Be careful if you use Google's web browser as hackers have found a new way of serving malware through Chrome. Security researchers have discovered a new scam using Chrome. Fraudsters ask users to download a "missing font" and instead serve malicious software.
The scam was first pointed out by Mahmoud Al-Qudsi from company ασφάλειας στον κυβερνοχώρο NeoSMART Technologies, η οποία δημοσίευσε λεπτομερώς την επίθεση στο blog her.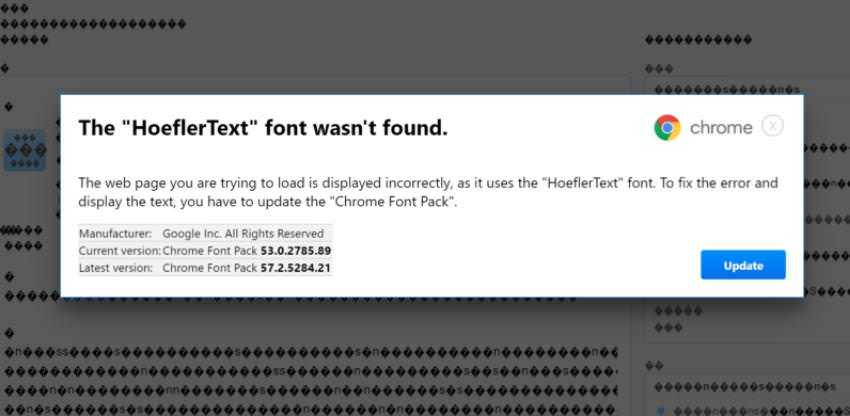
The investigator first noticed the trap when browsing a WordPress page that appeared to be infringed. Unlike other attacks, she seemed to be very masquerading.
The hackers used Javascript a lot to interfere with the rendering of the text, making it look like text that was incorrectly encoded. The hackers' script then asked users to fix the problem by updating the "Chrome font packages".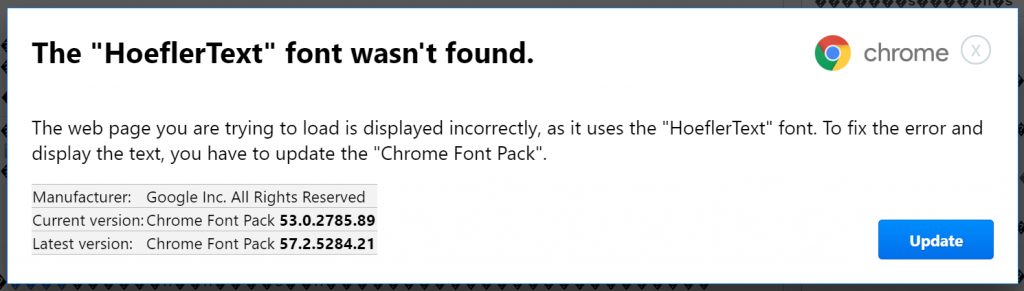
What makes the offensive especially sly is that the hacker or the hackers who designed it noticed too much the look: dialog was modeled to look exactly like real windows-alerts of Chrome.
According to NeoSMART Technologies, there are some "indicative signs" that could signal "bells" to careful users. One, the dialog box is hard-coded in the window that appears in version 53 of Chrome, which could raise suspicions among users using another version of the browser.
Additionally, while clicking "Update" you should download a file titled "v7.5.1.exe Chrome Font", which does not match what appears in the "Crome" window which states " Chrome_Font.exe. ”![]()
Researchers warn that Chróme still does not filter the file as malicious software like Windows Defender.
The security company ran the malicious software to VirusTotal, and currently only nine of 59 anti-virus scanners present in its database services detected the file as malicious.





