Garmin finally managed to obtain the decryption key to recover its files that were encrypted after a WastedLocker attack Ransomware.
On July 23, 2020, Garmin ceased operations worldwide and its customers could not access Garmin Connect, flyGarmin, Strava, inReach services.
The attackers demanded $ 10 million from the company to give them a decryption key.
After a four-day hiatus, Garmin suddenly announced that services were being restored, leading many to suspect that it had paid a ransom to obtain the decryption keys. However, the company declined to comment.
Today, BleepingComputer gained access in a package created by Garmin IT department to decrypt a workstation and then install security software on the machine.
WastedLocker is one ransomware business-oriented and has no weaknesses in the encryption algorithm. This means that there is no free cryptographer.
So in order to obtain a decryption function key, Garmin must have paid the ransom to the attackers. It is not known how much they paid.
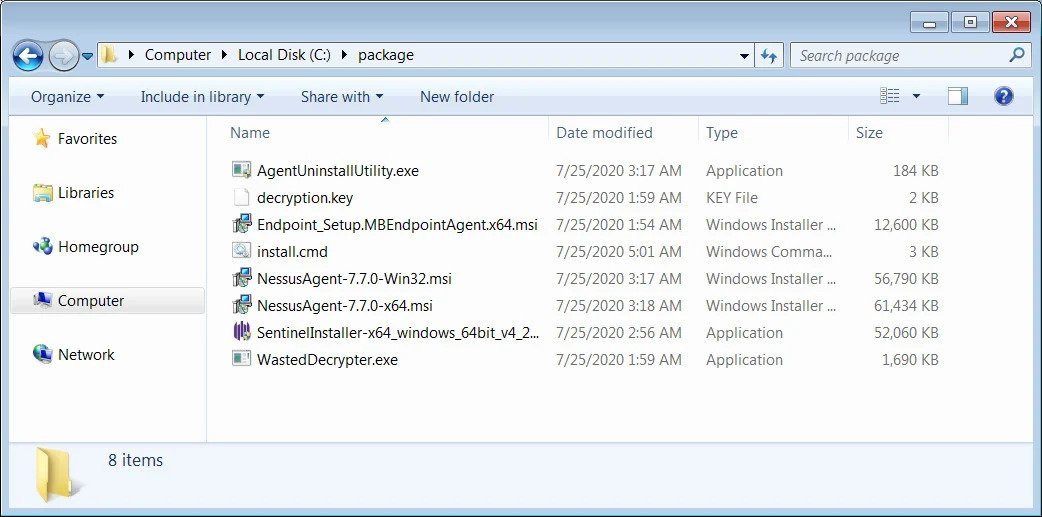
The recovery package acquired by BleepingComputer includes various security software installers, a decryption key, a decoder for WastedLocker, and a script that can run all of the above.
The script contains a time signalnsi25/07/2020', which shows that the ransom was paid on 24 or 25 July.
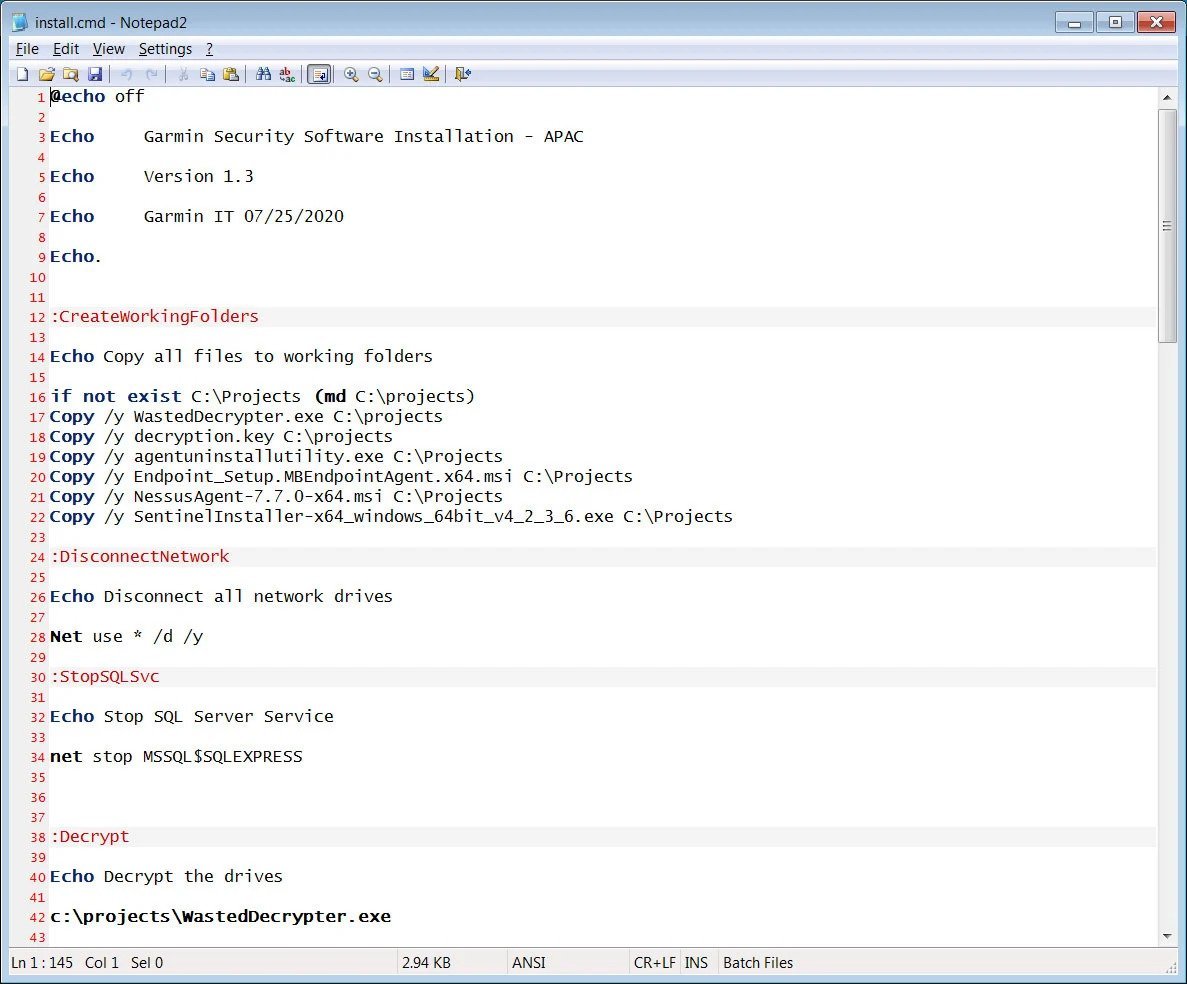
The cryptographer included in the package contains references to both the cybersecurity company Emsisoft as well as in the company supply ransomware trading services, Coveware.
When BleepingComputer contacted Coveware, they said they did not comment on ransomware reported in the media.
A similar answer was given by Emsisoft, which stated that it could not comment, but that they create decryption tools and are not involved in ransom payments.
Emsisoft usually creates custom ransomware decryptors when the tools provided by the attackers contain errors or if companies are concerned that they may contain backdoors.
“If the ransom has been paid, but the decryptor provided by the attacker is slow or faulty, we can extract the decryption code and create a custom solution that decrypts up to 50% faster with less risk of damage or loss data,” Emsisoft reports on a page of.





