This is the first time you have read such a common title and you usually expect to find some "secret" and unknown tricks in the text of the articles, but the truth is that the road to safety is smooth and smooth.
The difficult thing is for a large enough percentage of users to eliminate incorrect opinions - myths and unproven theories and to understand that they must follow appropriate solutions so as not to offer their computer as tool malicious activities.
Below you will read 9 tips that are not always emphasized or approached with a different perspective / argument.
1) Download Windows isos only from official Microsoft links. A reliable tool that facilitates the λήψη is Windows-ISO-Downloader (url=https://www.heidoc.net/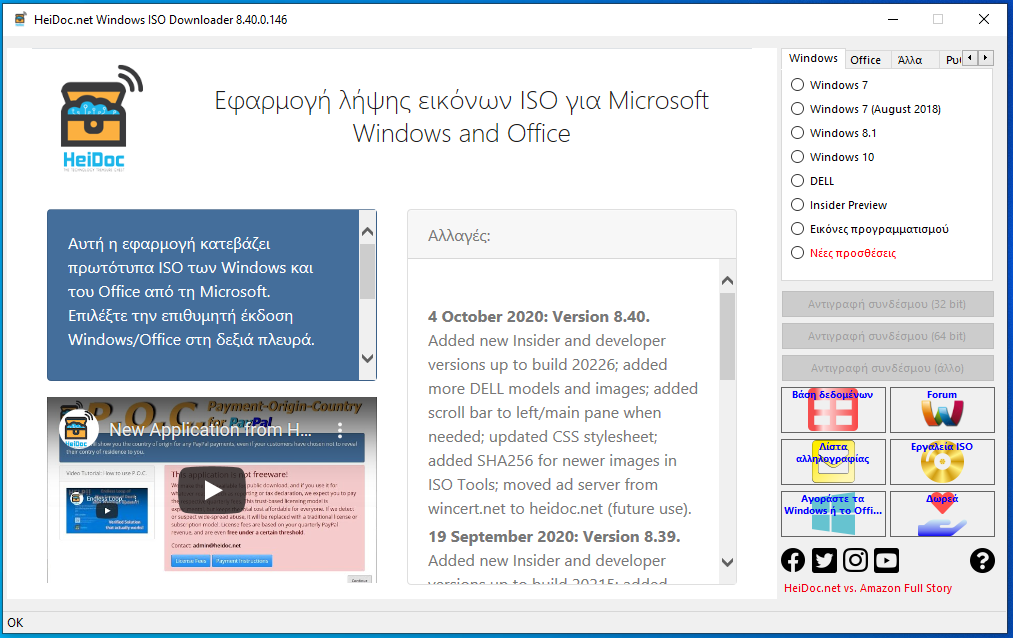
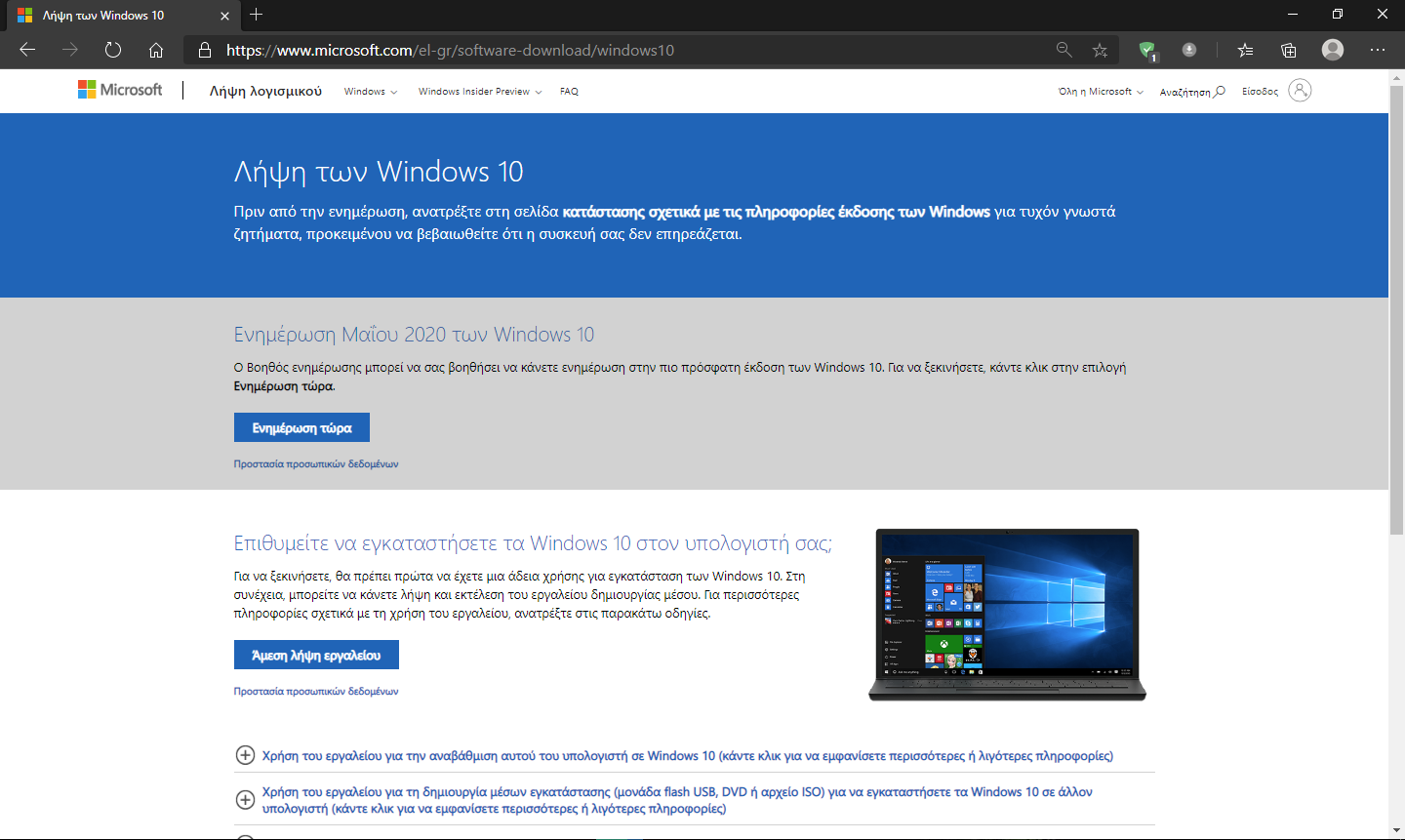
Because for this software we rely on the good choice of its creators, if we need Windows 10 we follow the following link:
https://www.microsoft.com/el-
Modified isos from torrents and warez sites with pre-installed applications and "enhancements" can offer us a zombie computer with tragic consequences for our privacy and network security.
Also buy activation keys and avoid online kms activators.
2) Drivers: we only download from the official website of the manufacturers. A dll contained in a driver from an unknown site can be malicious and digitally signed so that it is not detected by an antivirus.
3) Trust the manufacturer/developer of the product that usest. If you're of the opinion that you shouldn't trust Microsoft, then just use someone else functional. There is no reason to disable updates because "it damages some people" or "it once destroyed (sic) my computer". Provided that not you use beta / Release Preview the cases to "destroy" your computer are as many times as you have had so far.
Let us be responsible: we always keep our operating system up to date to protect ourselves from the new threats that are constantly appearing. An antivirus does not always protect against vulnerabilities exploiting vulnerabilities.
And these security vulnerabilities are not always "wrong" of the MS programmers, but functions that serve some needs such as device interconnection, for which the way was found to be exploited maliciously (so additional controls are inserted).
At the following link we can get an idea of Microsoft's update policy
https://docs.microsoft.com/el-
If the version of Windows is old (1903,1909) then you can upgrade to the latest one (2004 and any other):
Detailed Windows 10 upgrade guide
4) Antivirus / firewall: following the above, always install free or trial versions from the developers' pages. We never experiment with "trial reset", "activation patch". Trust it https://www.av-test.org/en/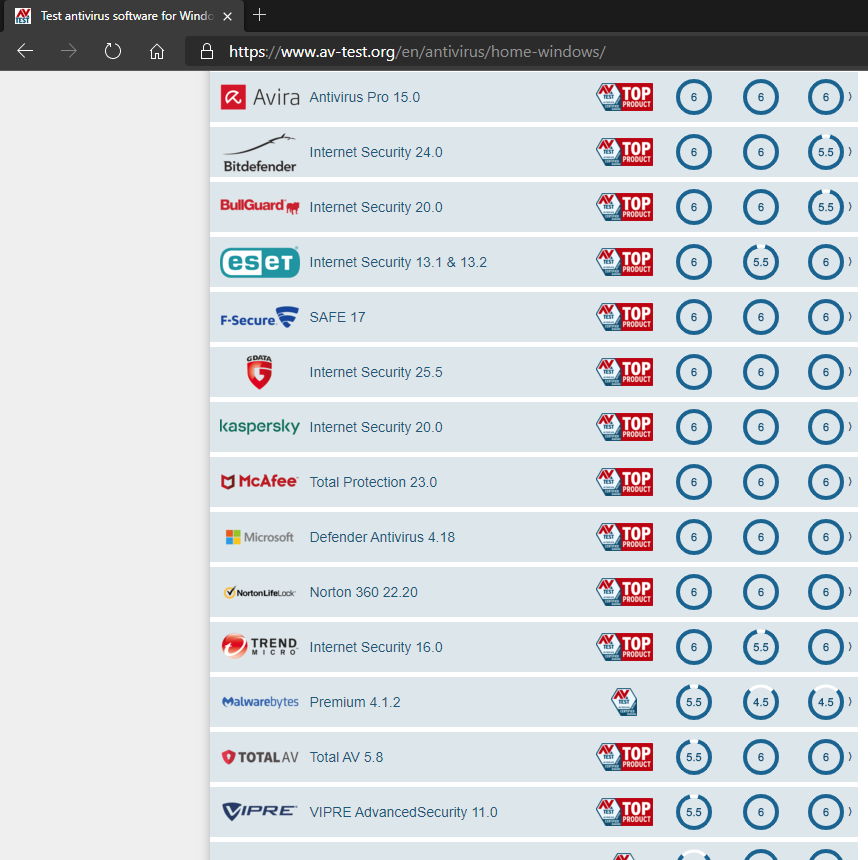
5) Protect your network. Many consider changing the password on Wifi a security step. But the most important thing they miss: change the default (factory) code of your modem-router! There is no network that does not break, but the main thing is not to give "on the plate" access to your router, the most important of all! Re-read “Six ways to secure your router"
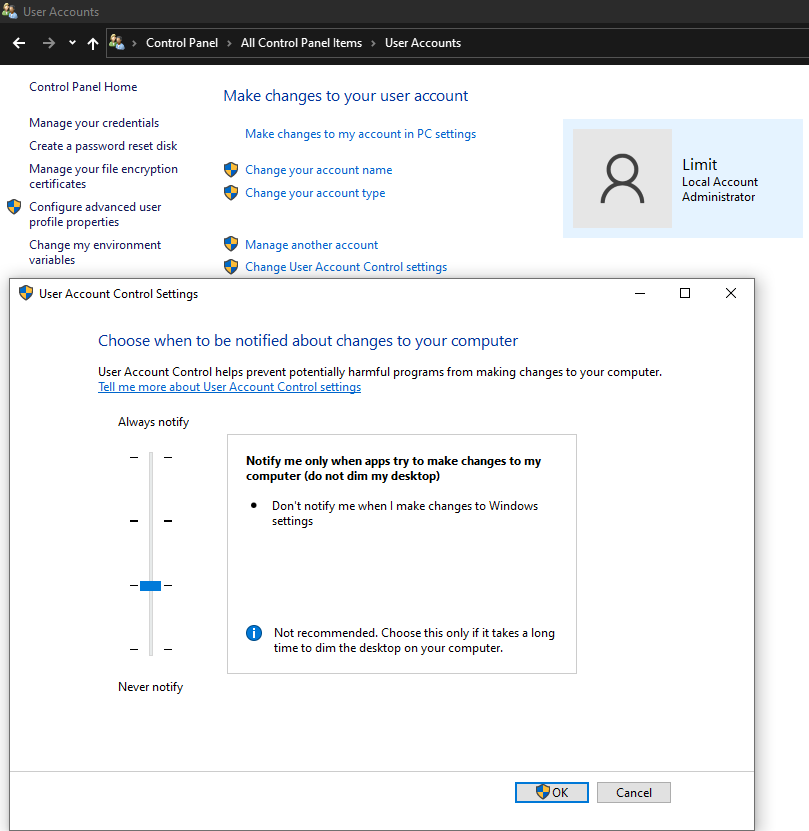
6) Enter a password on your computer. If you are a user with administrator privileges, enter a password that is easy to remember. The password requirement is a security step against unattended malicious installations (as they will not be complete without the user credentials). Do not turn off user control, leave it at the lowest level to let you know about significant changes to your system and to run programs
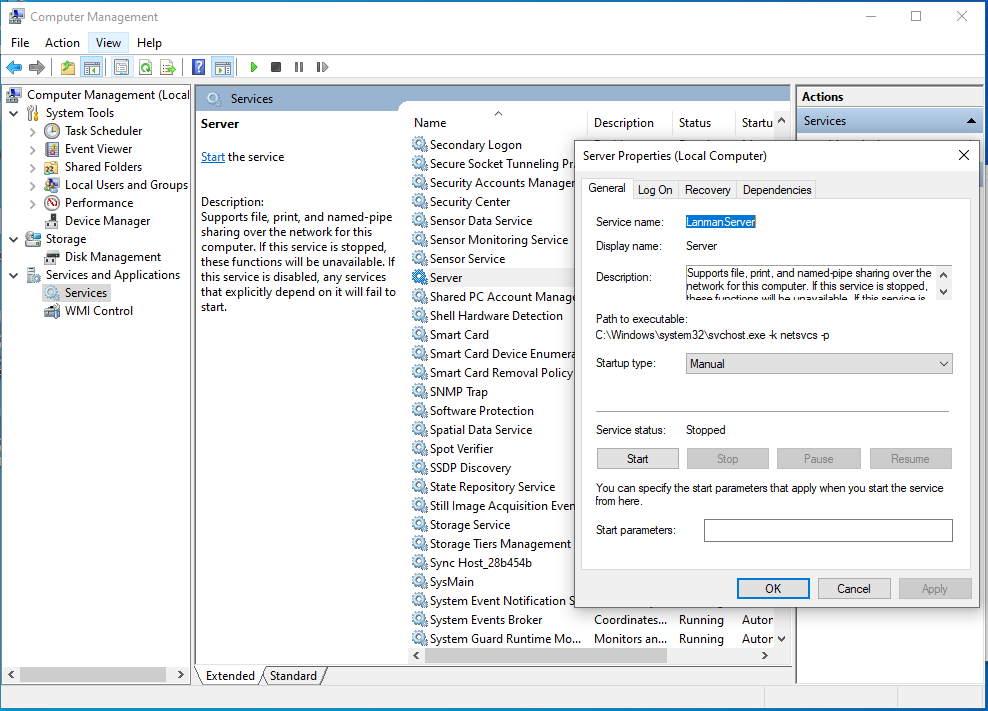
7) Disable administrator shares: Windows shares some system folders that can be accessed and maliciously accessed. There are two ways to turn it off:
-In the registry at HKEY_LOCAL_MACHINE \ SYSTEM \
In the system services we deactivate or set the Server service in the Manual, if our computer is not in a local network. A guide to system services is here
8) Do not install broken programs. Everything that is downloaded from warez sites, check them with the antivirus. Do not warn with prompts "it is not a trojan but it will incorrectly recognize the antivirus - add it to the exceptions" and "disable the antivirus before installing it".
Most patches, dll, exe and keygen are dangerous for your computer security. One solution is to have two Windows installations in different partitions or disks, where you will use one for your tests without using your navigation and sensitive passwords.
9)Use a browser supported by large teams of developers. There are three on the list:
- Chrome supported by Google
- Firefox supported by Mozilla Corporation
- Edge Chromium supported by Microsoft.
This ensures that you have a product that is always up-to-date against widespread threats and in line with European privacy requirements.
Avoid using browsers from countries that do not respect privacy (eg China) and there is no detailed reference in the Security Policy.
A simple example of how a browser can be used for cyber attacks is for an organization to gather information about which operating systems users are using and if they have vulnerabilities (eg Windows 7) to be selected for attacks.
One of the biggest hacks that targeted millions of users was in 2018 when they took advantage of Opera Sync and stole users' passwords.
He also wants a lot of attention to the extensions that you install, because you give them the right to access the websites you visit.
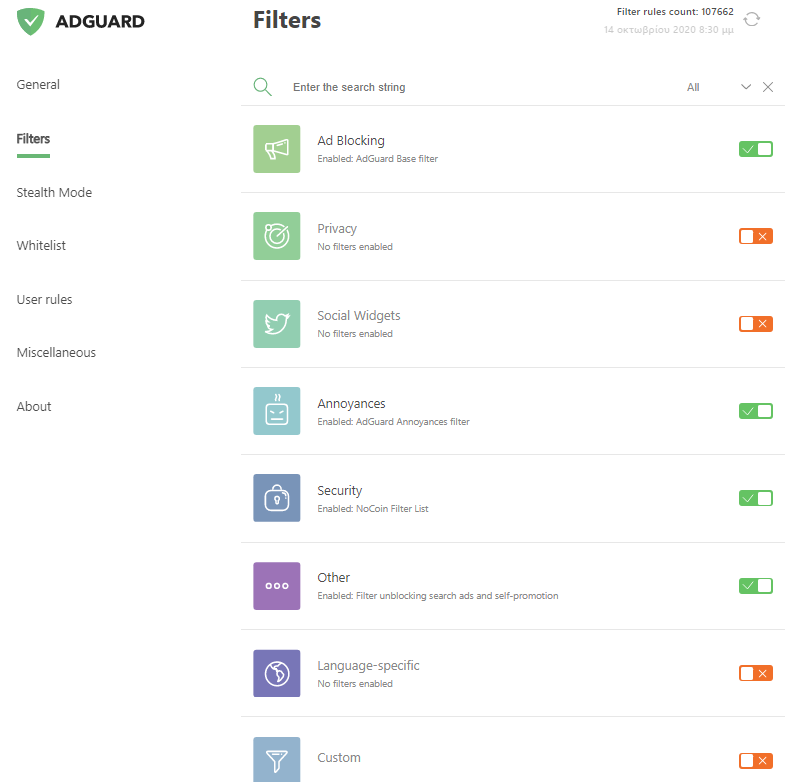
Use DNS that offer security like of AdGuard as well as an extension that will increase navigation security such as the AdGuard ad blocker.