Security researchers warn of a new family of malware that is currently targeting cell phone users and quietly enrolling them in legitimate premium services.
Με το όνομα WAPDropper, το κακόβουλο λογισμικό είναι ένας dropper πολλαπλών λειτουργιών που μπορεί να προσφέρει κακόβουλο λογισμικό και χρησιμοποιεί technology μηχανικής εκμάθησης για να παρακάμψει τις προκλήσεις CAPTCHA που χρησιμοποιούν εικόνα.
The company Cybersecurity Check Point identified WAPDropper in a recent campaign and found that it was signing up its victims for premium services from legitimate telecom providers in Malaysia and Thailand.
The malware analysis revealed that it has two modules, which can download and run other malware on a compromised device.
Στην περίπτωση του WAPDropper, υπάρχει μια μονάδα που είναι υπεύθυνη για την ανάκτηση κακόβουλου λογισμικού σε ένα δεύτερο στάδιο από τον διακομιστή εντολών και ελέγχου και μια άλλη μονάδα για την acquisition of the premium dialer.
The plan for scammers to make money is simple: many calls to premium numbers charge the victim's account.
CAPTCHA bypass
According to Check Point, WAPDropper administrators use a common tactic, embedding the malware in applications available from unofficial stores.
Once on the victim's device, the malware communicates with the command and control server (C2) to download the program that makes the premium calls.
In one technical reference , the researchers report that the malware activity starts with collecting details from the infected device:
- Device ID
- MAC address
- Subscriber ID
- Device model
- List of all installed applications
- List of services running
- Top activity package name
- The screen is on
- Are activated alerts for this application
- This application can design overlays
- Amount of free storage available
- Total amount of RAM and available RAM
- List of applications outside the system
Then a web viewer starts to load landing pages for premium services and make a subscription.
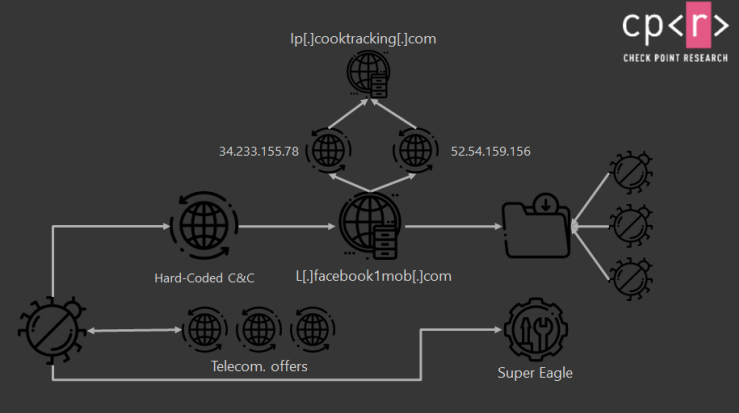
If there is a CAPTCHA that uses images, Check Point reports that WAPDropper uses the services of a Chinese company called "Super Eagle", which provides image recognition solutions based on machine learning technology.





