The new Have I Be Emotet service allows you to check if a domain or one address Your email was involved in Emotet spam.
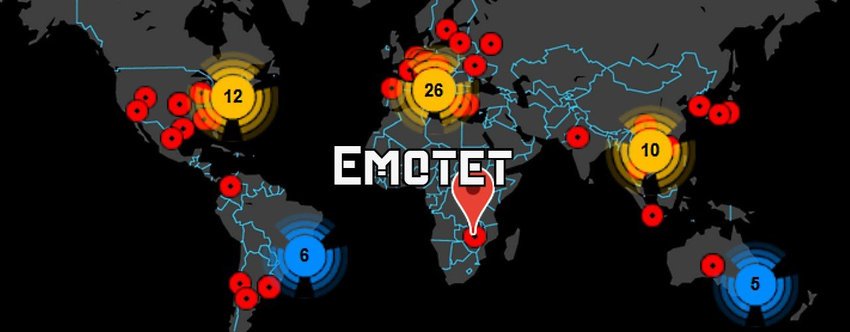
The Emotet is a malware infection, which spreads through spam messages emails that contain malicious Word or Excel documents attached. When the victim opens such a file and macros are enabled in Word or Excel, the Emotet trojan will be installed on their computer.
When infected, Emotet will steal the victim's email and relay it to attacker-controlled servers. These emails will then be used as future junk mail campaigns to make the malicious spam look legitimate.
Over time, the Emotet trojan will download and install other malicious programs, such as TrickBot and QakBot, onto the computer of an infected user. These trojans are known to lead to ransomware attacks by ransomware operators Ryuk, Conti and ProLock.
The Emonet trojan also steals e-bakning codes from the victim, which prompted the Cybercrime Prosecution will issue a warning to Greek internet users.
Today, the Italian cyber security company TG Soft, launched a new service called Have I Been Emotet, which lets you check if a domain or email address has been used as a sender or recipient of Emotet spam campaigns.
TG Soft reports that their database consists of controlled outgoing emails created by Emotet between August and September 23, 2020. During this period, they have collected over 2,1 million email addresses from approximately 700.000 outgoing emails.
To use the service, you can simply enter a domain or email address and it will let you know how many times the email address or domain has been used as the sender or recipient of an email.
For example, using this service, we can see that domain Microsoft.com, was used in recent Emotet campaigns and that the company received Emotet spam forty-two times.
If you use this service and find that your email address or domain has been used as a recipient, this does not necessarily mean that you are infected. To be infected, a user would have to open email attachments and enable macros before installation of malware.
On the other hand, if your domain has users listed as a “REAL” sender, then it is likely that one of your email domain users was infected and a thorough investigation of computers you.





