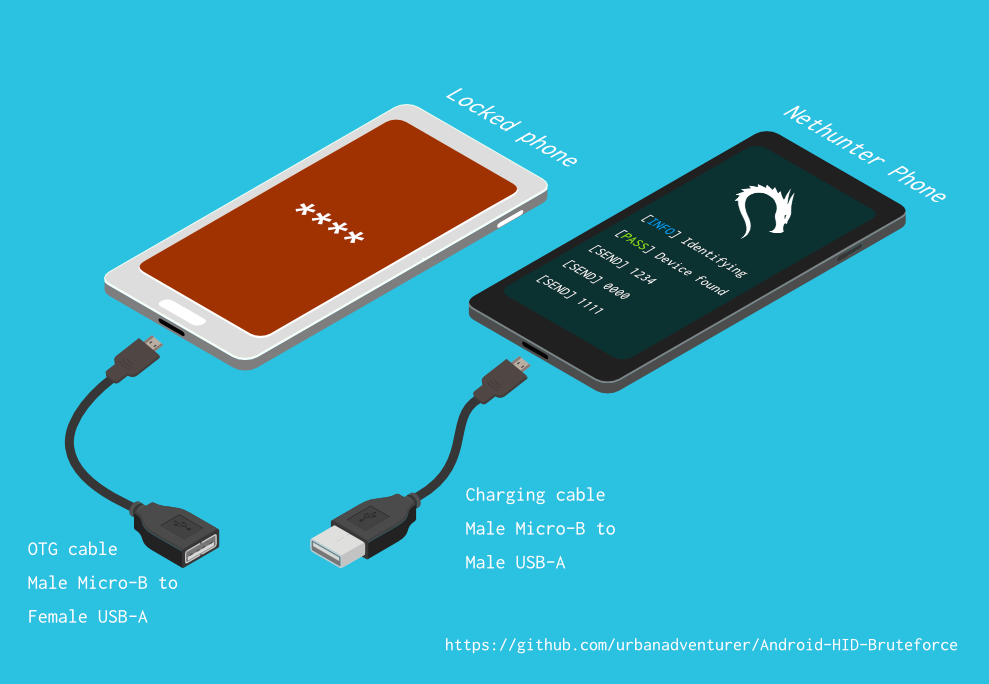
This feature already exists in Kali Nethunter and what it actually does is through a device Android, access another device.
We are given the opportunity both to bypass the lock screen, and to take full control of a device for future use.
How to avoid such an attack
- We always charge our mobile phone with our own charger
- We always use a complex lock code screen or some complicated pattern
- We use programs protections on our device and more specific programs that detect and prevent exploits.
PoC
What we need
- A rooted Android device with support for HID attacks on settings of Kernel (eg NetHunter ROM)
- OTG cable
The script may not work every time. Therefore, we must play with the keys we send to our target and change the exploit if it does not succeed with the first one. A list of all possible keys can be found at the link below.
HID support in custom ROM
https://github.com/pelya/android-keyboard-gadget
Brute-force attack using our Android
https://github.com/urbanadventurer/Android-PIN-Bruteforce
List of all available keys
https://github.com/anbud/DroidDucky/blob/master/droidducky.sh





