PixStealer: Check Point Research (CPR), its research division Check Point Software Technologies, για κυβερνοεπιθέσεις σε χρήστες του PIX, του συστήματος άμεσων πληρωμών που διαχειρίζεται η Κεντρική Τράπεζα της Βραζιλίας, ανακάλυψε πως οι εγκληματίες του κυβερνοχώρου εξαπάτησαν τους χρήστες ώστε να μεταφέρουν ολόκληρο το υπόλοιπο του λογαριασμού τους σε άλλο τραπεζικό λογαριασμό, διανέμοντας δύο κακόβουλες εφαρμογές στο Play Store of Google.
Applications have now been removed from the Google Play Store, but Check Point Software recommends that users immediately remove malicious applications from their mobile phones.

Check Point Research (CPR) has detected cyberattacks against users of PIX, the instant payment solution developed and managed by the Central Bank of Brazil. The attackers distributed two different variants of banking malware, called PixStealer and MalRhino, through two different malicious applications in the Google Play Store to carry out their attacks. Both malicious applications were designed to steal victims' money through user interaction and the original PIX application.
PIX is considered the number one payment solution in Brazil, handling more than 40 million transactions a day and managing $ 4,7 billion a week.
| Name | Package Name | Md5 |
| Inter bank | br.com.intermidium | 2ef536239b84195e099013cfda06d3dd |
| Nubank | com.nu.production | 678212691ab75ea925633512d9e3b5f4 |
| Next | br.com.bradesco.next | d74e8b32e9d704633bd69581a15f55de |
| Santander | com.santander.app | 38737771e1ddab60c062cd0be323e89b |
| UOL PagBanks | br.com.uol.ps.myaccount | 5b3deb74ec783b05645b3fff5d56667d |
| Banco origafter | br.com.original.bank | 64679e8af5f494db86fb7b7312e79ba9 |
PixStealer transfers account amounts to intruder accounts
The first parchange it's called PixStealer. Presented in what CPR calls a “slim” form factor, the attackers designed PixStealer with only one capability: to transfer the victim's money to an account controlled by the perpetrator.
PixStealer's "slim" presentation is a reference to the variant's ability to operate offline with a command and control (C&C) server, promoting unobtrusive detection. CPR eventually found PixStealer distributed in the Google Play Store as a fake PagBank Cashback service, targeting only the Brazilian PagBank.
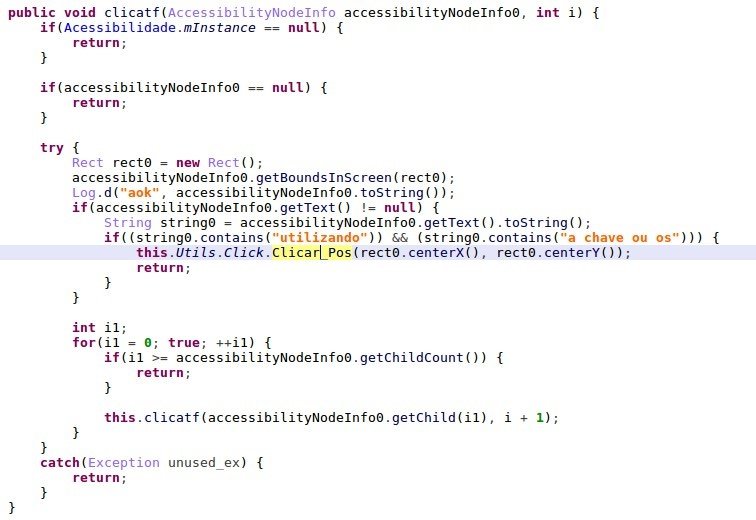
When a user opens the PIX bank application, Pixstealer displays an overlay window on the victim, where the user cannot see the intruder's movements. Behind the overlay window, the attacker recovers the available amount of money and transfers the money, often the entire account balance, to another account.
MalRhino completely steals banking applications
CPR found a more advanced variant of banking malware capable of taking over the entire PIX mobile app and other banking apps. Called MalRhino, CPR found the most sophisticated variant of the malware in a fake iToken app for Brazil's Inter Bank – also distributed through Google's Play Store. MalRhino displays a message to its victim trying to get them to donate permission accessibility. Once this is done, MalRhino can:
- Get the installed application and send the list to the C&C server along with them information of the victim's device.
- Execute banking applications
- Recover the pin from the Nubank application
IOCs
PixStealer
28e8170485bbee78e1a54aae6a955e64fe299978cbb908da60e8663c794fd195 com.pagcashback.beta c0585b792c0a9b8ef99b2b31edb28c5dac23f0c9eb47a0b800de848a9ab4b06c com.pagback.beta
8b4f064895f8fac9a5f25a900ff964828e481d5df2a2c2e08e17231138e3e902 com.gnservice.beta
MalRhino
2990f396c120b33c492d02e771c9f1968239147acec13afc9f500acae271aa11 com.gnservice.beta
Comment by Lotem Finkelsteen, Head of Threat Intelligence at Check Point Software Technologies:
"We live in an age where cybercriminals do not have to hack into a bank to steal money. All a cyber criminal needs to do is understand the platforms used by banks and their respective pitfalls. There is a growing trend where cybercriminals are chasing institutional banking applications. This time, we detected cyberattacks against users of Brazil's No. 1 banking app.
The attack involved two malicious applications, which at one time could be found in the Google Play Store, but no longer.
The attackers presented a thin version, which performed an overlay when using the legal application and a complete version that has the ability to eventually occupy the entire banking application. We believe that these cyber attacks are a strong sign that the criminals in it tend to develop their activities around the android banking malware, with the aim of transferring victims' money to their own accounts. In a world where everything is done remotely because of Covid, we recommend that users immediately remove malicious applications from their mobile phones.
I also urge all users of banking applications to beware of banking malware that is embedded in mobile applications. "CPR will continue to monitor the latest technological trends and the way cybercriminals exploit them."





