In an ever-changing cybersecurity environment, organizations must adapt their security to ensure better. As the environment becomes more complex, open XDR has emerged as an advanced detection and response tool that companies should consider.
In this article, we'll break down exactly what it is openXDR, what kind of benefits you can expect and whether this technology is right for your business.

What is XDR?
XDR stands for eXtended Detection and Response and combines traditional detection and response with network traffic analysis and other telemetry sources from traditional security information and event management (SIEM) systems.
By leveraging telemetry and security data from multiple security sources, including traditional endpoint detection and response tools, organizations are better equipped to detect unusual behavior and understand how and if a breach has occurred.
XDR Options:
The solutions XDRs vary by vendor, but many leverage analytics and data from various back-end and front-end components. These include:
- firewalls (virtual and on-premise)
- Network data
- Endpoint data
- Cloud Services
- Email systems
- Endpoint detection and response (EDR) tools
- Identity and access management solutions
- Intrusion and prevention systems
- Cloud access security brokers (CASB)
Every XDR solution is different, and if you're in the market, you should carefully consider how the tool will integrate into your environment.
What is Open XDR?
Open XDR, also referred to as everything XDR, is a vendor-agnostic XDR approach that integrates with the customer's existing security environment, incorporating all of their security tools as part of data collection and analysis. It is called “Open” XDR because it takes an open approach, gathering data from all sources. The traditional or XDR, on the other hand, offers an all-in-one platform and does not integrate third-party vendors.
Open XDR is also referred to as hybrid XDR (to avoid open source associations). As a relatively new solution, Open XDR varies widely among the different vendors that offer this approach.
How does Open XDR work?
Open XDR, unlike traditional XDR solutions that only integrate data from a vendor's native technology function, is designed to ingest security data from all available sources. These solutions often use AI-powered data analysis to extract the right information about security.
Open XDR leverages an organization's existing EDR or SIEM tool, aggregating data from on-prem, cloud, and other hybrid sources. It is not designed to replace any particular technology but instead sits on top of a company's existing security stack, centralizing data collection and analysis.
Five advantages of Open XDR:
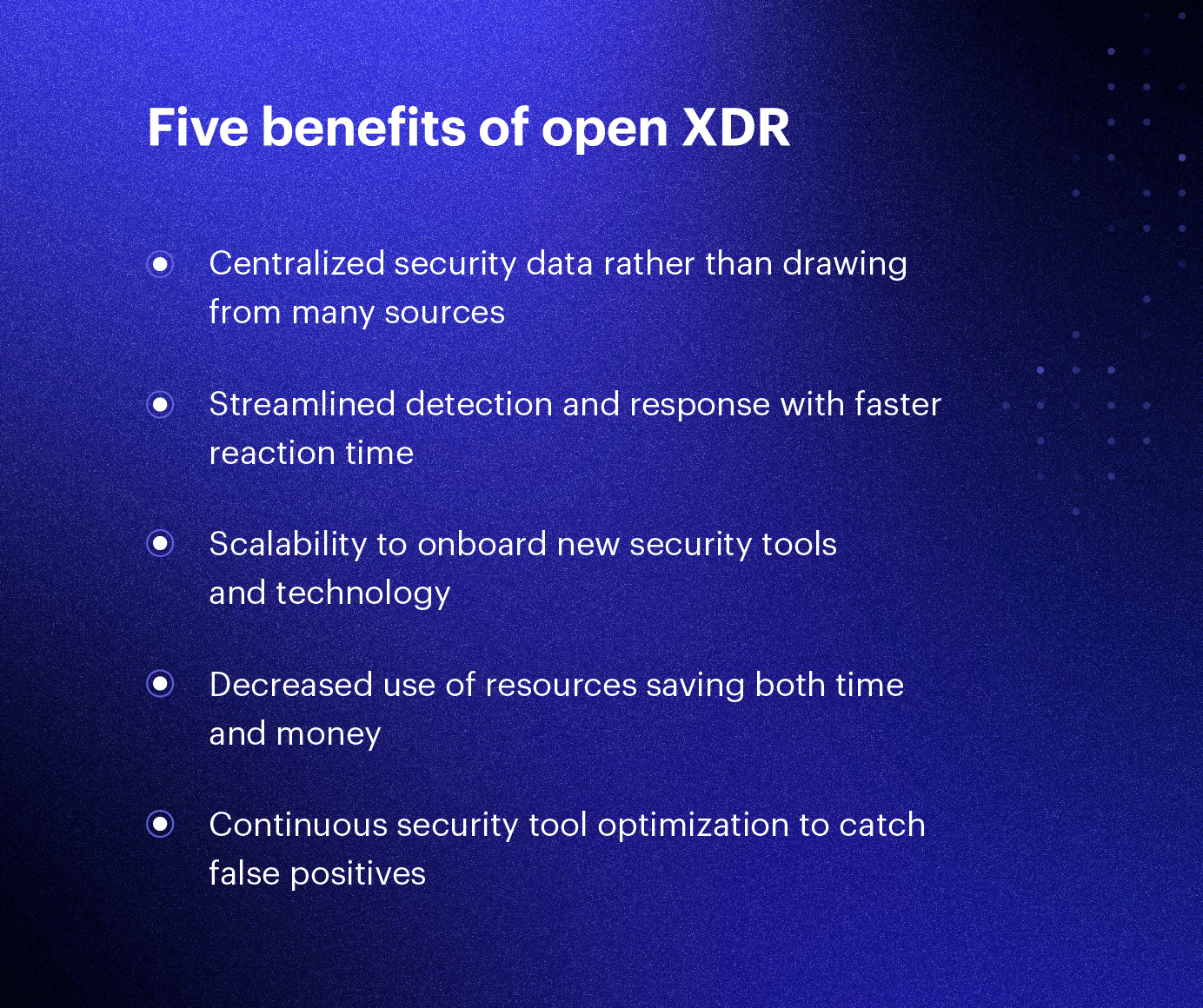
Open XDR solutions are designed to centralize, streamline and centralize the data collection process, enabling organizations to save costs and improve their security intelligence. See what organizations can expect.
1.Centralized security data
Open XDR is designed to aggregate data from all security sources, providing organizations with a single security data platform instead of having to manually aggregate data from different sources.
2.Streamlined detection and response
Because information can be found in a single source, security analysts can easily identify a potential attacker or suspicious behavior that may be a sign of a breach. This makes reaction time much faster, reducing risk exposure and reducing the damage an intrusion can do.
3.Scalability is possible
The nature of allows you to integrate new security tools and technologies and easily integrate and connect them with the open XDR solution. As your security department scales and new technology is introduced, this is a key benefit worth highlighting.
4. Reduced resource usage
A can free up time and money by simplifying the supplier management process. By having security analysts have a single point of access through XDR, a company can save valuable resources.
5. Continuous optimization of security tools
Because an open XDR inputs real-time security data, you can see if an existing tool stops collecting data or produces false positives. This helps ensure that your technology is working and being optimized on an ongoing basis.
Open XDR vs. native XDR: which solution is best?
Not all organizations should use an open XDR, and the same goes for more traditional, native XDR solutions. Here are some of the key features organizations should consider when choosing between open XDR or native XDR.
When should you choose Open XDR?
open XDR is the best solution for an organization with a wide security scope and a well-equipped security environment. This can include EDR and SIEM solutions. In this case, an open XDR fixes what is probably a challenge for the service – managing multiple vendors and security data sources.
When should you choose native XDR?
The open XDR option is only as effective as the data sources that feed it. If your security environment is small or you have only a few data sources, then a native XDR solution can help you expand your current technology activity by introducing new sources of security data.
Open XDR vs. EDR and SIEM
You may be trying to choose between an open XDR solution and an EDR or SIEM solution, but these options are quite different and you may find yourself with the wrong choice for your organization.
An EDR or SIEM are different kinds of security sources that help an organization detect if its network has been compromised. To put it simply, the differences between the two are mainly where the data comes from.
As the name suggests, EDRs collect information from various endpoints on a network, usually in the form of an agent installed on a machine. EDRs take a device-based approach – collecting, correlating and potentially alerting to unusual activity coming from a specific device.
These triggers can be connections to unusual IP addresses, the device performing strange DNS lookups, access or changes to various registry keys, and new, unexpected, or unusual system calls, processes, or application behavior.
Unlike traditional antivirus solutions, EDRs use and to detect malicious behavior on a specific device. EDRs then use this information to correlate or find threats on other devices running the EDR agent.
However, EDRs often lack the larger context of what is happening in the network, perimeter firewalls, or , in Active Directory, or on any device on which an agent cannot be installed.
On the other hand, a SIEM is a bit more extensive and not just limited to endpoints. It collects information from firewalls, servers, logs, and potentially from the EDR sources themselves. Many SIEM tools offer possibilities search logs to find threats, as well as ready-made correlation rules based on the data they are able to collect.
Open XDR works best when it aggregates data from multiple sources, such as an EDR and a SIEM tool. This is why we recommend that organizations consider an Open XDR solution only after their environment requires it, rather than jumping right into Open XDR.





