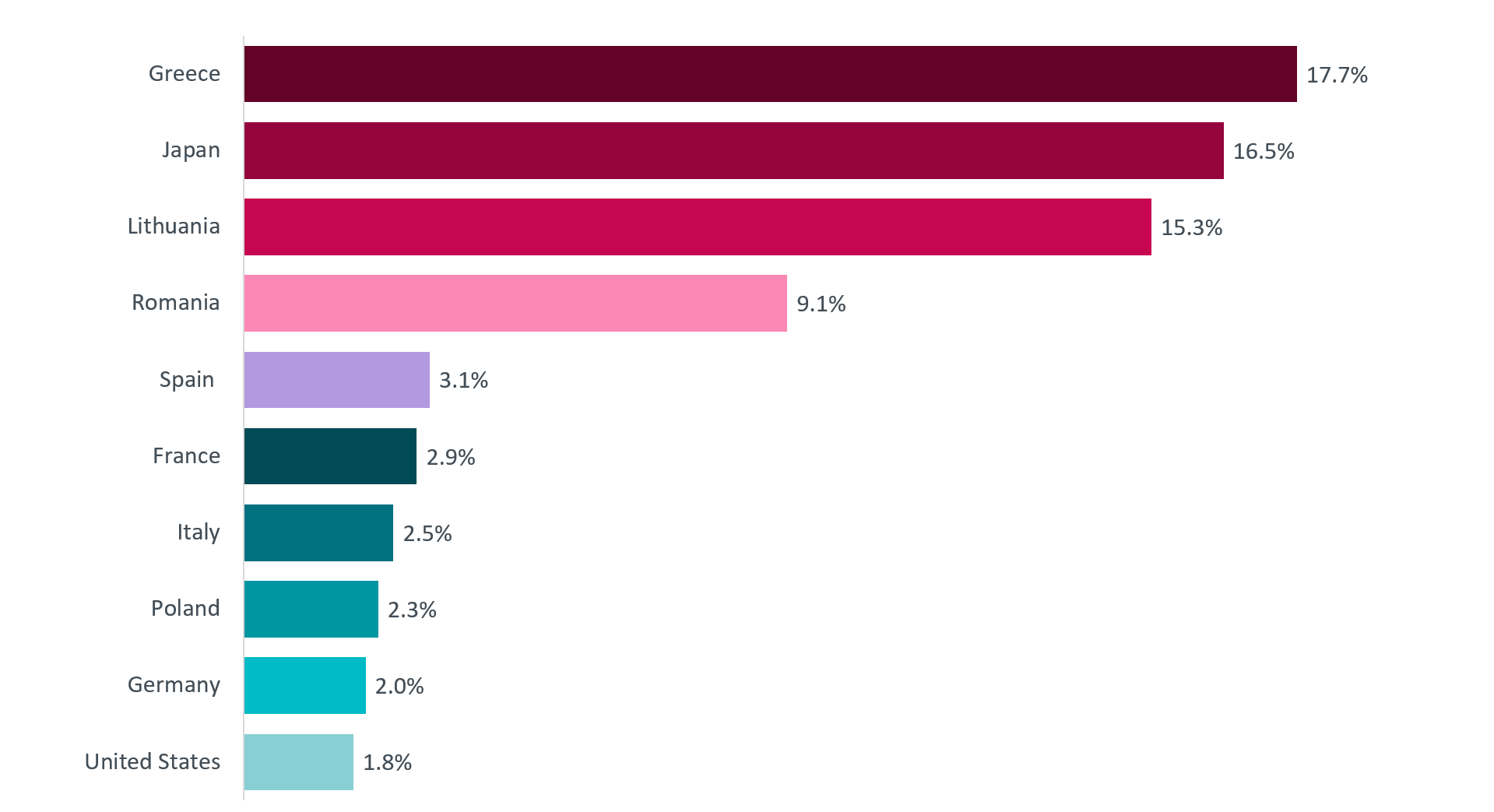
After a short break of two weeks, a huge Emotet botnet spam business is underway again. Until recently, most attacks were recorded on users in Greece (17.7%), while an equally significant number of attacks occurred in Japan (16.5%) and Lithuania (15.3%).
According to Forrester, botnets are one of the top cyber threats to look out for in 2020, and with a workforce working remotely in different areas, many organizations can become more vulnerable than ever.
Botnet operations can grow in sophistication, carrying out a wide range of illegal activities such as collection πληροφοριών προγράμματος περιήγησης, συλλογή κωδικών access, stealing login credentials from banking websites or deploying ransomware.
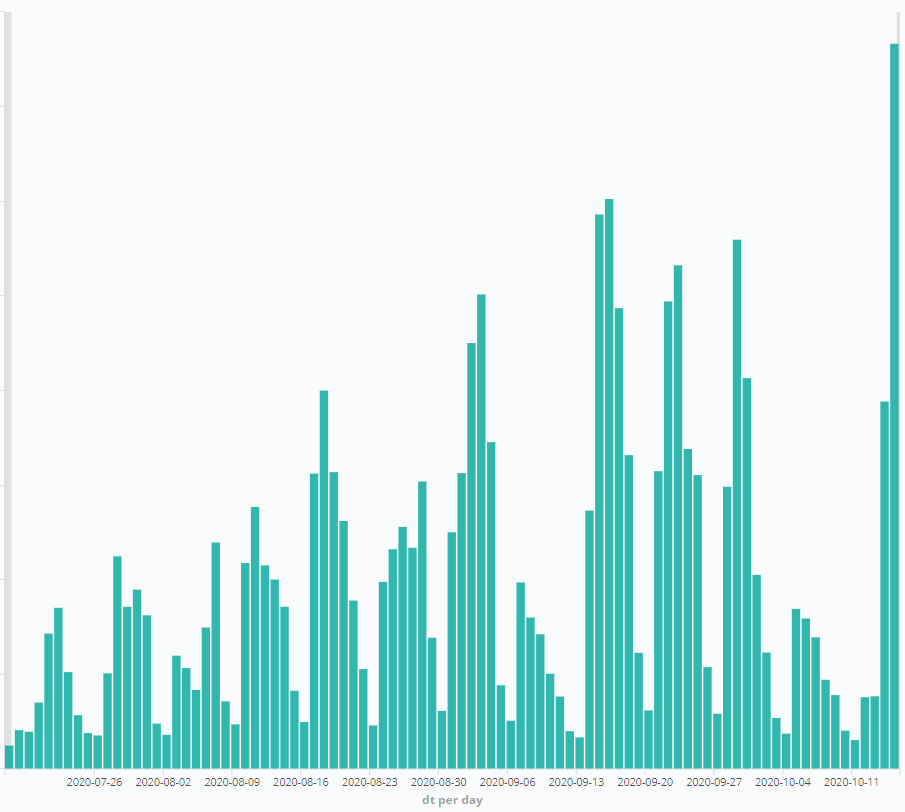
In the recent malware of Emotet, spam usually contains stolen legitimate communication and a general "Please see attached document" lure.
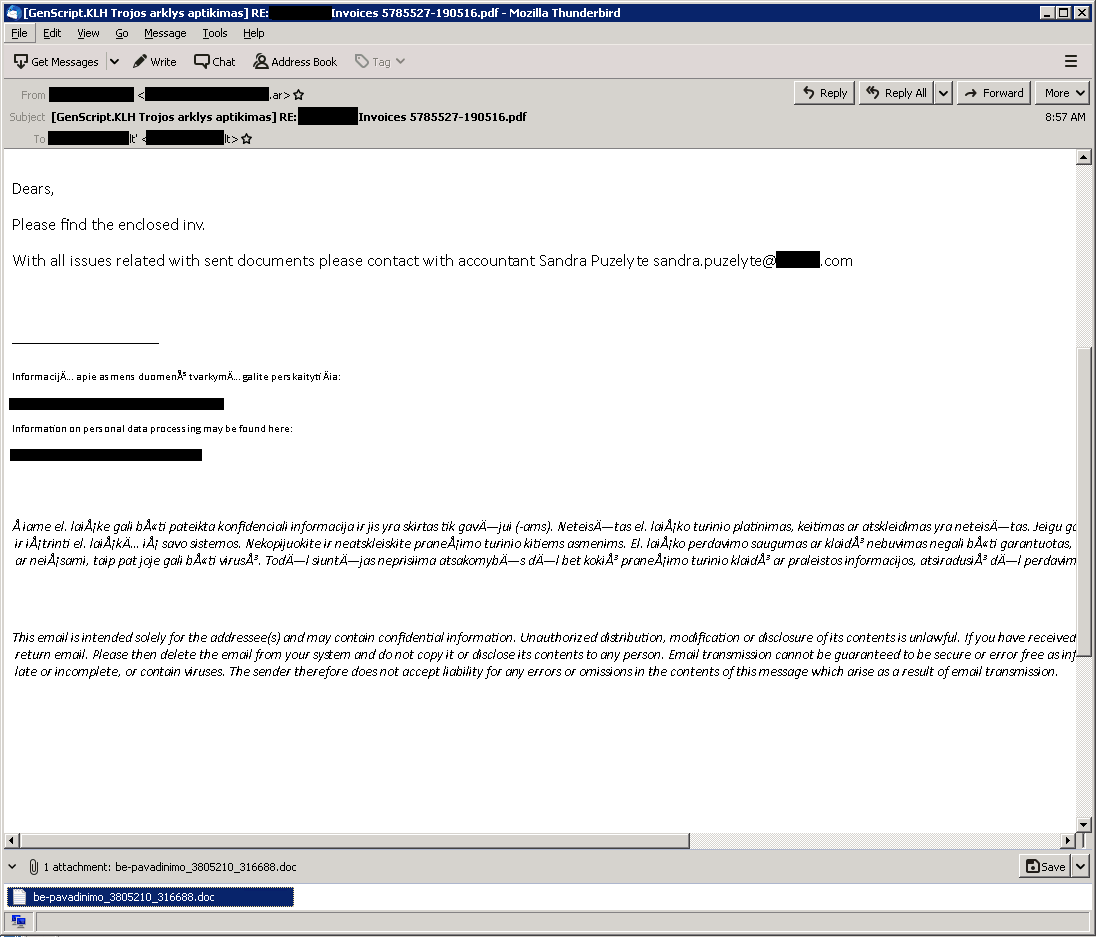
Attached this time is a malicious document detected by ESET as GenScript.KLH. This is a document containing a malicious VBA, identified as VBA / TrojanDownloader.Agent, which is the beginning of a chain infection infection.
Emotet is considered particularly dangerous, as it then installs other malicious programs on the victim's computer, such as Trickbot and QBot. Trickbot and QBot have their own malicious activity, however in turn they can lead to Conti (Trickbot) or Ryuk ransomware attacks.
https://www.youtube.com/watch?v=w2i-4mU-ldY
Είναι σημαντικό να τονιστεί ότι, παρά την τεράστια κακόβουλη επιχείρηση του Emotet botnet, η δράση του κακόβουλου TrickBot – το οποίο, από το 2016, έχει προσβάλλει πάνω από ένα εκατομμύριο υπολογιστές- παραμένει σε σαφώς περιορισμένα επίπεδα χάρη στην κοινή προσπάθεια αναχαίτισής του από τις ESET, Microsoft, Black Lotus Labs Threat Research της Lumen, NTT και άλλους.
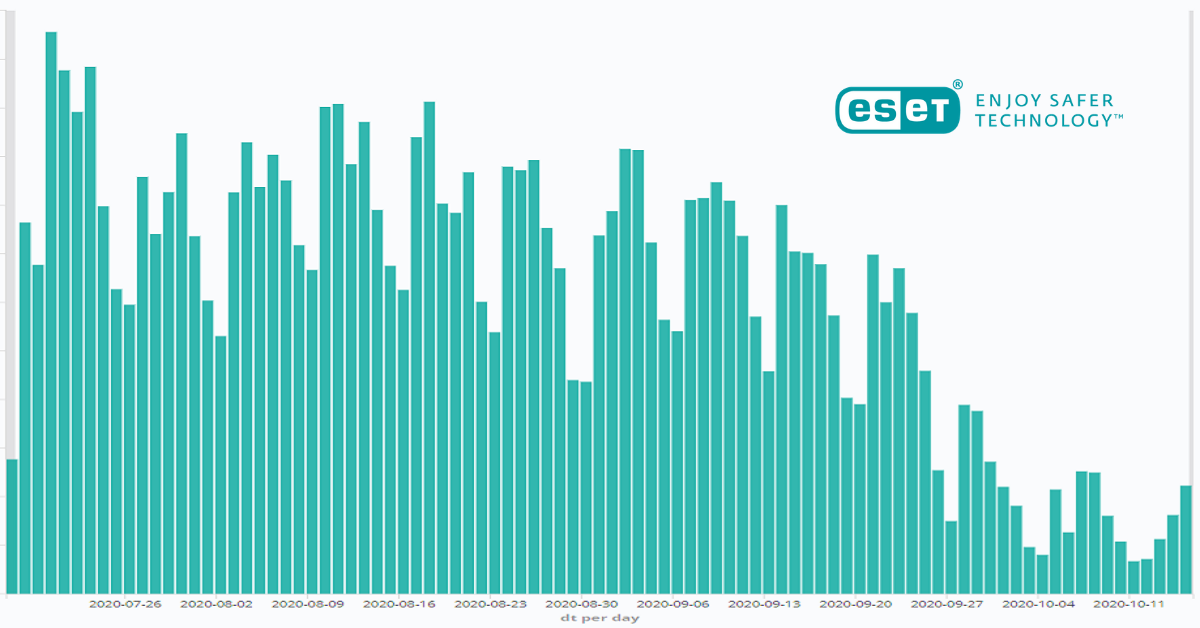
Trickbot is known to steal users' credentials from compromised computers and, more recently, it has been observed as a mechanism for carrying out more serious attacks, such as ransomware attacks.
The coordinated global operation interferes with Trickbot by crashing the servers orders and control. ESET contributed to the effort by providing technical analysis, statistics, and command and control server names and IP addresses.
Dealing with such a threat may seem like a daunting task, but there are ways in which organizations can protect themselves from botnet attacks.
Businesses also need to ensure that their networks are always up to date recent security updates, preventing cybercriminals from exploiting potential vulnerabilities. In addition, as remote ports can be turned into an entry point of hackers, businesses should restrict access as much as possible – especially when it comes to the RDP port.





