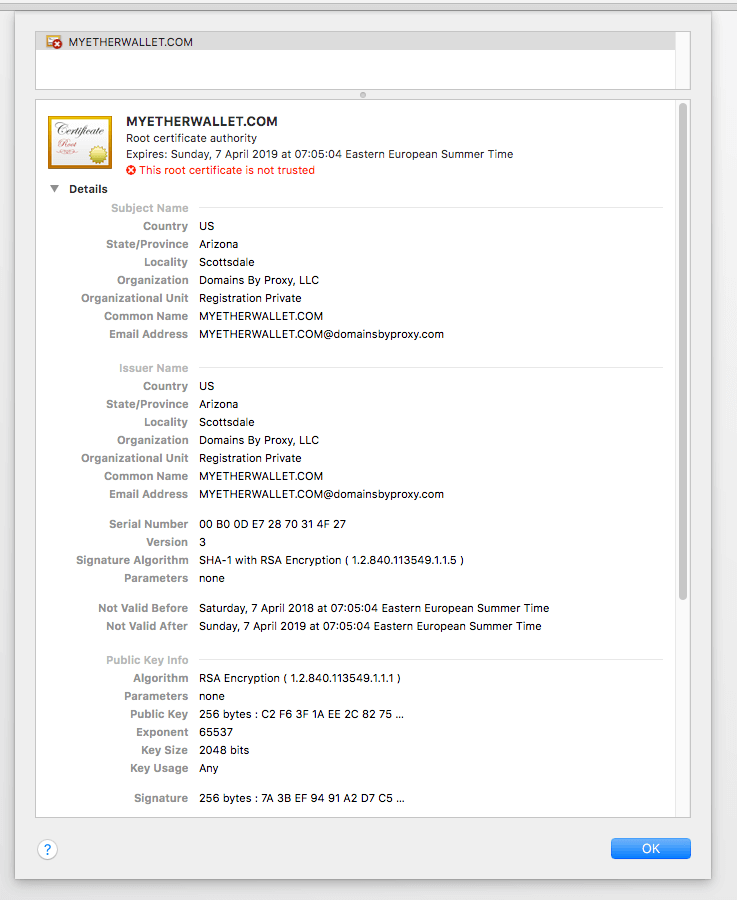
BGP hijacking: Last night, users of MyEtherWallet began to notice something strange. By signing in to the service, there was a non-signed SSL certificate and of course a warning.
It was unusual, but it was the kind of problem that usually some react without thinking.
But anyone who clicked on this certificate warning was redirected to a server in Russia, which emptied the digital wallet (wallet) του χρήστη. Κρίνοντας από τη δραστηριότητα των συναλλαγών, οι επιτιθέμενοι φαίνεται να αποκτήσει ήδη περισσότερα από 17 εκατομμύρια δολάρια σε Ethereum.
MyEtherWallet has confirmed attack in a statement to Reddit.
"We are currently in the process of verifying the servers to resolve this issue as soon as possible," the company told users. "We advise users to run a local (offline) copy of MyEtherWallet."
The attackers did not appear to have breached MyEtherWallet itself, but used an internet infrastructure, blocking the requests DNS of myetherwallet.com. So they made the Russian server look like the rightful owner of the address.
To hinder these requests, hackers used a technique known as BGP hijacking. This technique spreads misleading routing information to trap movement during transport. Typically, the use of such a hijacker requires invasion of BGP servers operated by an ISP (Internet Infrastructure Provider). In this case, hijacking happened to an ISP from Chicago, although the root of the evil is still unknown.
So far, MyEtherWallet is the only confirmed service to have this kind of attack.
It should be mentioned that BGP hijacking has long been known as a fundamental weakness in Internet. The story is a very good example of what can happen when we operate automatically, or impulsively without thinking.
See the certificate used: