Technical details about a high-vulnerability in Facebook's Instagram app for Android and iOS show how a malicious user could exploit it to take full control of the victim's account.

For this technique to work, the malicious user would have to send the target a specially crafted image via a common exchange platform messages or via email.
The issue was how analysisς των εικόνων από το Instagram, αρκεί η εφαρμογή να έχει πρόσβαση σε αυτήν για να την εμφανίσει ως choice in a post. Then the vulnerability would start by allowing dangerous actions.
Technically, vulnerability is a buffer overflow (CVE-2020-1895) that happens when Instagram tries to upload a bigger image believing it is smaller.
Facebook fixed the problem in the spring, after the revelation of the company Check Point and issued security tips to deal with it.
In a detailed technical report today, Gal Elbaz of Check Point points out how custom third-party code implementation on Instagram could lead to serious, remote code execution risks.
The weak point, in this case, was a fixed hardcoded value that the Instagram developers added when integrating the Mozjpeg, an open source JPEG encoder that Mozilla modified libjpeg-turbo to better compress JPEGs.
Check Point started checking Mozjpeg for possible defects that could be exploited in a meaningful way. The purpose was to find out if Instagram could be influenced by the library.
They found that the function that handles image sizes when parsing JPEGs had a bug that caused memory allocation problems during the parsing process.compression.
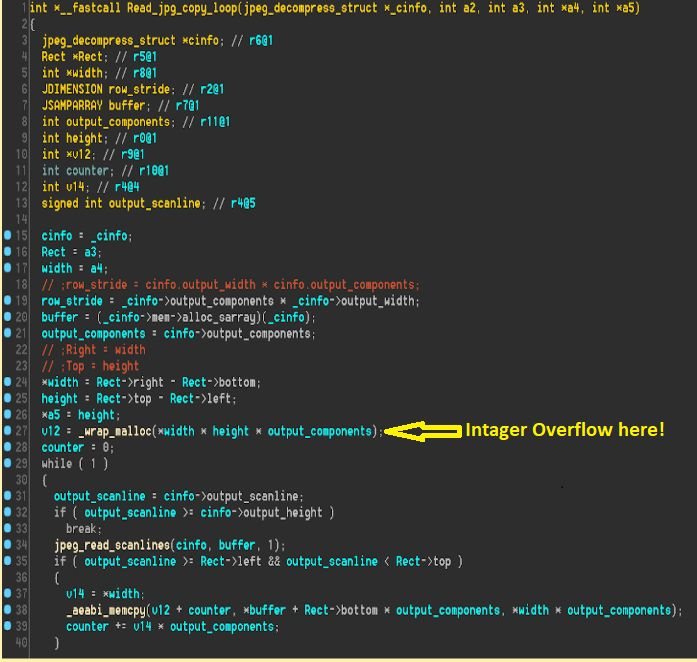
This could be used to damage memory, which can have dangerous consequences. At best, this type of error could throw Instagram, but if exploitable, it can lead to critical risks.
According to Check Point, Instagram has extensive permissions on the device, which include access to contacts, storage, device location, camera and microphone.
So in addition to checking the device owner's Instagram, a hacker could use the device as a spy tool without suspicion.





