The EncryptedRegView είναι ένα εργαλείο για τα Windows που ανιχνεύει το Μητρώο του συστήματός σας ή το μητρώο που υπάρχει αποθηκευμένο σε ένα εξωτερικό σκληρό δίσκο και αναζητά δεδομένα κρυπτογραφημένα με DPAPI (Data Protection API).
When it detects encrypted data in register, tries to decrypt them, then displays the decrypted data in the main window of EncryptedRegView. With this tool, you can find passwords and other confidential data stored in the registry from various Microsoft products as well as third-party applications.
Works well on Windows XP up to Windows 10 and supports 32 and 64-bit systems.
EncryptedRegView does not require installation or additional DLL files. To use it, simply run the executable archive EncryptedRegView.exe.
The "Advanced Options" window will open, allowing you to select the registry scan settings.
By default, EncryptedRegView offers the ability to scan your current system and current user registry without using Run As Administrator.
If you check "Run as administrator to decrypt protected data", EncryptedRegView will run with Administrator privileges and decrypt protected system data that cannot be decrypted with simple user privileges.
Press 'OK' and EncryptedRegView will start scanning the Registry and looking for encrypted DPAPI data.
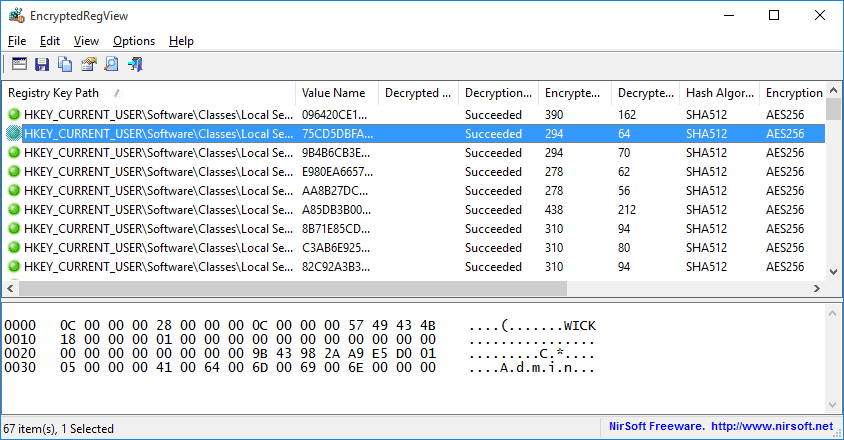
When it detects encrypted data, it tries to decrypt it. When it successfully decrypts them, it will show 'Succeeded' in the 'Decryption Result' column with a green icon.
You can see the entire decrypted information in Hex-Dump format in the lower part of the window by selecting the desired item in the upper part of the window. If the decrypted information is a string, it is also displayed in the upper part of the window in the 'Decrypted Value' column.
If the decryption process fails, 'Failed' will be displayed in the 'Decryption Result' column with a red icon.
EncryptedRegView also allows you to scan the registry of an external hard drive that is connected to your computer.
To scan the registry on external hard drive easily, select the option 'Scan the Registry of external drive' then select or type the path of the external drive. Then click the 'Automatic Fill' button.
EncryptedRegView will automatically discover the correct folders on the external drive (Registry Hives Folder, User registry file, User classes registry file, Protect Folders). Note that EncryptedRegView selects the user profile (c:\users\[Profile Name]) that was last used since the modification time. So if you want another user you will have to manually add the route.
Also, to decrypt a user's encrypted data on an external drive (usually stored under the HKEY_CURRENT_USER key), you must provide the correct user login password.
You do not need to have a password to decrypt encrypted system data on an external drive (usually stored under the HKEY_LOCAL_MACHINE key).
Beware, many times its tools Nirsoft show false positives in known virus detection software.





