AMIRA is a service for automatic analysis of OSXCollector files. Automated analysis is performed via OSXCollector output filters.
More specifically, with One Filter to Rule Them All. AMIRA takes care of retrieving the output files from an S3 bucket, running the analysis filter, and then uploading the analysis results back to the S3.

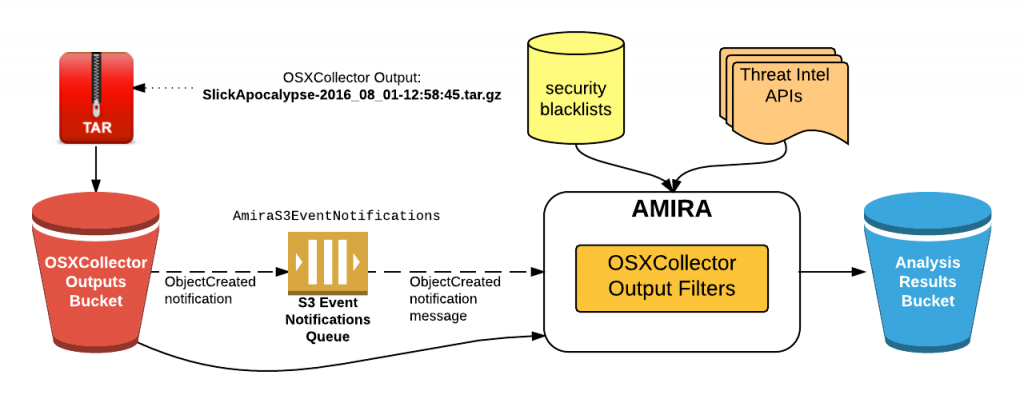
Architecture
The service uses S3 bucket event alerts to enable resolution. You will need to configure an S3 bucket for the OSXCollector output files so that when a file is added there, the notification will be sent to a series of SQS (AmiraS3EventNotifications in the image below).
AMIRA periodically checks the order for any new messages and when downloaded will get the OSXCollector output file from the S3 bucket. It will then run the analysis filter on the recovered file.
The analysis filter performs all of them sequentially filters contained in packet φίλτρων εξόδου OSXCollector. Ορισμένα από αυτά επικοινωνούν με εξωτερικούς πόρους, όπως τα hashes και χρησιμοποιούν μηχανές απειλών Intel API, π.χ. VirusTotal, OpenDNS Investigate or ShadowServer.
The initial output of OSXCollector extends with all this information and the last filter run by the analysis filter summarizes all the findings in human-readable form. Once the filter is complete, the analysis results will be loaded into the S3 results analysis bucket
Information about the installation as well as the use of the prelettertos, you will find here.





