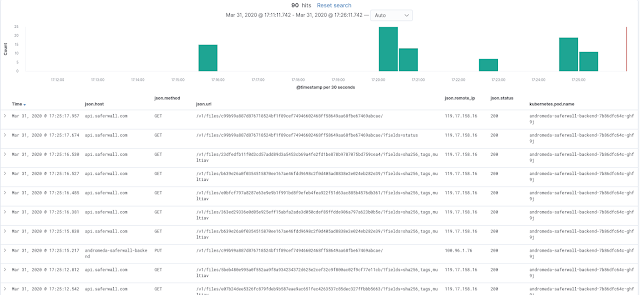
Here is a basic workflow that occurs when scanning a file:
- The frontend communicates with the backend via REST APIs.
- Backend uploads samples to storage.
- Backend promotes one message in the scan queue.
- The consumer retrieves the file and copies it to the shared nfs, avoiding sampling it in any container.
- Consumers call scanning services asynchronously (such as AV scanners) via gRPC calls and wait for results.
You can download the program from here.





