The researchers of ESET analyzed malware samples – detected by ESET as Win32/Industroyer – capable of attacking power supply infrastructure. 
There is a high probability that this particular malware is involved in the attack against Ukraine's electricity grid in December 2016, leading to a one-hour blackout in the country's capital, Kyiv.
"The attack on the Ukrainian electricity grid will have to alert everyone who is responsible for the security of critical systems at the global level, warns Anton Cherepanov, Senior Malware Researcher of ESET.
ESET researchers have discovered that Industroyer can directly control electrical substation switches and circuit breakers. It uses industrial communications protocols used worldwide for power supply, transport control systems and other critical infrastructures. Possible impacts may range from a single power failure, which will result in a series of failures, even to severe damage to the equipment.
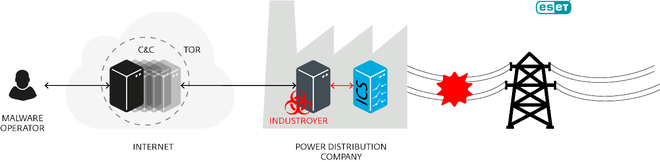
Illustration of operation of Industroyer from ESET
"Industroyer's ability to remain in the system and be able to directly interfere with the operation of industrial infrastructure makes it the most dangerous malware threat to industrial control systems since the famous Stuxnet, which was able to attack the program Iran's nuclear program and was discovered in 2010," says Anton Cherepanov.
Detailed information about malware, as well as IOC (Indicators of Compromise) indicators, can be found in the relevant article and an extensive whitepaper on ESET's blog, WeLiveSecurity.com.





