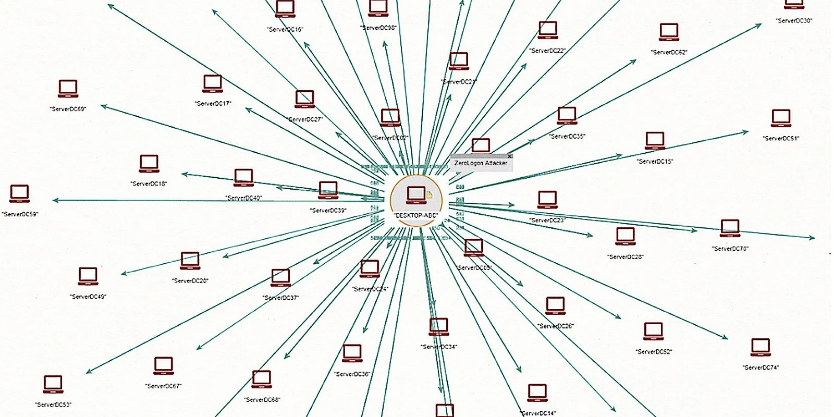
Microsoft has added Zerologon detection support to Microsoft Defender for Identity to enable Security Operations teams to detect attacks within the enterprise that attempt to abuse this critical vulnerabilitys.
Microsoft Defender for Identity (formerly known as Azure Advanced Threat Protection or Azure ATP) is one solution better safetyis cloud-based and designed to leverage on-premises Active Directory signals to detect and analyze compromised identities, advanced threats, and malicious insider activity targeting a registered organization.
"Microsoft Defender for Identity can detect this vulnerability early on," said Microsoft Program Manager Daniel Naim. "It covers both aspects of exploiting and controlling the circulation of Netlogon."
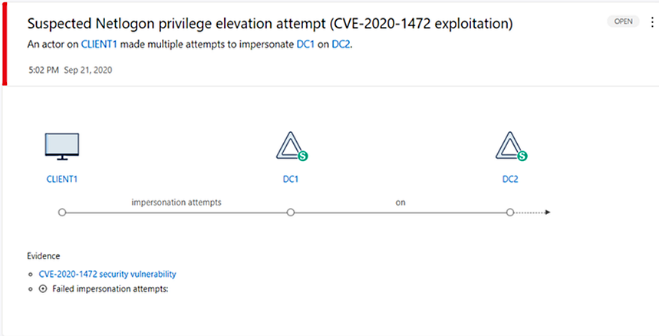
Alerts displayed whenever a Zerologon exploit or related activity is detected will allow SecOps teams to quickly obtain information about device or the domain controller behind attack attempts.
Alerts will also provide information that can help identify targeted information if the attacks were successful.
"Finally, customers using Microsoft 365 Defender can take full advantage of the strength of Microsoft Defender for Identity signals and alerts, combined with behavioral events and crawls from Microsoft Defender for Endpoint," Naim added.
"This coordinated one protection it enables you to not only monitor Netlogon exploit attempts over network protocols, but also see device process and file activity related to the exploit.”