Address Space Layout Randomization or ASLR: Windows 8, Windows 8.1 and later versions of Windows 10 reportedly do not implement ASLR properly, rendering a very critical Windows security feature useless.
Address Space Layout Randomization or ASLR is a security technique that selects random memory addresses to run the code of an application.
The ASLR feature was originally released in 2003 in OpenBSD and has since been added to all major operating systems, Linux, Android, MacOS, and Windows.
Microsoft has first added ASLR to Windows with 2006 Vista. To enable the feature, users had to install Microsoft EMET and use their GUI to choose to use ASLR in system-wide or application-specific situations.
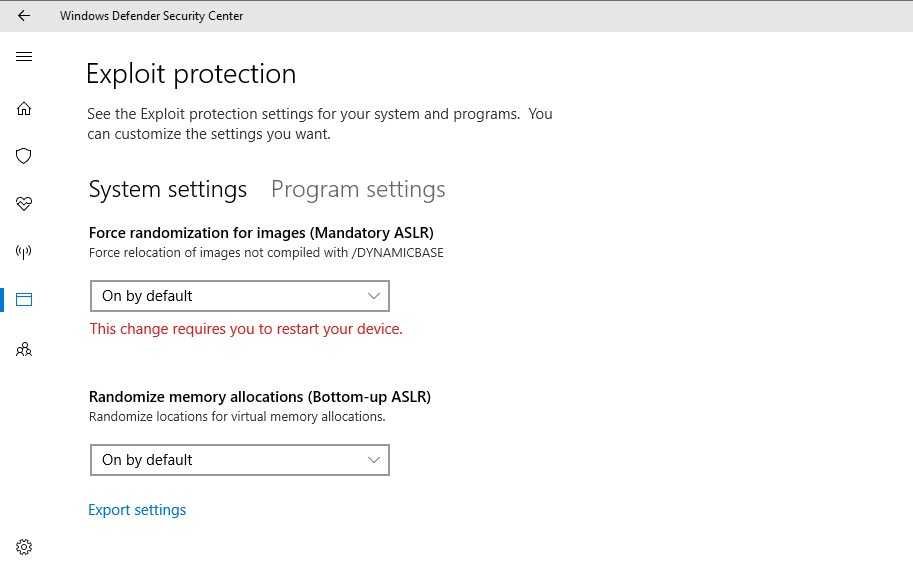
With the release of Windows 10, ASLR was added to Windows Defender Feat Guard and users can enable it through the Windows Defender Security Center.
A vulnerability that exists here and 17 years (was recently revealed) that affects the Microsoft Office equation editor, demonstrated that ASLR did not randomize memory code addresses into application files under certain conditions.
According to Will Dormann, a CERT / CC vulnerability analyzer, when users activate ASLR protection across the system, there were errors that did not allow the creation of random memory addresses.
"The result is that programs used the same address every time on all reboots even on different systems," Dormann said in a statement. published in CERT.
This practically means that ASLR is not used even though it is enabled, which means that users of the feature security they are open to memory address reuse attacks of an application containing malicious code.
The researcher says that this issue only affects Microsoft systems from Windows 8 and then because the company changed the registry values through which the ASLR starts.
Of course Microsoft is expected to fix the problem in some future update and for now, the only way to boot the ASLR feature to work is a tweak oscillation in the Windows registry.
How can I protect:
Create a text file and type the following text:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\kernel] "MitigationOptions"=hex:00,01,01,00,00,00,00,00,00,00,00,00,00,00,00,00
Save the .reg file instead of .txt, for example, iguru.reg.
Optionally, you can download the file we made for you, and run it with a double click (after thetreatment of from .zip)
Right click save as:





