Uneducated and rather naive Android users seem to be the target of an Android banker trojan (Acecard) requesting the shipment of one Selfie from his victims holding their police officer ID card.
The name of the trojan is Acecard and is considered one of the most dangerous and intrusive Android trojans that is known today, according to a Kaspersky analysis last February.
In an earlier version the Acecard trojan was hidden inside a Black Jack game that was distributed through the official Google Play Store. Η πιο πρόσφατη έκδοση του κακόβουλου λογισμικού σύμφωνα με τους ερευνητές ασφαλείας της McAfee μπορεί να κρυφτεί μέσα σε όλα τα είδη των εφαρμογών που χρησιμοποιούν το Adobe Flash Player, in pornographic material or in video codecs.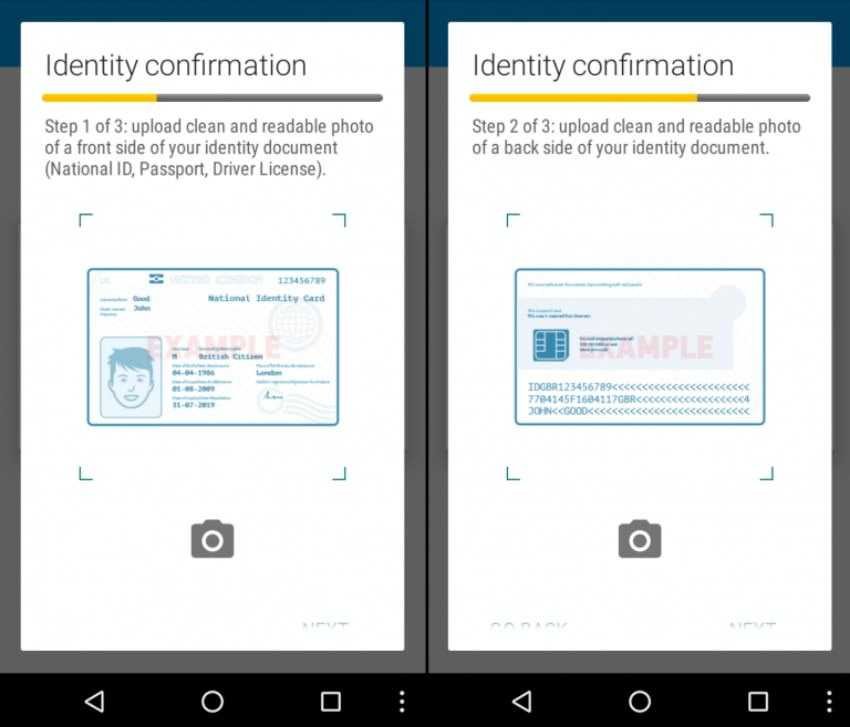
All of these apps are distributed outside of the Play Store and are known because they are constantly asking for the victim's permission until they get what they want, that is, administrator rights.
Once this step is reached, the trojan is hidden until the user opens a specific application. McAfee researchers found that when a user opens the Google Play app, the trojan uses a social engineering trap.
First, it asks the user for his credit card number. Then, in different pop-ups, he asks the user for his card details, such as the name and expiration date, but also asks for his real identity.
After that, the trojan gives his victim new instructions requiring him to pull back and forth his identity. In the third stage the trojan asks the user to keep the ID in his hand under his face and get a selfie.
"This is very useful for a cybercriminal who wants to verify the identity of the victim and have access to not only bank accounts but maybe even social networks," says Carlos Castillo of McAfee.
In addition to Google Play, this version of Acecard also collects access credentials from the following services: Facebook, WhatsApp, WeChat, Line, Viber, Dropbox, Google Music, Google Books, and Google Videos.
This trick obviously works only to beginner users.





