As many companies are now online on the internet, the need for security specialists has increased dramatically. If you are eager to learn ethical hacking, it is recommended that you get some of the best books for this purpose.
Such ebooks will help you gain knowledge of cyber security and are an excellent prerequisite before using penetration testing tools.
In this article we will look at the top 5 tools that are pre-installed on Time Linux.
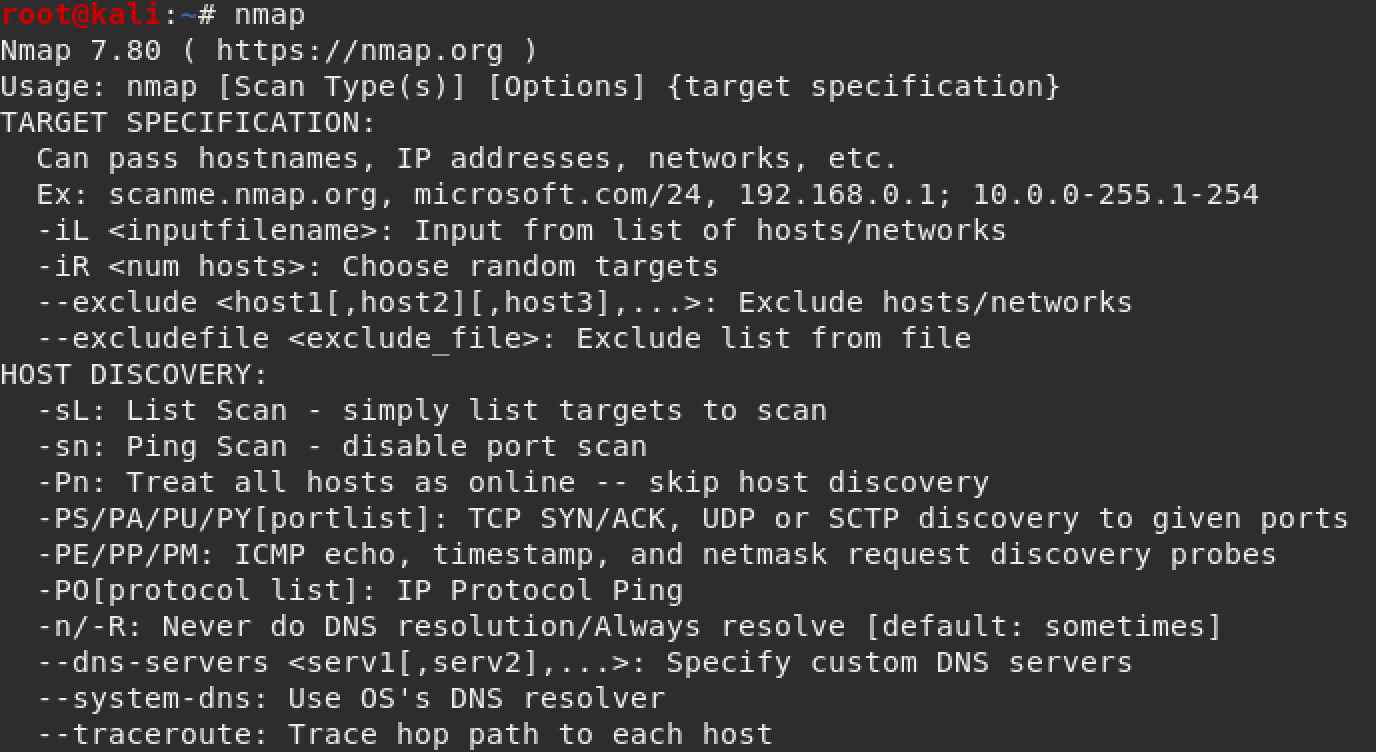
Nmap is a powerful evaluation tool when used to scan a network. Nmap allows one to discover open ports and running services along with their respective version numbers. Nmap also has the advantage ofcase of a bundle actions which when used correctly can be a very powerful addition to penetration testing.
Wireshark
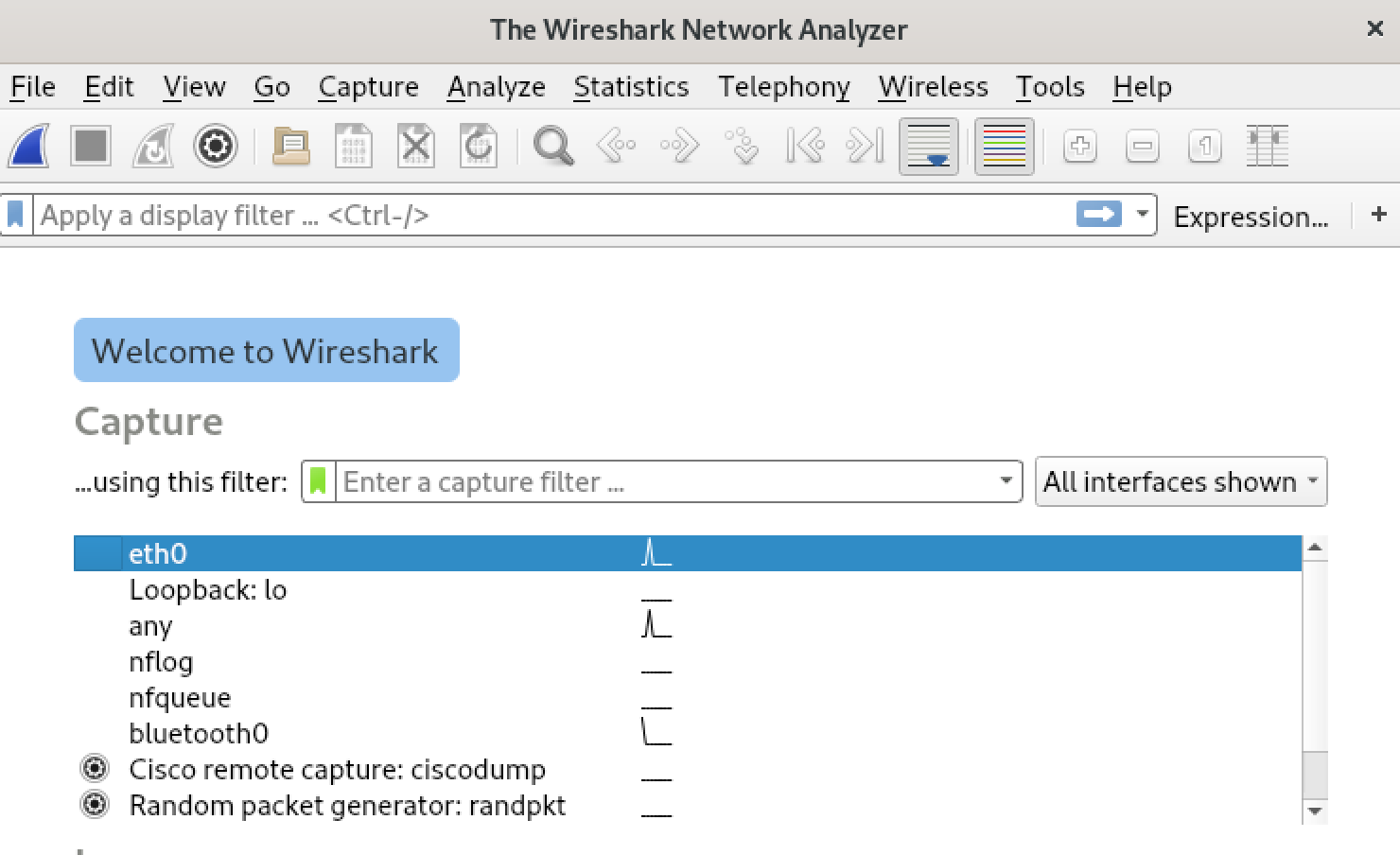
Wireshark is a popular network analysis tool. It is designed to scan packets passing through a network and is the favorite analytics tool for many security system researchers who want to make sure their code works as expected or for pentesters who want to check the security of their projects.
Burp Suite
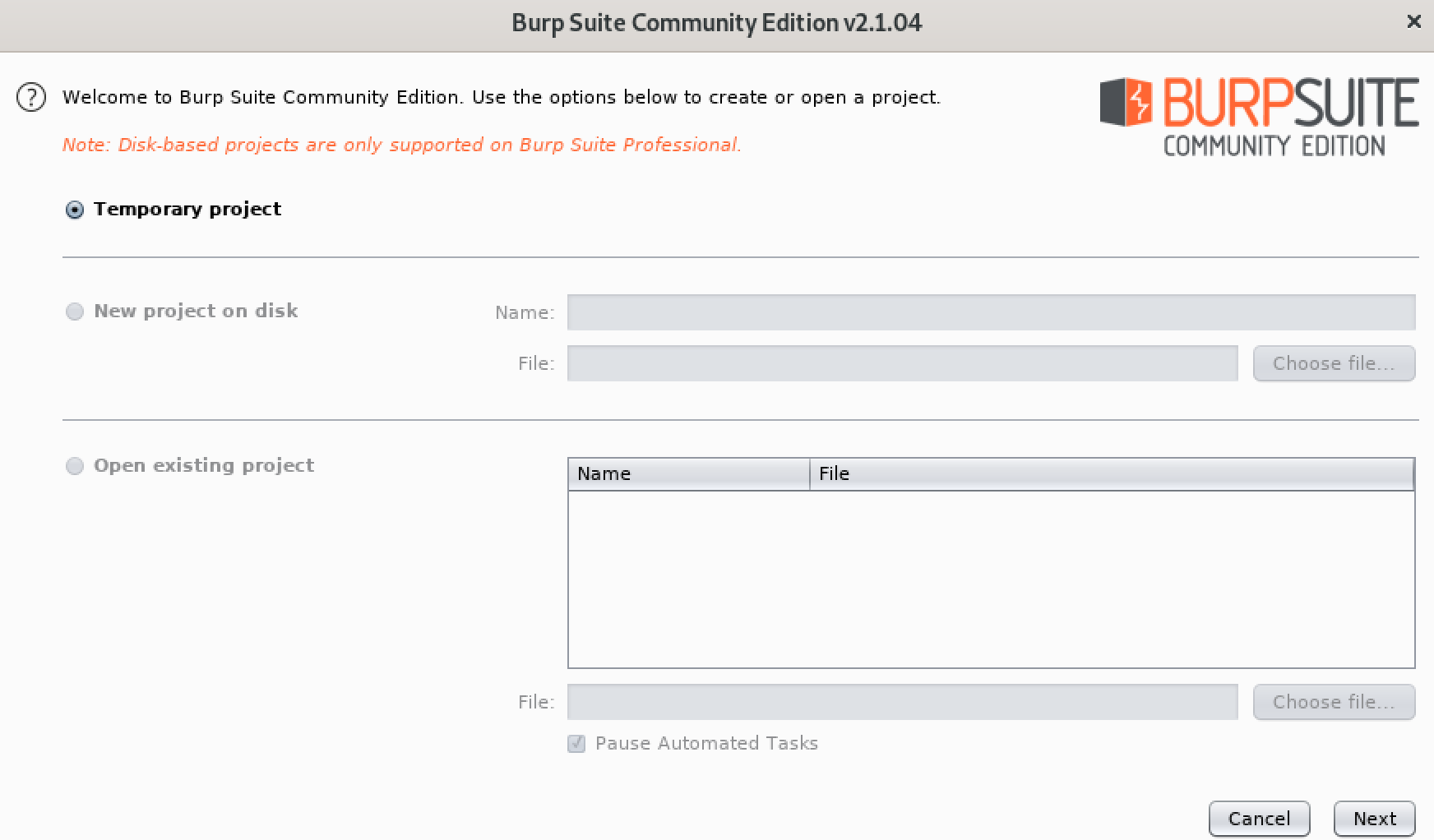
Burpsuite is the go-to tool for almost any web application penetration testing, it has a wealth of additional tools most of which are free on the Internet.
With Burpsuite we can perform a complete penetration test as it has all kinds of add-ons for the risks of web applications and not only. The paid version is necessary for you who work in the field of Cyber Security.
WPScan
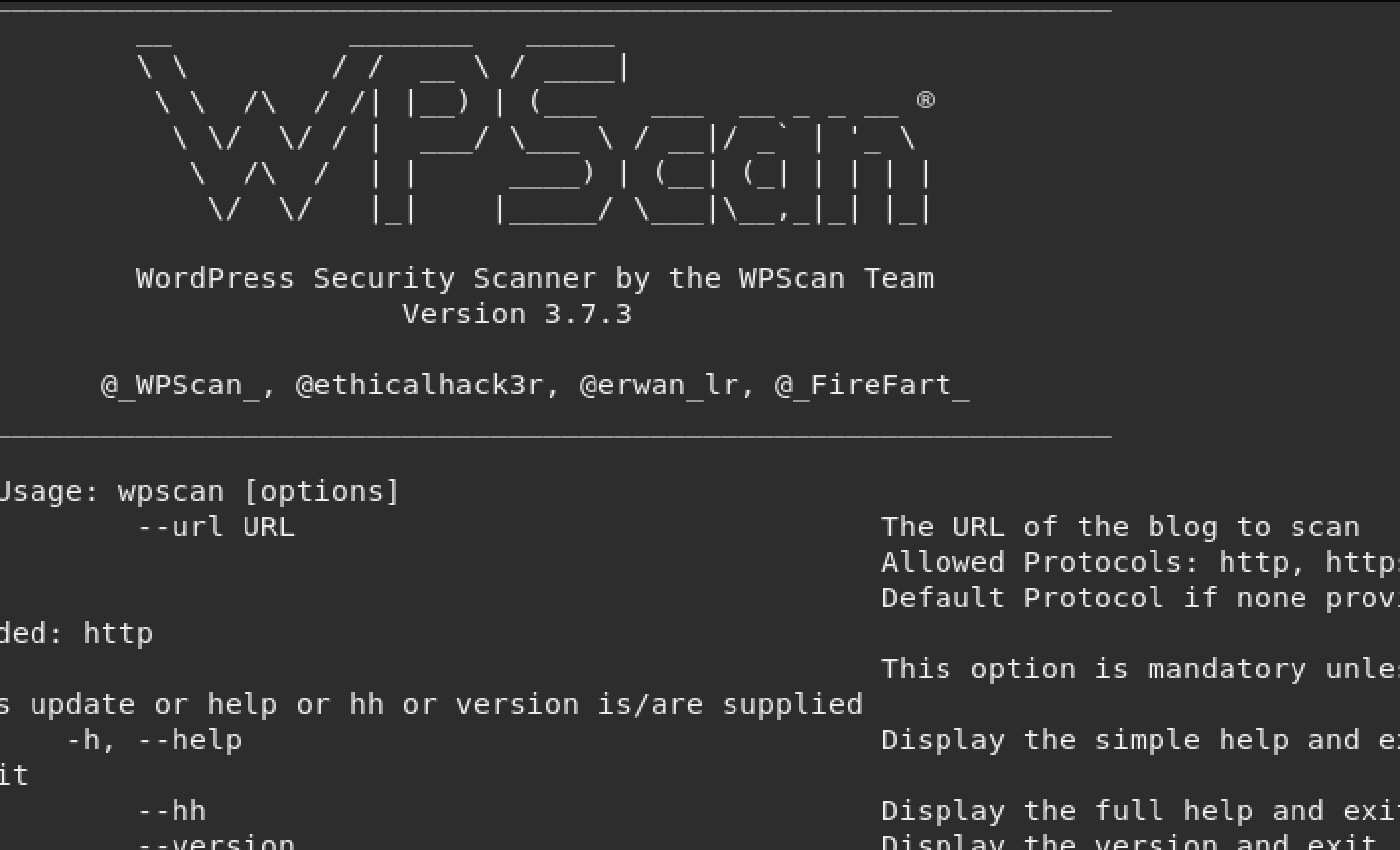
WPScan is a tool specifically designed to detect vulnerabilities in WordPress pages. It can detect WordPress versions, which plugins are running and if there are any vulnerabilities.
It can also search for usernames, brute force the code accessof the administrator and succeeds in uploading a backdoor to allow shell access to the victim's website.
Nessus
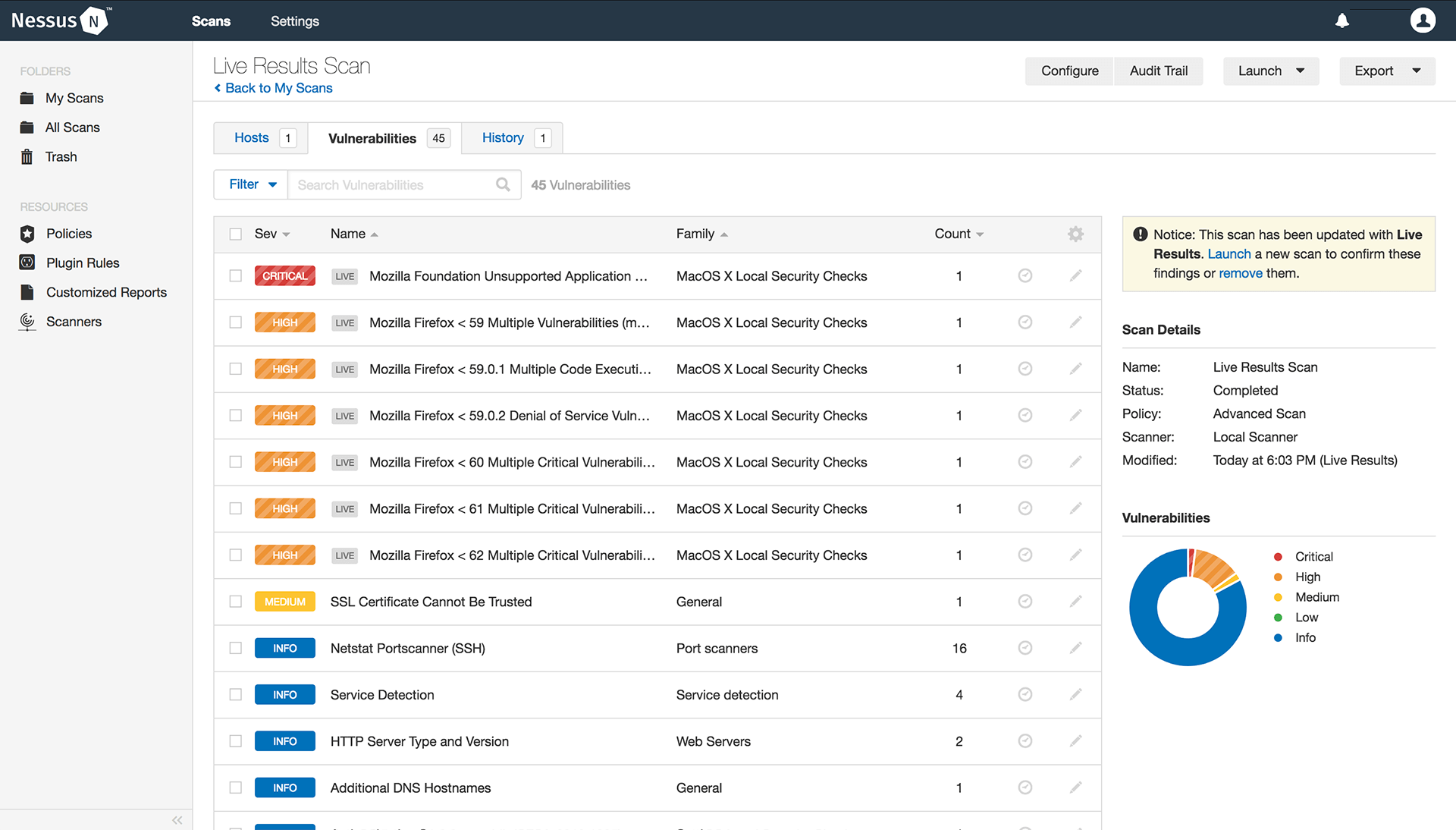
Nessus is a very important vulnerability scanner. It comes with a user-friendly graphical user interface and is able to scan multiple networks for open ports and vulnerabilities.





