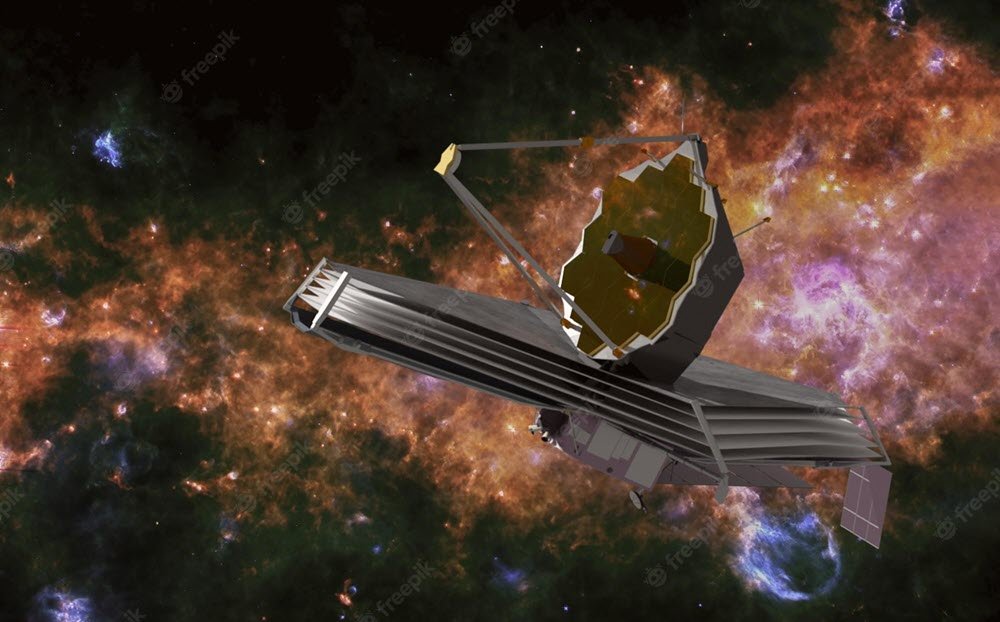
In July 2022, NASA he published the first images taken by the James Webb Telescope. Among them was one showing a galaxy cluster called SMACS 0723.
At the time, NASA called it the deepest infrared image of the universe, and the thousands of galaxies in the image were touted as the faintest objects ever observed in the infrared region of the electromagnetic spectrum.
However, the same image seems to have been "weaponized" by hackers after they managed to add a malicious software inside it.
Security firm Securonix researchers describe a malicious campaign software called GO#WEBBFUSCATOR, and uses the famous click to seed malware on the Webb telescope image. The biggest advantage comes from using the Golang programming language because it is natively compatible with multiples platforms, πράγμα που σημαίνει ότι ο ίδιος κακόβουλος κώδικας μπορεί να αναπτυχθεί σε διαφορετικές πλατφόρμες-στόχους Linux, macOS και Windows.
It all starts with an email containing a malicious Office attachment titled (in Securonix's case, at least) Geos-Rates.docx. Document metadata can trigger a file download.
Once the document is opened, the auto-download scopt stores the malware, which then runs to perform its intended task. The code passed to the system then downloads a jpg image file that looks like the image taken by the Webb telescope.
However, the analysis of the image using with some program processingof text reveals that it is actually hiding a Base64 code that is also the payload, ready to execute and cause damage.
What really raises the threat level here is the fact that the malicious Base64 code gets past all protection systems without triggering any system-level alarm, Securonix reports. Once the payload is executed, it connects the target system to a remote server, leaving the computer at the mercy of hackers. Once a connection is established, encrypted data packets are sent to the hacker.
Securonix states:
“This practice can be used to create encrypted command channels and control, or to extract sensitive data. In addition, the malware tricks the Windows registry's Run key into becoming persistent, meaning that a reboot will not remove the malicious code.





