Emotet botnet has started using a new malicious attachment that pretends to be a message from Windows Update telling you to upgrade Word.
Emotet is one malware που εξαπλώνεται μέσω ανεπιθύμητων μηνυμάτων ηλεκτρονικού ταχυδρομείου που περιέχουν κακόβουλα έγγραφα Word ή Excel. Αυτά τα έγγραφα χρησιμοποιούν μακροεντολές για την λήψη και installation by Emotet Trojan στον υπολογιστή του θύματος. Το trojan χρησιμοποιεί τον υπολογιστή για την αποστολή ανεπιθύμητων μηνυμάτων ηλεκτρονικού ταχυδρομείου και τελικά οδηγεί σε επίθεση ransomware στο δίκτυο του θύματος.
After a brief hiatus, the malware Emotet returned to service on October 14 and began sending malicious spam content worldwide.
These spam campaigns pretend to be invoices, shipping information, information about COVID-19, information about President Trump's health, biographics or purchase orders.
These junk e-mail attachments include malicious Word (.doc) attachments or download links.
When opened, these attachments will prompt the user to "Enable Content" to run malicious macros that will install the malicious Emotet software on the computer.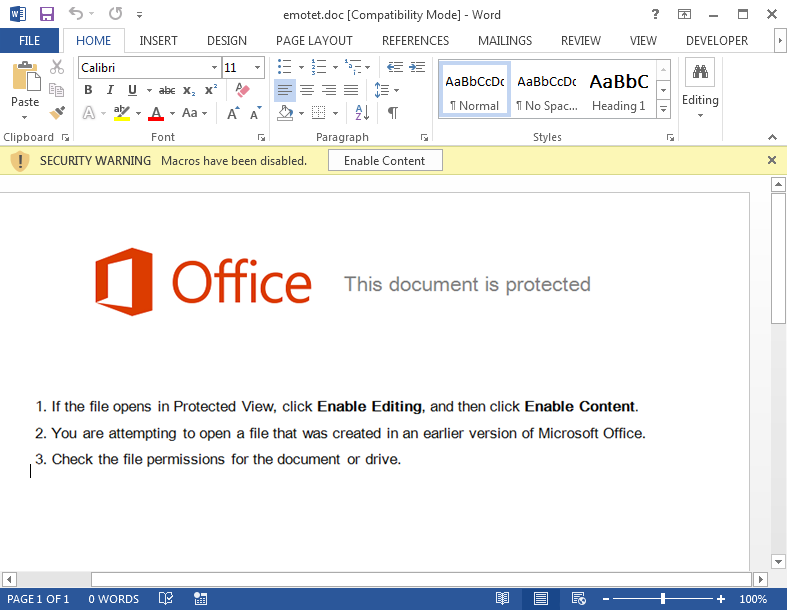
Upon its return, Emotet released a new template that pretends to be a message from Windows Update stating that Microsoft Word should be updated before viewing the document.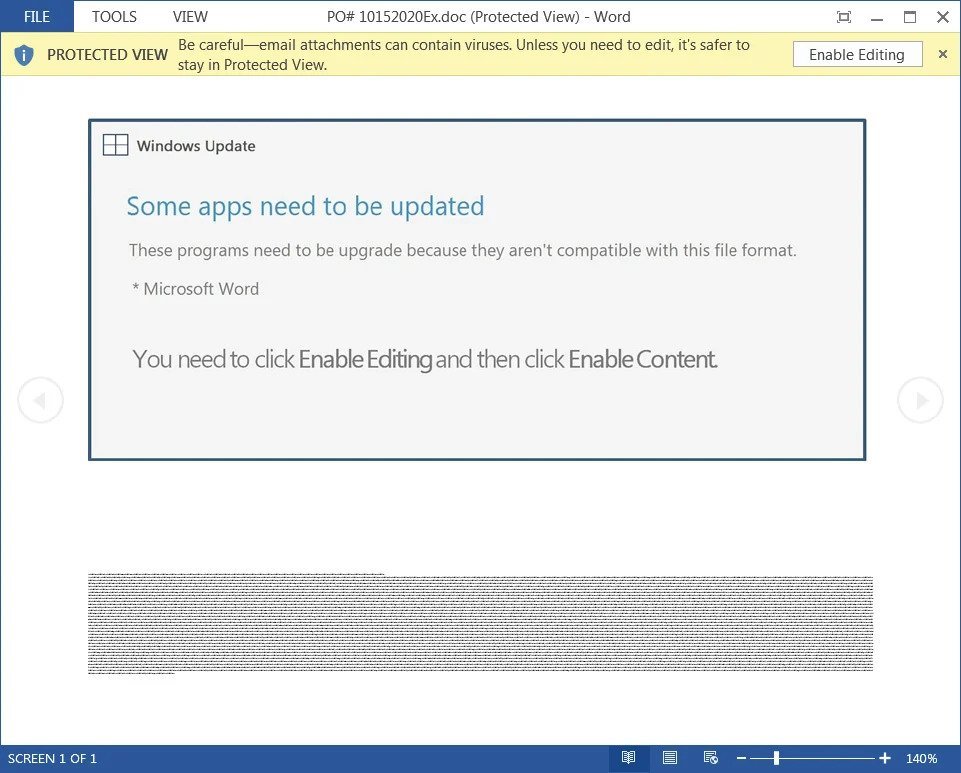
To update Word, the message tells the user to click the Enable Editing and Enable Content buttons, which will trigger malicious macros,
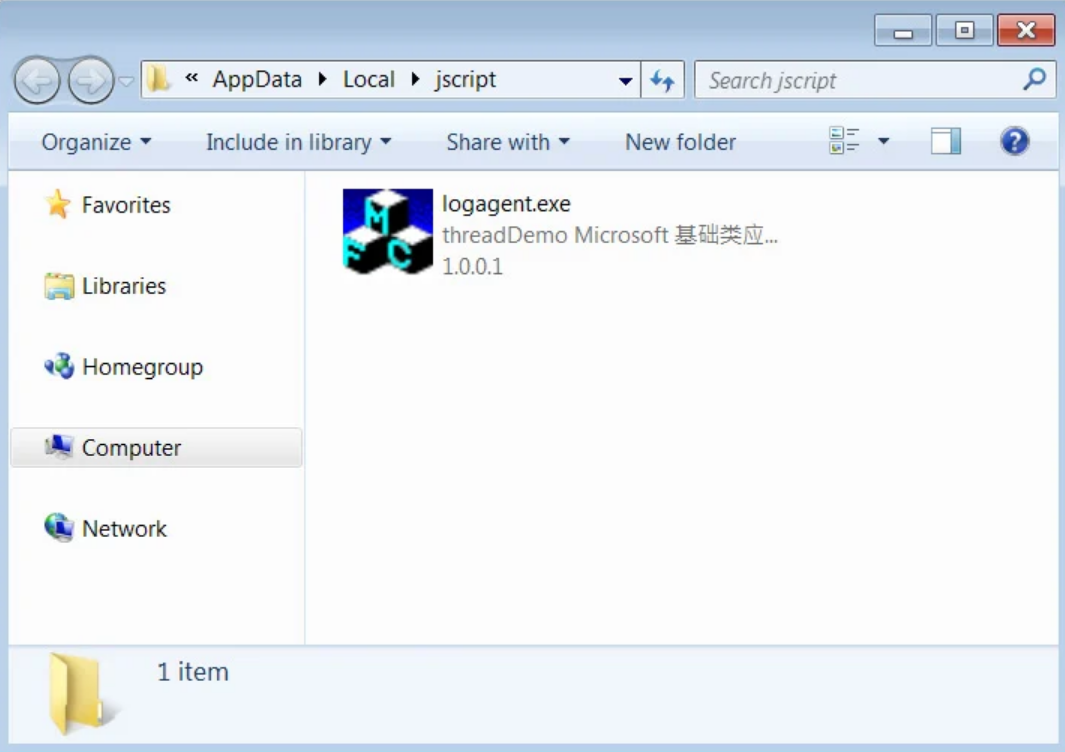
These malicious macros will download and install the malicious Emotet software onto the victim's computer, as shown below.
Emotet is now considered to be the most common malware. It is also particularly dangerous as it installs other malicious programs such as Trickbot and QBot on the victim's computer.
While TrickBot and QBot have their own malicious activity, such as stealing stored passwords accesss, banking information and various other information, also commonly lead to Conti (TrickBot) or ProLock (QBot) ransomware attacks.
So it is vital that you recognize the malicious document templates used by Emotet so that you do not accidentally become infected.





