Hackers use a software called Facebook Email Search v1.0 to reveal millions of Facebook user email addresses, even if the addresses are private.
This user data, combined with the 553 million phone numbers that leaked from Facebook a few weeks ago, can help hackers access accounts or create a database with personal information of Facebook users.
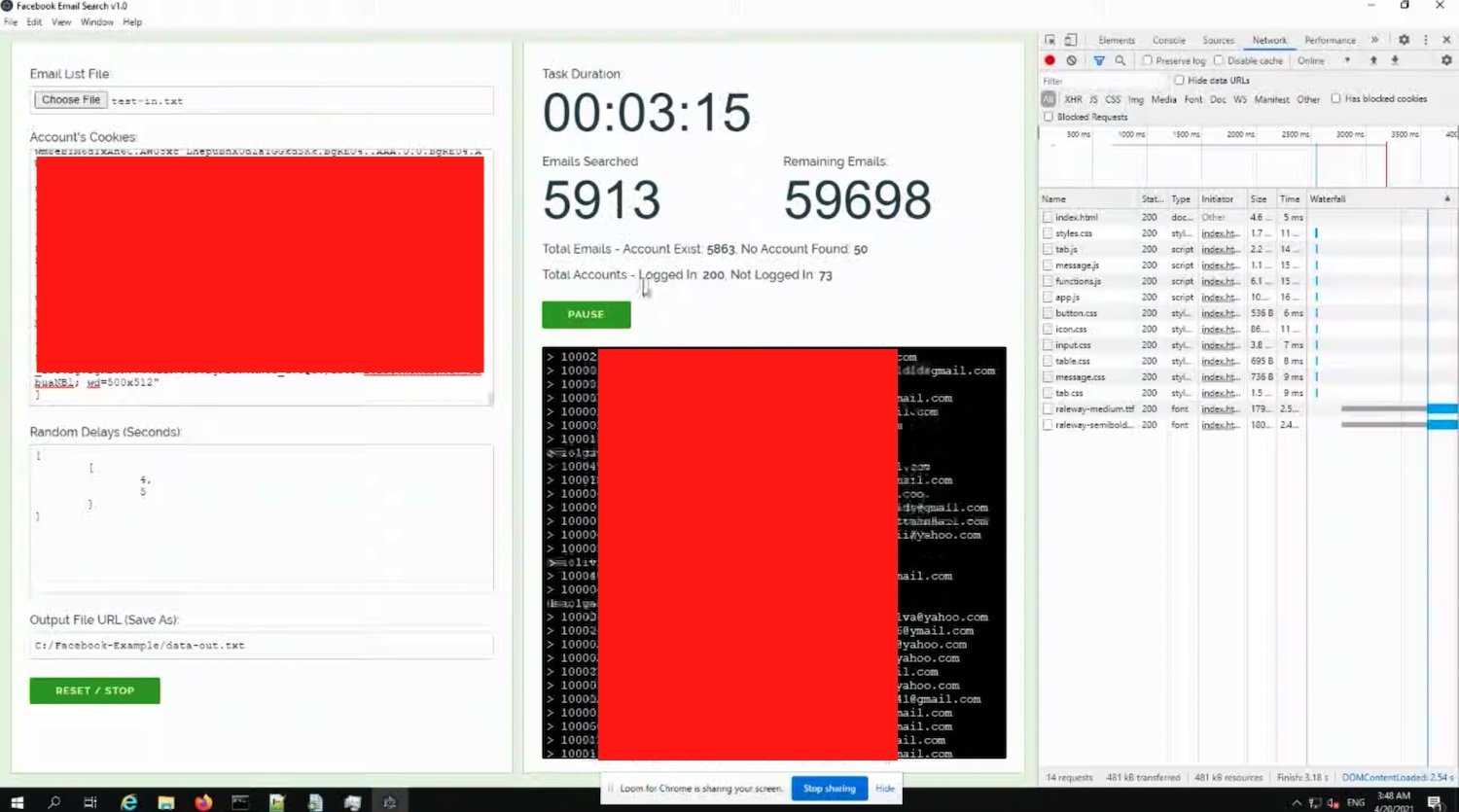
Facebook Email Search v1.0 exploits a front-end vulnerability on the Facebook website. Automatically associates user IDs with the relevant address ηλεκτρονικού ταχυδρομείου , επιτρέποντας σε έναν μόνο hacker provide about 5 million email addresses a day. Facebook says it fixed an almost identical vulnerability earlier this year.
In a conversation with Ars Technica, an anonymous researcher claims to have sent the vulnerability to Facebook, but the larger social network chose to ignore the matter. Facebook told the researcher that it "does not consider [the vulnerability] important enough to fix," despite the fact that it is a clear security risk and infringement of the privacy of its users.
Facebook has not only ignored the vulnerability, but is actively encouraging PR representatives to downgrade and "normalize" data breaches. Read an internal Facebook email which was accidentally sent to a Data News reporter after the April 5 leak.
Hundreds of millions of Facebook users saw their data travel online this month due to two separate social network vulnerabilities. In the face of this significant amount of data, Facebook hopes to "normalize" the phenomenon and argues that we should learn to live with data leaks. For a site that is obsessed with collecting data from its users, Facebook negligence causes.
Facebook now says it “accidentally closed this report errorbefore routing it to the appropriate team" and that it is currently investigating the problem. We don't know when the company will fix this particular security hole or how many accounts have been affected.





