BOtB is a container analysis and utilization tool designed for use by computer engineers, while at the same time being CI / CD friendly with their common technologies.
Contents
hide
Mode
BOtB is a CLI tool that allows you to:
- Take advantage of common container vulnerabilities
- Perform joint actions after operating the containers
- Enable when certain tools or binaries are not available in the container
- Use them possibilities of BOtB with CI / CD technologies to test the development of the container
- Perform the above in either manual or automated approach
Specifications
- Find and identify the UNIX domain slots
- Identify the UNIX domain hosts that support HTTP
- Find and recognize the Docker Daemon in UNIX domain slots or on an interface
- Analyze and locate sensitive strings in ENV and edit it in ProcFS, ie / Proc / {pid} / Environ
- Identify the endpoints of the services of metadata, e.g. http://169.254.169.254, http://metadata.google.internal/ and http://100.100.100.200/
- Perform a container breakout via CVE-2019-5736
- Binary territory files with custom payload
- Perform operations in CI / CD mode and return only output codes> 0
- Find metadata information from GCP endpoints
- Upload data to S3
- Force BOtB to always return an output code 0 (useful for non-blocking CI / CD)
- Perform the above from CLI arguments or from a YAML configuration file
- Perform a reverse DNS lookup
- Identify the secrets of Kubernetes service accounts and try to use them
Use
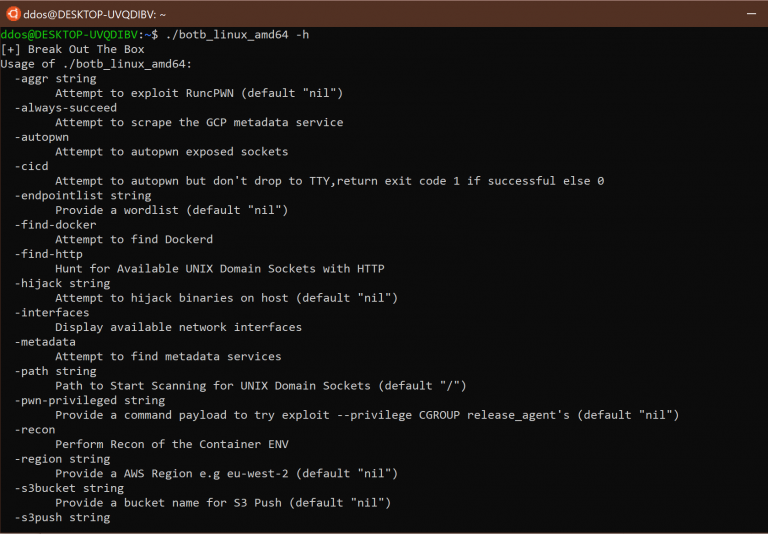
Instructions on how to use the program, you will find here.
You can download the program from here.





