Often, as cyber warriors, we need to check whether our systems or the systems of others are vulnerable to various known vulnerabilities and attacks. Whether it's pentesters, security engineers or other malicious actors, this information can be critical to the success of this mission.
There are several other sites that offer some information in this key area, such as Shodan and Censys, but netlas.io is probably the best! To be honest, if you're not using netlas.io, you're missing out on one of the best resources on the internetnetwork.
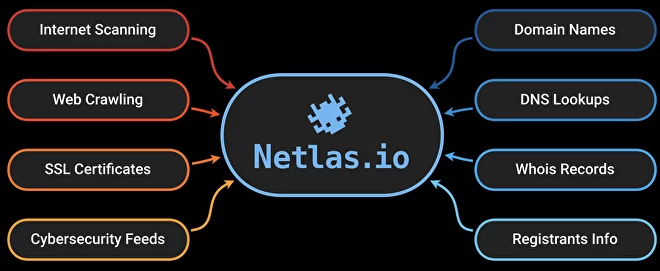
Netlas.io can be used in at least 5 different use cases such as,
-
OSINT
-
Offensive Security
-
Defensive Security
-
Leads and contacts
-
MarketingResearch
In this guide, we will focus on using netlas.io as an offensive security tool in the context of penetration testing. The first steps of a pentest, including the identification and formation of a surface attacks, it's faster and easier with Netlas.io. Use whois and DNS lookup option including A, NS, PTR, MX and SPF records to configure network perimeter, scaling and performance.
Step #1: Login to netlas.io
The first step is to navigate to netlas.io and create an account.
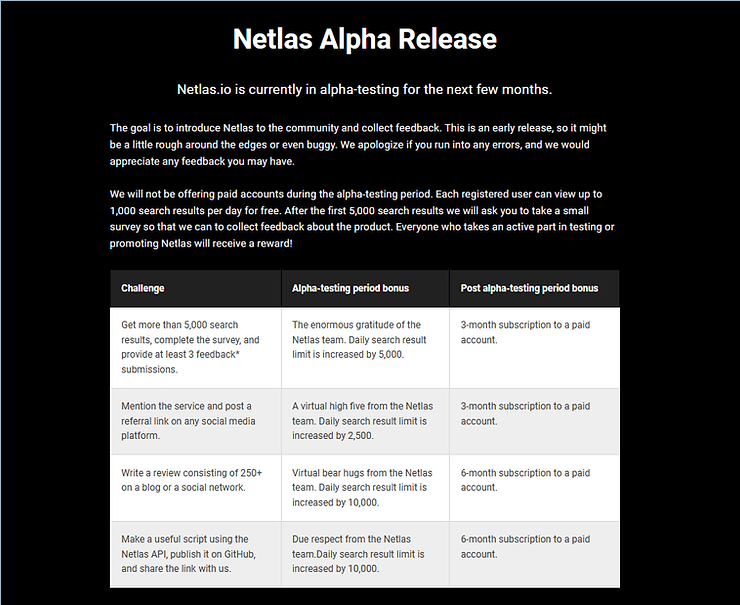
Since netlas.io is in its early stage of development, it offers multiple free accounts.
Step #2: Basic search
Like many other search engines, you can create a search query with search fields and search phrases separated by colons (:). You can search by IP address, host, whois and many other fields. Additionally, you can search by subfields using the field name followed by the subfield name separated by a period.
field.subfield:value
So if you were looking for apache web servers you could type,
tag.name:apache
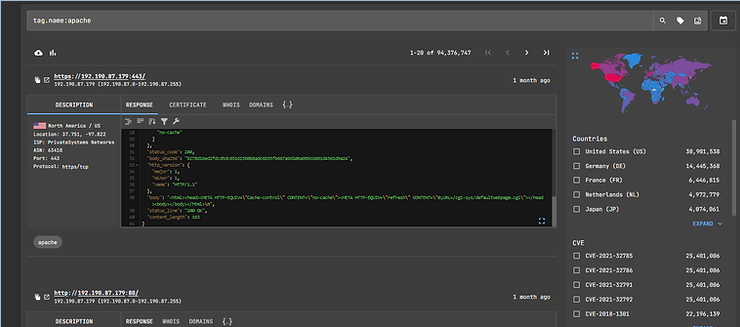
As you can see below, netlas.io was able to find 94 millions servers using apache.
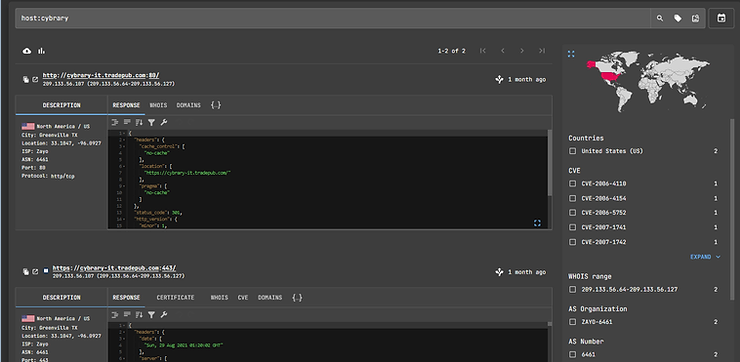
Each entry has a response tab, a certificates tab, a Whois tab, and a domains tab. When we click on the domains tab, all the domains hosted on the specific IP address are displayed.

We can also search by host using the syntax,
host: cybrary
Step #3: Search for vulnerabilities
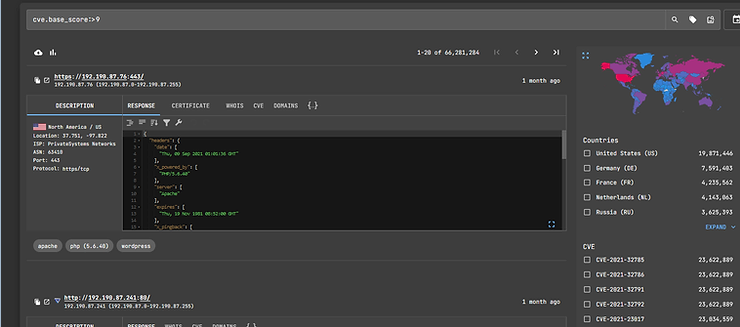
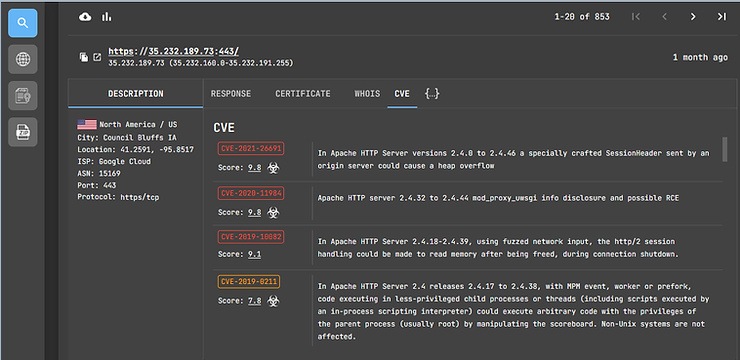
One of the beauties of this site is the ability to search by vulnerability and cve. For example, if I wanted to see all sites with CVE vulnerabilities greater than 9, I could enter the search,
cve.base_score:>9
If I wanted to find all SMB-enabled sites, I could enter the search,
smb:*
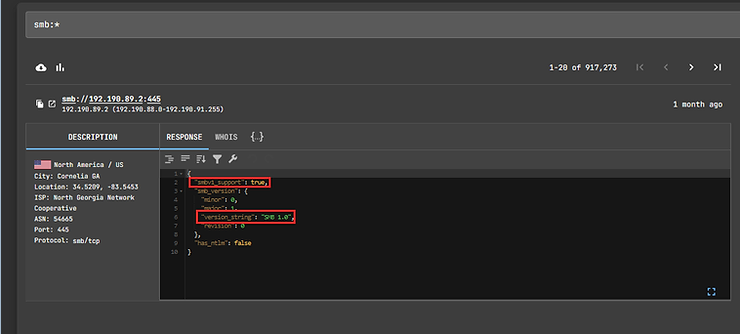
Note that in the response field we have a subfield “smbv1_support". We can use this subfield to find all sites with faulty and vulnerable SMBv1 (true) enabled.
smb.smbv1_support:true
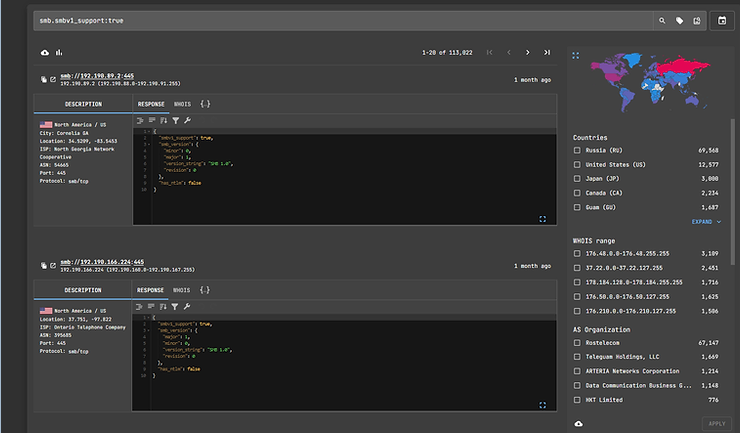
Note that over 113.000 sites were found with this outdated and flawed version of SMB.
We can also search for sites that have a known public exploit using the search,
cve.has_exploit:*
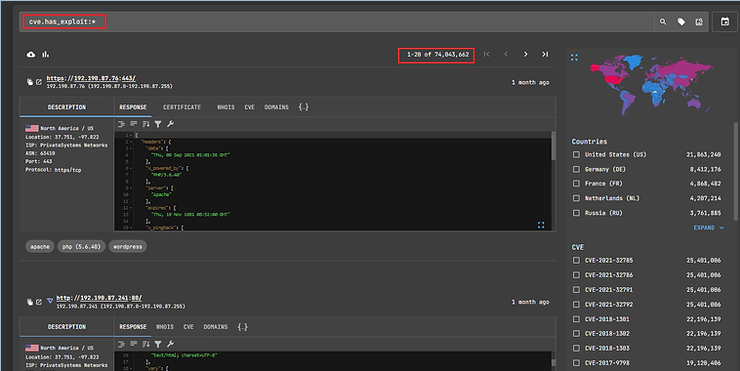
This search reveals that there are over 74 million websites that are potentially vulnerable to some known public exploit. At its right end screens you can see the CVEs of the vulnerabilities found. We can then click on the tab CVE above the listing and netlas.io will list all known vulnerabilities. Note that the website below has 3 vulnerabilities with severity above 9!
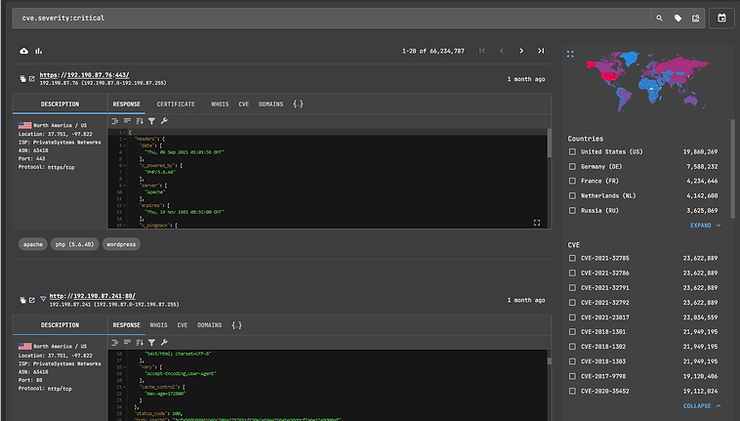
We can also search based on the severity level of known vulnerabilities. If we wanted to see all the sites with a degree of seriousness”critical", we use the search term,
cve.severity:critical
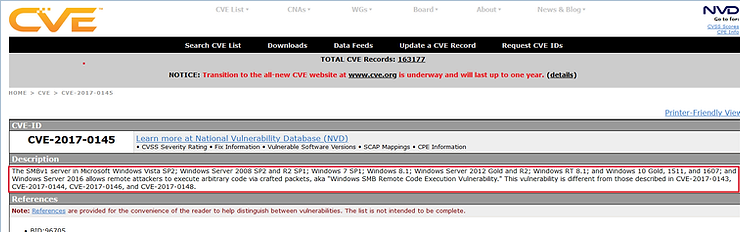
If we wanted to find all websites that are vulnerable to the infamous EternalBlue (remote SMB code execution) exploit, we can search by CVE name,
cve.name: CVE-2017-0145
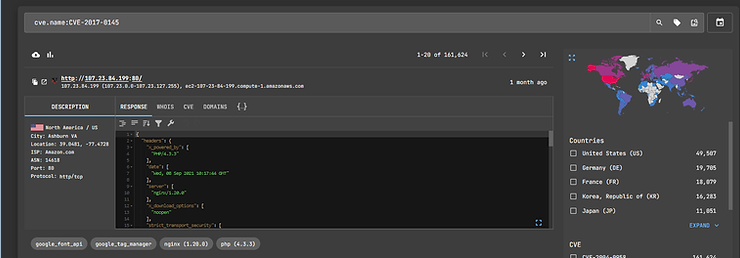
Over 161 thousand websites are still vulnerable to this exploit. Just for the sake of it record, here is the list of CVEs in NVD.
Step #4 Use logical operators
As with other sites similar to netlas.io, you can use logical operators to narrow your search. You can use AND, OR ή NOT (&&, ||, !, respectively). The default operator is the AND.
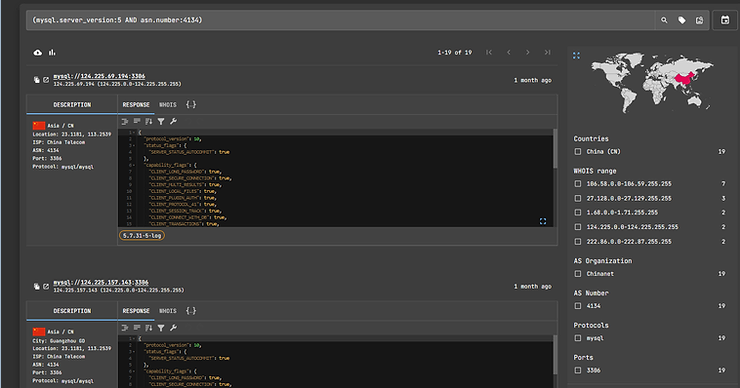
So if you are looking for sites running the outdated and vulnerable MySQL v5 sites with ASN number 4134 you could create a query like,
mysql.server.version:5 and asn.number:4134
Netlas.io also allows you to search using regular expressions (regex) and wildcards (* and ?).
Summary
If you are into pentest or OSINT, netlas.io is a must have tool. It can save you hours of searching for key information and vulnerabilities.
I hope it goes without saying that no tool is perfect and that goes for netlas.io as well. That's why you need to familiarize yourself with a wide variety of tools and then use the best tool for the job or situation.





