Severe security gap in Curiosity Rover! Canadian security researcher Yannick Formaggio discovered a major flaw in the VxWorks, the real-time operating system (RTOS) developed by Intel's Wind River subsidiary.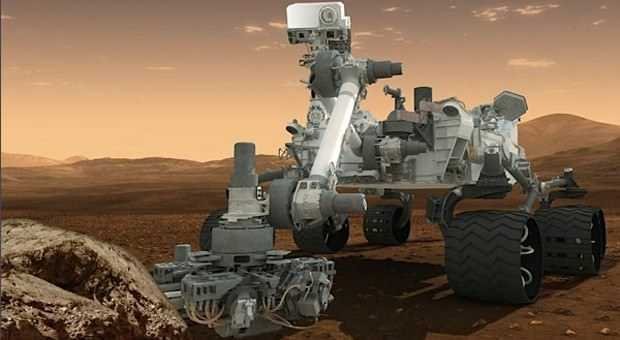
Speaking at the event 44CON last week, Formaggio he described in detail how an overflow method allows for remote code execution in the operating system.
Formaggio disclosed the flaw in the operating system, while acknowledging that Wind River did a very good job with the security parameters it implemented. But he said he had never thought about what might happen when a certification is found to be negative price.
Formaggio after discovery of the vulnerability, was able to create a software backdoor, which of course operational RTOSs try to avoid. Most real-time operating systems are considered extremely reliable and secure, since they are used in industrial equipment, airplanes and the Curiosity Rover that the Wind River says proudly that it uses its operating system.
Formaggio also found that the operating system contains vulnerabilities on the FTP server it uses.
The researcher states "it is prone to buffer overflow when access is at high speeds" and got stuck when it sent a "specially designed username and password".
Special OS versions 5.5 through 6.9.4.1 have problem, which means many millions of devices need an immediate fix.
Wind River has acknowledged the flaw and is already in the procedure providing updates to its customers.
The researcher said he would not publicly disclose the exploit “except if he is given express permission".
After the Curiosity Rover report, we can finally say that hacking has entered a space era!



