His team Google Cloud revealed today a attack A DDoS that took place on Google's service in September 2017 reached 2,54 Tbps, making it the largest DDoS attack on record to date.
In one separate report published at the same time, Google Threat Analysis Group (TAG by Threat Threat Analysis Group), Google's security team that analyzes high-level threats, said the attack was carried out by state-backed hackers.
TAG investigators said the attack came from China, specifically from the network of four Chinese Internet service providers (ASNs 4134, 4837, 58453 and 9394).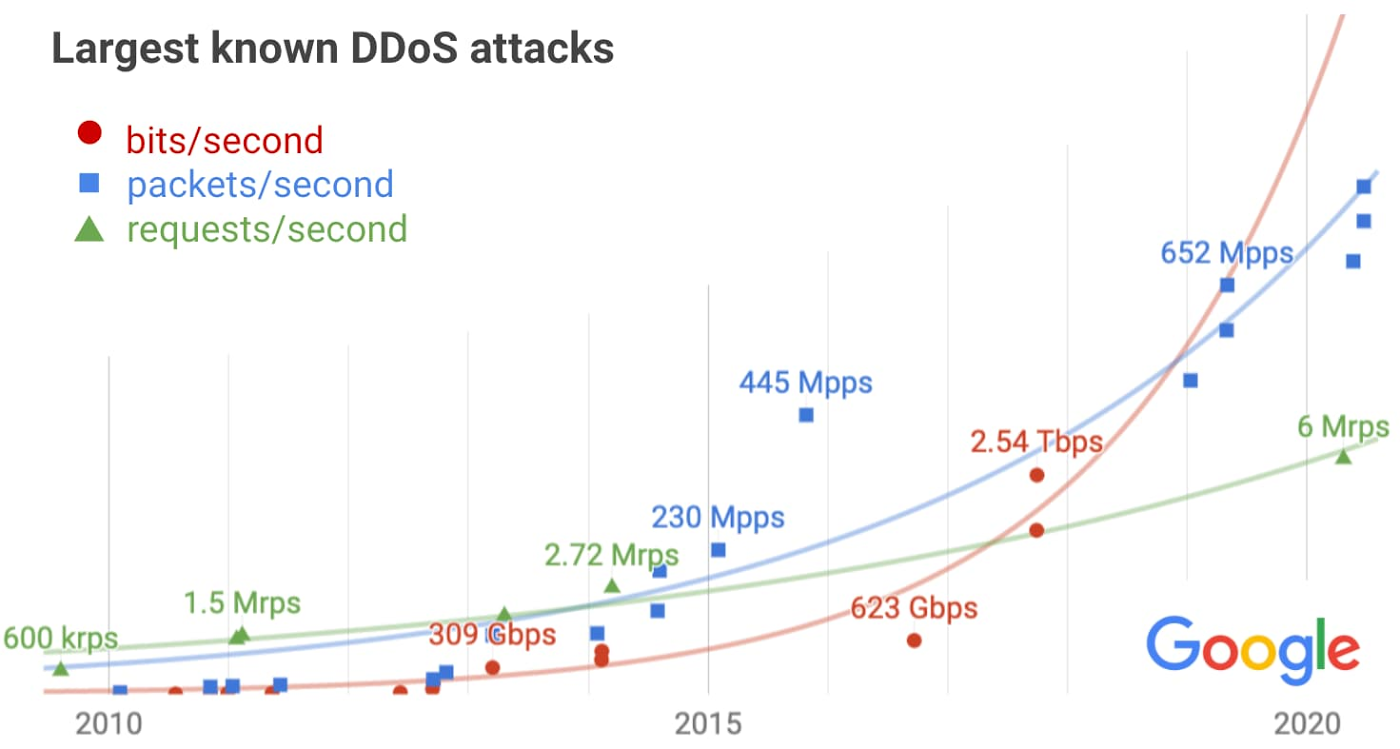
Damian Menscher, security engineer for Google Cloud, said the 2,54 Tbps pick was "the culmination of a six-month campaign" that used multiple attack methods to hit Google's server infrastructure.
Menscher did not disclose which services were the target of the attacks,
"The attacker used various networks to forge 167 Mpps (millions of packets per second) on 180.000 exposed CLDAP, DNS and SMTP servers, which would then send us larger packets," Menscher said.
"This demonstrates the volumes that an intruder can achieve with a good source: The hit was four times larger than the pioneering 623 Gbps attack achieved by mirai botnet a year earlier [in 2016]. ”
Additionally, this attack is also larger than the 2,3 Tbps DDoS attack that hit its AWS infrastructure Amazon this year in February.
Although the attack had not been revealed for three years, Google decided to reveal the incident today for different reasons.
The Google TAG team wanted to raise awareness of the growing trend of government hacker groups using DDoS attacks to hit targets.
The Google Cloud team also wanted to warn that DDoS attacks would intensify in the coming years as internet bandwidth increases.





