A vulnerability in the popular BitTorrent Transmission application allows malicious users to remotely control computers running the program. The revelation was made by his researcher Google Project Zero Tavis Ormandy who reported that there is a possibility that the same security flaw exists in other BitTorrent clients.
The bug is in the feature that allows users to control BitTorrent from their browsers, and this feature is available in most BitTorrent applications that are running. 
Ormandy he also says, that many are running those without a password because they believe that physical access to the system is required by hackers. But if someone who knows uses an attack method called DNS rebinding can take control of the computer running the application.
All you need is a website that hosts the malicious code needed to exploit the vulnerability. At the moment, it seems that both Google Chrome and Mozilla Firefox on Windows and Linux can be used to attack.
Technical analysis of the vulnerability shows that hackers can change the torrents download list and simultaneously use Transmission to run commands when downloads are over.
The worst thing is that Transmission programmers have so far ignored Ormandy who says he has been contacting them for a long time.
To mention that all security flaws discovered by the program Project Zero, they are publicly disclosed 90 days after the app developer is notified. In the event that the company has not released an update to fix the vulnerability, Project Zero program policy allows public disclosure of the vulnerability. This time, however, Ormandy decided to release all the details 40 days after the vulnerability was announced.
But look at the image below from the qBitTorrent which I use: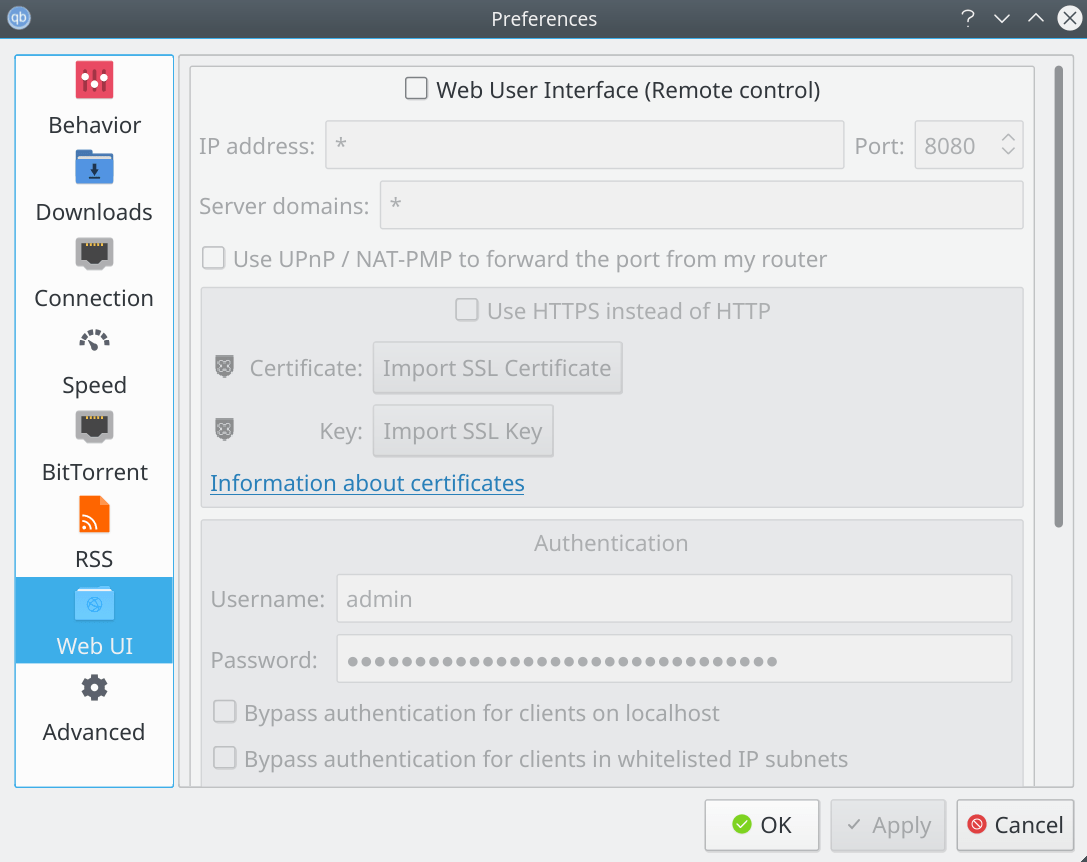
And below the web ui of Transmission:
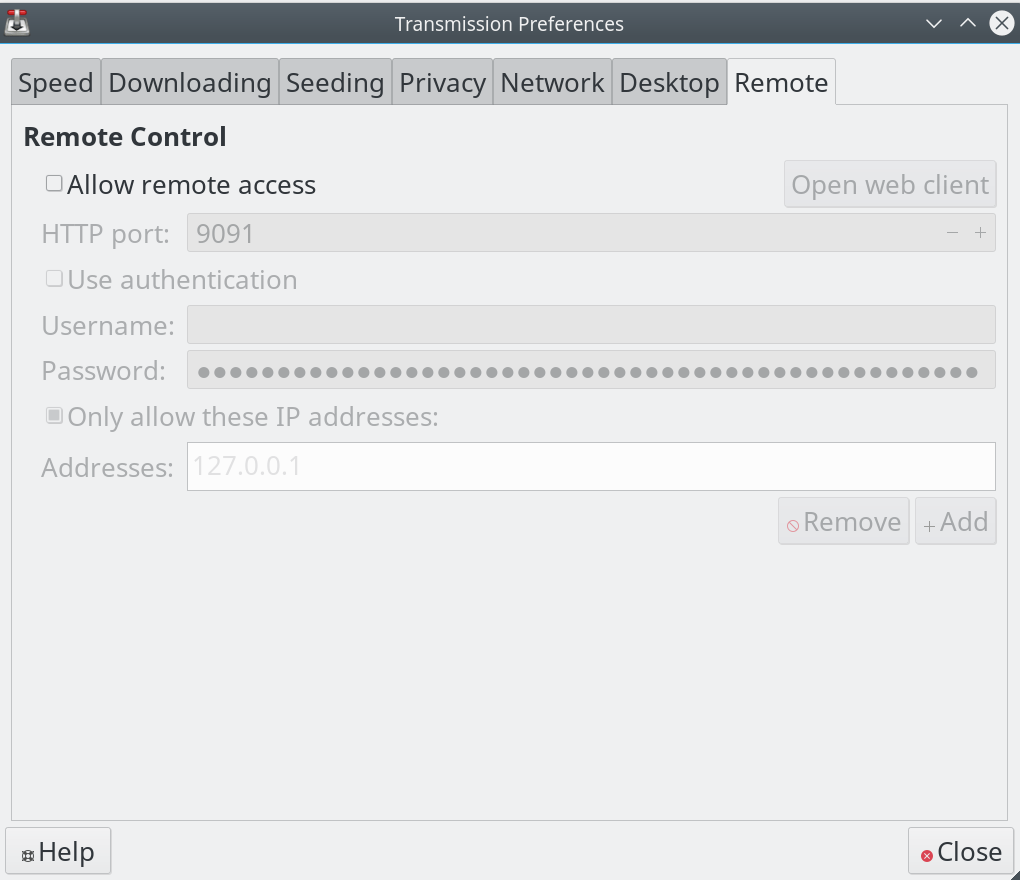
According to the above images, I should mention that BitTorrent clients I know and I have used this feature disabled by default, so the Ormandy rush was probably not needed.
You have encountered a client with it activated remote control?





